Android 13, the new version released by Google last week. The new Android 13 brings in various security upgrades and particularly Google has ‘restricted’’ the use of Accessibility Service in the new version.
However, Threat Fabric says they have successfully overcome these limitations and managed to avoid the new restrictions added in the new OS version.
Android 13’s Restricted Setting Feature
An Accessibility Service assists users with disabilities in using Android devices and apps. It is a long-running privileged service that helps users process information on the screen and lets them interact meaningfully with a device.
The beta version of Android 13 introduces a new approach to enabling AccessibilityService of applications installed from third-party sources. This new option is called “restricted settings”, which include AccessibilityService.
In earlier versions of Android, the malware found its way inside the devices or dropper apps available on the Play Store, which masquerade as legitimate apps. Therefore when the user installs such malware apps, it will prompt users to grant access to dangerous activities and drop the malicious payloads by abusing Accessibility Service privileges.
ThreatFabric researchers’ illustrated two proof-of-concept applications, one behaving like the droppers, while the second uses a different technique with a slight change in the installation process. Researchers managed to avoid the restricted settings in the second PoC application.

Researchers at Threat Fabric have spotted a previously undocumented Android dropper trojan that’s currently in development.
“This new malware tries to abuse devices using a novel technique, not seen before in Android malware, to spread the extremely dangerous Xenomorph banking trojan, allowing criminals to perform On-Device Fraud on victim’s devices,” ThreatFabric
Dubbed ‘Bugdrop’ the first malware trying to circumvent Google’s security Controls. It is designed to defeat new features introduced in the upcoming version of Android that aims to make it difficult for malware to request Accessibility Services privileges from victims.
This dropper features code similar to Brox, a freely distributed malware development tutorial project circulating on hacker forums, but with a modification in one string of the installer function.
“What drew our attention is the presence in the Smali code of the string “com.example.android.apis.content.SESSION_API_PACKAGE_INSTALLED,” explains Threat Fabric.
“This string, which is not present in the original Brox code, corresponds to the action required by intents to create an installation process by session.”
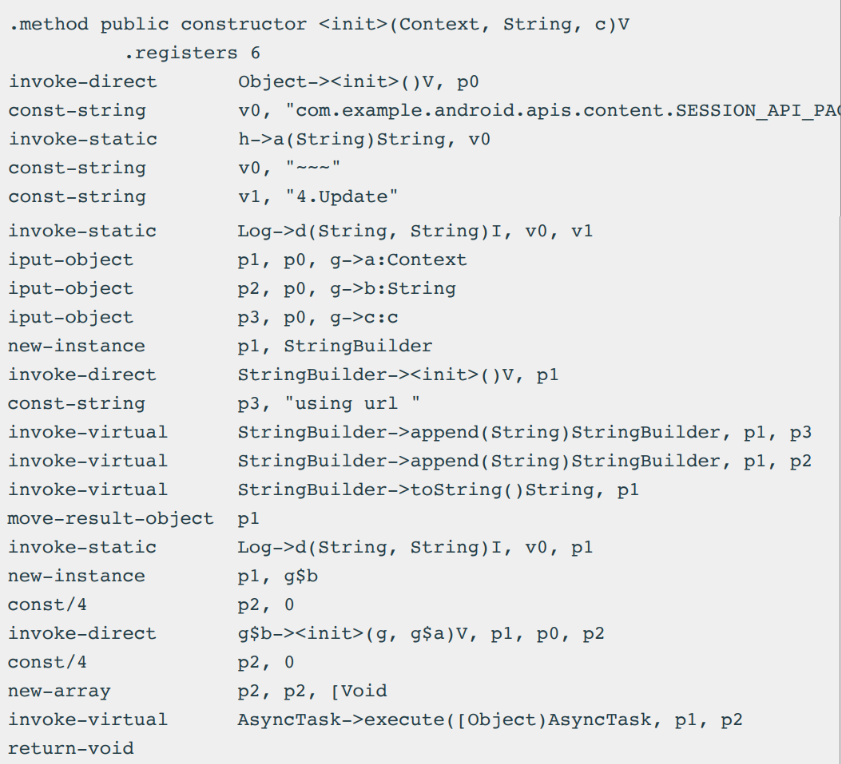
Google introduced the “restricted setting” feature, which blocks side-loaded applications from requesting Accessibility Services privileges, limiting this kind of request to applications installed with a session-based API.
Mitigation
The company says “To realize the real impact and prevent losses a proper solution should be in place to gain visibility on the malware infecting customers’ devices”.
Therefore, appropriate on-device detection of malware also helps to gain visibility on distribution channels and proactively notify customers about new distribution campaigns to raise their awareness.
Continuous authentication based on behavioral biometrics is a great source of Ti-based risk score for every account and makes fraud detection and prevention easier for financial organizations.
Also Read: Download Free Secure Web Filtering – E-book










.webp)