

Cybersecurity enthusiasts and IT administrators worldwide are voicing concerns over a newly discovered vulnerability in AnyDesk that could lead to local privilege escalation (LPE).
The vulnerability, identified as CVE-2024-12754 and coordinated by Trend Micro’s Zero Day Initiative, allows attackers to weaponize Windows background images for escalating permissions on Windows systems.
Discovered by security researcher Naor Hodorov, the flaw lies in the way the AnyDesk service handles background images during remote sessions.
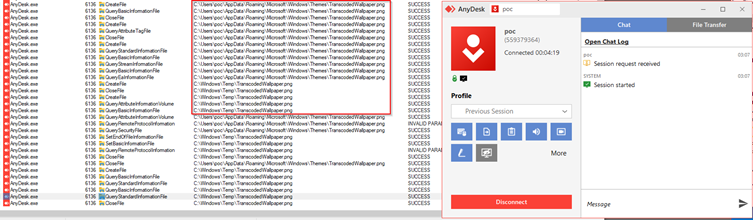
Specifically, when a session is initiated, AnyDesk copies the user’s background image into the C:\Windows\Temp directory using NT AUTHORITY\SYSTEM privileges.

Here’s the twist: A low-privileged user can manipulate this file-copy operation to gain access to otherwise restricted files and, ultimately, escalate their privileges.
By carefully pre-creating a target file in C:\Windows\Temp and exploiting file ownership inheritance behaviors, the attacker can execute an arbitrary file read or copy operation.
To exploit this vulnerability for privilege escalation, the attacker follows these steps:
What makes this vulnerability dangerous is its potential simplicity. AnyDesk, a popular remote administration tool used by millions worldwide, is installed on enterprise and personal devices alike.
While the complexity of the attack chain may deter casual attackers, skilled adversaries could weaponize this for more sophisticated breaches.
The vulnerability was responsibly disclosed to AnyDesk Software GmbH on July 24, 2024, with public disclosure coordinated for December 19, 2024.
The credit for this discovery goes to Naor Hodorov, whose findings were facilitated by Trend Micro’s Zero Day Initiative.
Until a patch is released, users and administrators are urged to:
As organizations increasingly rely on remote access tools, this vulnerability serves as a stark reminder of the importance of regular security audits and timely patching.
Investigate Real-World Malicious Links & Phishing Attacks With Threat Intelligence Lookup - Try for Free
A new project has exposed a critical attack vector that exploits protocol vulnerabilities to disrupt…
A threat actor known as #LongNight has reportedly put up for sale remote code execution…
Ivanti disclosed two critical vulnerabilities, identified as CVE-2025-4427 and CVE-2025-4428, affecting Ivanti Endpoint Manager Mobile…
Hackers are increasingly targeting macOS users with malicious clones of Ledger Live, the popular application…
The European Union has escalated its response to Russia’s ongoing campaign of hybrid threats, announcing…
Venice.ai has rapidly emerged as a disruptive force in the AI landscape, positioning itself as…