

The malicious Southeast Asian APT group known as OceanLotus (APT32) has been implicated in a sophisticated attack that compromises the privacy of cybersecurity professionals.
A recent investigation by the ThreatBook Research and Response Team revealed that a popular privilege escalation tool utilized by cybersecurity experts had been backdoored, leading to significant data breaches and identity leaks.
The attack, which was first identified in November 2024, involved the release of a Cobalt Strike exploit plugin embedded with a Trojan onto GitHub.

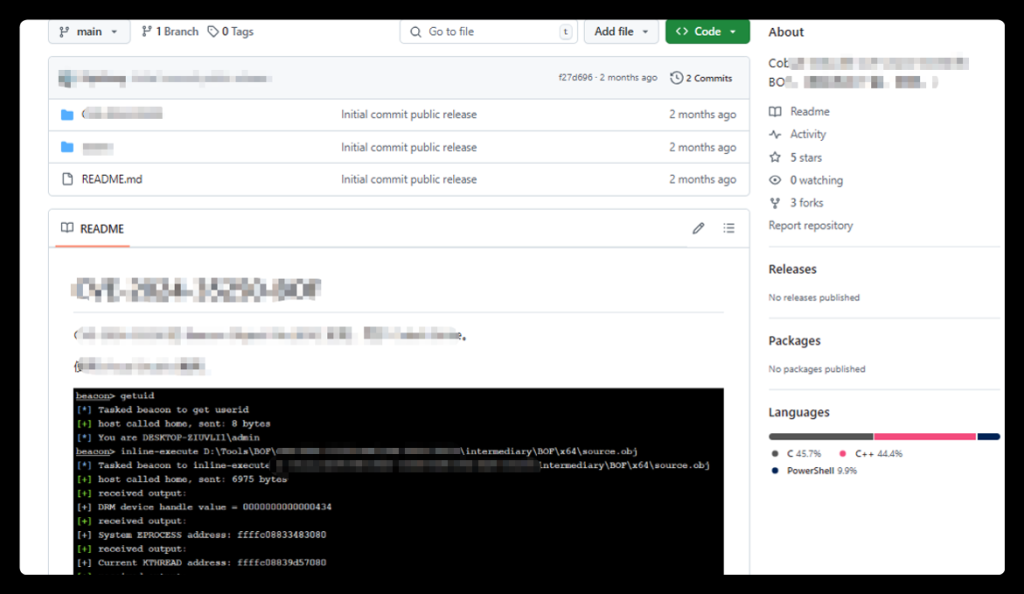
The attackers employed a novel tactic by incorporating a malicious .suo file within a Visual Studio project. When unsuspecting users compile the project, the Trojan executes automatically, effectively compromising their systems.
Investigate Real-World Malicious Links, Malware & Phishing Attacks With ANY.RUN – Try for Free
The poisoned account, set up to resemble a legitimate security researcher from a prominent Chinese FinTech company, is linked to the malicious repository at GitHub.
The OceanLotus group targeted Chinese cybersecurity researchers, with the attack commencing between mid-September and early October 2024.
On October 10, the rogue account registered on GitHub, strategically forking various legitimate security tools to lower the victims’ guard.
Within days, two malevolent projects were published, containing Chinese-language descriptions and aimed specifically at enticing local cybersecurity professionals.
Despite the attacker’s subsequent deletion of these projects, the poisoned code had already been integrated into other researchers’ repositories, making detection increasingly difficult.
The code is designed to execute malicious commands seamlessly while self-destructing to avoid detection.
ThreatBook’s extensive analysis revealed that the attack was not only sophisticated but indicative of OceanLotus’s evolving techniques.
By utilizing a combination of dll hollowing and base64 encoding, the malware establishes command-and-control communication via the Notion platform, cleverly circumventing traffic detection measures.
The research team provided numerous Indicators of Compromise (IOCs) derived from their analyses, enabling cybersecurity entities to enhance their defenses against such targeted threats.
ThreatBook’s suite of security tools—including the Threat Detection Platform (TDP) and Cloud Sandbox—has been instrumental in identifying and mitigating the effects of this attack.
The OceanLotus group’s use of GitHub for conducting such targeted cyber operations raises urgent awareness regarding software supply chain vulnerabilities.
As the cybersecurity landscape becomes increasingly complex, professionals must maintain vigilance and utilize robust security practices to protect sensitive information.
Cybersecurity professionals must remain informed and proactive in safeguarding their tools and identities against such pernicious threats.
Find this News Interesting! Follow us on Google News, LinkedIn, and X to Get Instant Updates!
A new project has exposed a critical attack vector that exploits protocol vulnerabilities to disrupt…
A threat actor known as #LongNight has reportedly put up for sale remote code execution…
Ivanti disclosed two critical vulnerabilities, identified as CVE-2025-4427 and CVE-2025-4428, affecting Ivanti Endpoint Manager Mobile…
Hackers are increasingly targeting macOS users with malicious clones of Ledger Live, the popular application…
The European Union has escalated its response to Russia’s ongoing campaign of hybrid threats, announcing…
Venice.ai has rapidly emerged as a disruptive force in the AI landscape, positioning itself as…