Amazon Web Services (AWS) has announced the general availability of Amazon GuardDuty Malware Protection for Amazon Simple Storage Service (Amazon S3).
This new feature expands GuardDuty Malware Protection to detect malicious file uploads to selected S3 buckets, enhancing the security of cloud storage.
Enhanced Malware Detection for S3
Previously, GuardDuty Malware Protection provided agentless scanning capabilities to identify malicious files on Amazon Elastic Block Store (Amazon EBS) volumes attached to Amazon Elastic Compute Cloud (Amazon EC2) and container workloads.
With the new update, AWS customers can now continuously evaluate new objects uploaded to S3 buckets for malware and take action to isolate or eliminate any malware found.
Amazon GuardDuty Malware Protection uses multiple AWS-developed and industry-leading third-party malware scanning engines to provide malware detection without degrading the scale, latency, and resiliency profile of Amazon S3.
This managed solution removes the operational complexity and cost overhead associated with automating malicious file evaluation at scale.
Free Webinar on API vulnerability scanning for OWASP API Top 10 vulnerabilities -> Book Your Spot
Simplified Security Management
With GuardDuty Malware Protection for Amazon S3, development, and security teams can work together to configure and oversee malware protection throughout their organization.
This feature is particularly useful for select buckets where newly uploaded data from untrusted entities is required to be scanned for malware.
Users can configure post-scan actions in GuardDuty, such as object tagging, to inform downstream processing or consume the scan status information provided through Amazon EventBridge to implement isolation of malicious uploaded objects.
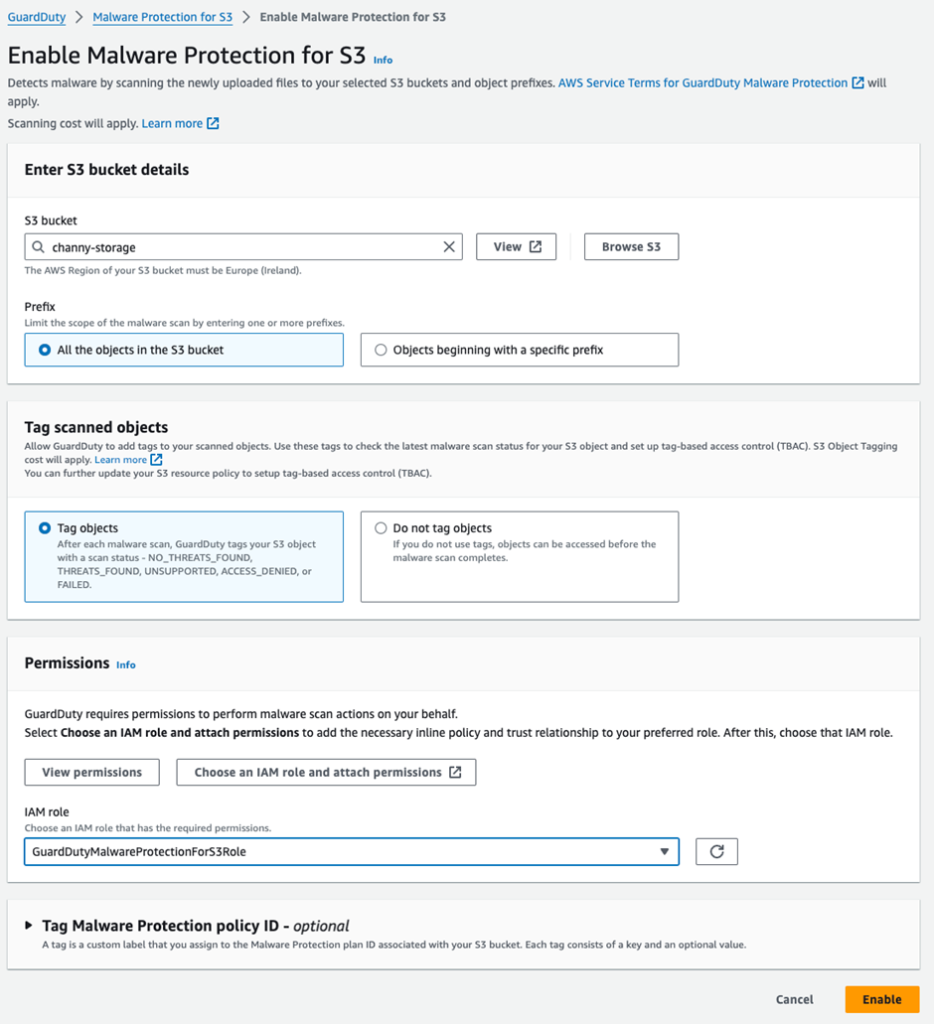
To get started, users can enable Malware Protection for S3 in the GuardDuty console, select the S3 bucket name, and choose the objects they want to scan.
After scanning a newly uploaded S3 object, GuardDuty can add a predefined tag with the key as GuardDutyMalwareScanStatus and the value as the scan status, such as NO_THREATS_FOUND, THREATS_FOUND, UNSUPPORTED, ACCESS_DENIED, or FAILED.
GuardDuty Malware Protection
To enable GuardDuty Malware Protection for an S3 bucket, users must create and attach an AWS Identity and Access Management (IAM) role with the required permissions.
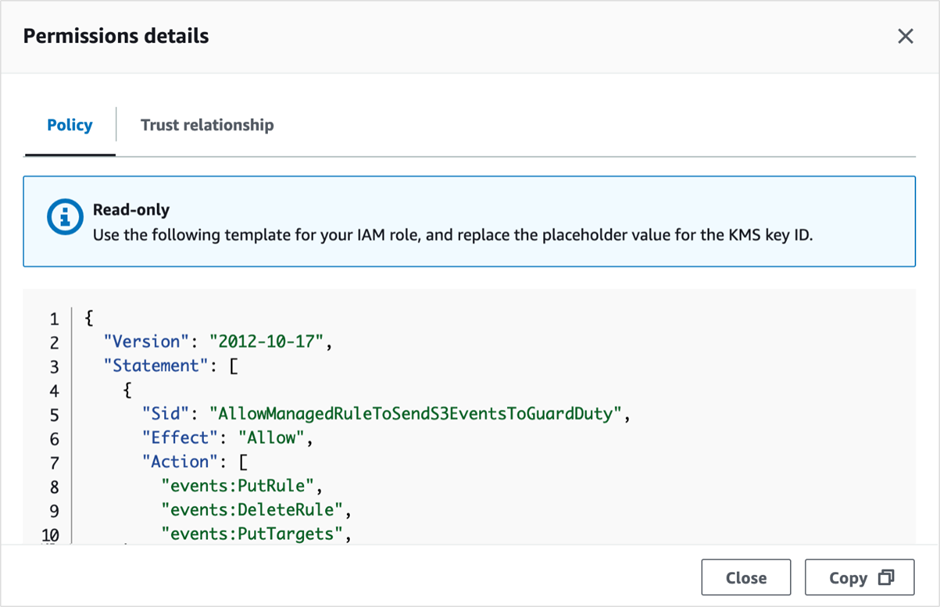
These permissions include EventBridge actions to create and manage the EventBridge managed rule, Amazon S3 and EventBridge actions to send S3 Event Notifications to EventBridge, Amazon S3 actions to access the uploaded S3 object and add a predefined tag, and AWS Key Management Service (AWS KMS) key actions to access the object before scanning.
Once the IAM role is created or updated, users can enable the protection in the GuardDuty console.
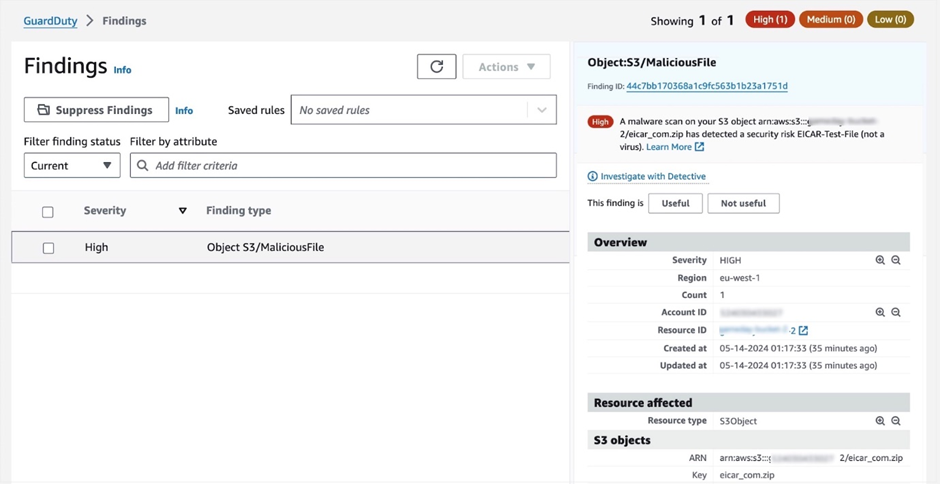
The protected bucket’s protection status will show as Active, and users can view all S3 malware findings to see the generated GuardDuty findings associated with their scanned S3 bucket.
Users can follow the recommended remediation steps in the Findings details panel if a malicious file is detected.
Things to Know
GuardDuty Malware Protection for S3 buckets can be set up even without GuardDuty enabled for the AWS account.
However, enabling GuardDuty provides full monitoring of foundational sources, such as AWS CloudTrail management events, Amazon Virtual Private Cloud (Amazon VPC) Flow Logs, DNS query logs, and malware protection features.
Security findings can also be sent to AWS Security Hub and Amazon Detective for further investigation.
GuardDuty can scan files from various Amazon S3 storage classes, including S3 Standard, S3 Intelligent-Tiering, S3 Standard-IA, S3 One Zone-IA, and Amazon S3 Glacier Instant Retrieval.
The feature supports file sizes up to 5 GB, including archive files with up to five levels and 1,000 files per level after decompression.
Amazon GuardDuty Malware Protection for Amazon S3 is now generally available in all AWS Regions where GuardDuty is available, excluding China Regions and GovCloud (US) Regions.
Pricing is based on the GB volume of the objects scanned and the monthly number of objects evaluated.
A limited AWS Free Tier is available, which includes 1,000 requests and 1 GB each month for the first 12 months of account creation for new AWS accounts or until June 11, 2025, for existing AWS accounts.
Free Webinar! 3 Security Trends to Maximize MSP Growth -> Register For Free
.webp?w=696&resize=696,0&ssl=1)


