
.webp?w=1600&resize=1600,900&ssl=1)
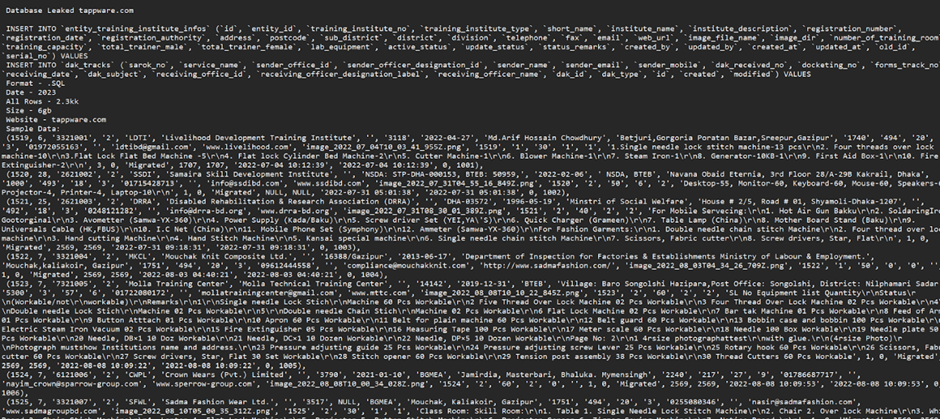
Tappware, a prominent IT service provider, faced a breach when approximately 50GB of its database was leaked on a hacker forum.
This database contained 2.3 million rows of data, including sensitive personal information such as names, addresses, and phone numbers of individuals associated with the company.
94% of organizations experience security problems in production APIs, and one in five suffers a data breach. As a result, cyber-attacks on APIs increased from 35% in 2022 to 46% in 2023, and this trend continues to rise:
Key Takeaways:
Start protecting your APIs from hackers
According to the Bangladesh Cyber Security Intelligence (BCSI) reports, the leaked data, structured in SQL format and dated 2024, included a wide range of personal details, posing a substantial privacy risk to the individuals involved.
The exposure was discovered during routine monitoring activities on platforms commonly used by cybercriminals to trade stolen data.

The leak directly threatens the privacy and security of thousands of individuals, potentially leading to identity theft and fraud.
This incident underscores the need for robust cybersecurity defenses to protect against unauthorized data access and prevent future breaches.
On-Demand Webinar to Secure the Top 3 SME Attack Vectors: Watch for Free.
Tappware faces potential reputational harm, affecting customer trust and business operations.
There is a risk of legal consequences and regulatory scrutiny due to non-compliance with data protection laws, which mandate stringent security measures to protect personal information.
Tappware should promptly activate its incident response plan, including identifying the breach’s scope, securing any vulnerabilities, and mitigating ongoing risks.
A comprehensive audit is crucial to uncover security weaknesses and implement corrective measures to protect data.
Enhancing the cybersecurity knowledge base of all employees will help prevent future incidents, particularly those stemming from human error.
Implementing MFA across all critical systems can significantly reduce the risk of unauthorized access.
This incident serves as a critical reminder of the vulnerabilities inherent in managing large sets of personal data and the continuous need for advanced security measures to protect against evolving cyber threats.
Tappware must take decisive actions to address the breach and prevent future occurrences, restoring trust and ensuring compliance with global data protection standards.
Is Your Network Under Attack? - Read CISO’s Guide to Avoiding the Next Breach - Download Free Guide
Cybersecurity experts at the AhnLab Security Intelligence Center (ASEC) have uncovered a novel phishing malware…
A newly disclosed authentication bypass vulnerability (CVE-2025-2825) in CrushFTP file transfer software enables attackers to…
A newly identified Android malware, dubbed TsarBot, has emerged as a potent cyber threat targeting…
A critical remote code execution (RCE) vulnerability, tracked as CVE-2025-24813, is being actively exploited in…
Water Gamayun, a suspected Russian threat actor, has been identified exploiting the MSC EvilTwin zero-day…
The Cybersecurity and Infrastructure Security Agency (CISA) has issued a detailed Malware Analysis Report (MAR-25993211-r1.v1)…