

As a dedicated bug bounty hunter with an enviable track record on BugCrowd, Abdullah Nawaf, Full full-time bug Bounty Hunter, thrives on the thrill of discovery and the challenge of finding high-impact vulnerabilities.
Recently, alongside his colleague Orwa Atyat, they achieved a notable success: turning a limited path traversal vulnerability into a fully-fledged remote code execution (RCE) exploit, earning a generous bounty of $40,000. Here’s a detailed account of their journey.
Our adventure began with standard reconnaissance on a target subdomain, specifically http://admin.target.com:8443. Initially met with a 404 response, many hunters would have moved on.
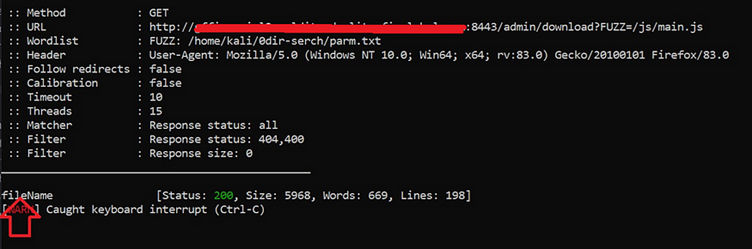
However, his instincts told me to dig deeper. Employing fuzzing techniques on the URL, they discovered an endpoint at /admin/Download, which returned a 200 OK status but an empty response, as per the report by Medium. This hinted at a potentially exploitable feature.
Investigate Real-World Malicious Links & Phishing Attacks With Threat Intelligence Lookup - Try for Free
Delving deeper into the admin path, he began testing for Local File Inclusion (LFI) and path traversal vulnerabilities. His tests revealed that the /download endpoint accepted a parameter called filename.
When he accessed http://admin.target.com:8443/admin/download?filename=/js/main.js, it displayed the contents of the JavaScript file.
However, the limitation was clear: the function only allowed access to files within the /admin/ directory.

Undeterred, he attempted to access /WEB-INF/web.xml, a file known to contain vital information. This strategic exploration proved fruitful, as he unearthed three URLs, including one for an /incident-report.
Upon visiting this endpoint, he triggered the download of a live log file—an unexpected twist that would lead us down a path of significant discovery.
Inside the log file, he stumbled upon sensitive data: admin credentials, including an MD5-hashed password.
After some attempts, he successfully logged into the admin panel using the credentials he found. This victory led him to an intriguing function called export_step2.xhtml, which housed a Groovy console—an interface for executing Groovy scripts.
Accessing the Groovy console opened the door to potential RCE, but executing commands yielded no visible output. This raised an important question: where was the command output hiding?
Upon reflection, he recalled that our log file could serve as a portal for uncovering the RCE output. By running commands through the Groovy console, he could leverage the log file to retrieve output.
Each time he visited http://admin.target.com:8443/admin/incident-report, a new log file was generated capturing the command execution results.
The cycle was straightforward:
This intricate chaining of vulnerabilities not only met the criteria for RCE but also showcased the importance of thorough exploration. He submitted reports on both the RCE and the credentials discovery, culminating in a total payout of $40,000 from the program.
This experience highlights the significance of persistence and creative problem-solving in the field of cybersecurity. Each bug bounty hunt holds the potential for monumental discoveries—if one is willing to dig deeper.
Integrating Application Security into Your CI/CD Workflows Using Jenkins & Jira -> Free Webinar
A startling discovery by BeyondTrust researchers has unveiled a critical vulnerability in Microsoft Entra ID…
The Cofense Phishing Defense Center has uncovered a highly strategic phishing campaign that leverages Google…
Cybersecurity researchers from Trustwave’s Threat Intelligence Team have uncovered a large-scale phishing campaign orchestrated by…
Cisco Talos has uncovered a series of malicious threats masquerading as legitimate AI tool installers,…
Pure Crypter, a well-known malware-as-a-service (MaaS) loader, has been recognized as a crucial tool for…
A recent discovery by security researchers at BeyondTrust has revealed a critical, yet by-design, security…