

Cyber police seized a huge bot farm that used to send large scale spam through various services such as email and social media.
The investigation was carried out by Ukraine police in six different regions. Attackers use homes, garages, apartments, and rented offices to carry out malicious activities.


To hide their anonymity and to anonymize the bot farm they used TOR and the VPN services. Further investigation reveals that the bot farm is operated exclusively for client interest.
The bot farm lets attackers register accounts on various online platforms that require user phone numbers to complete the verification process, such as social media, email, payment systems, etc..

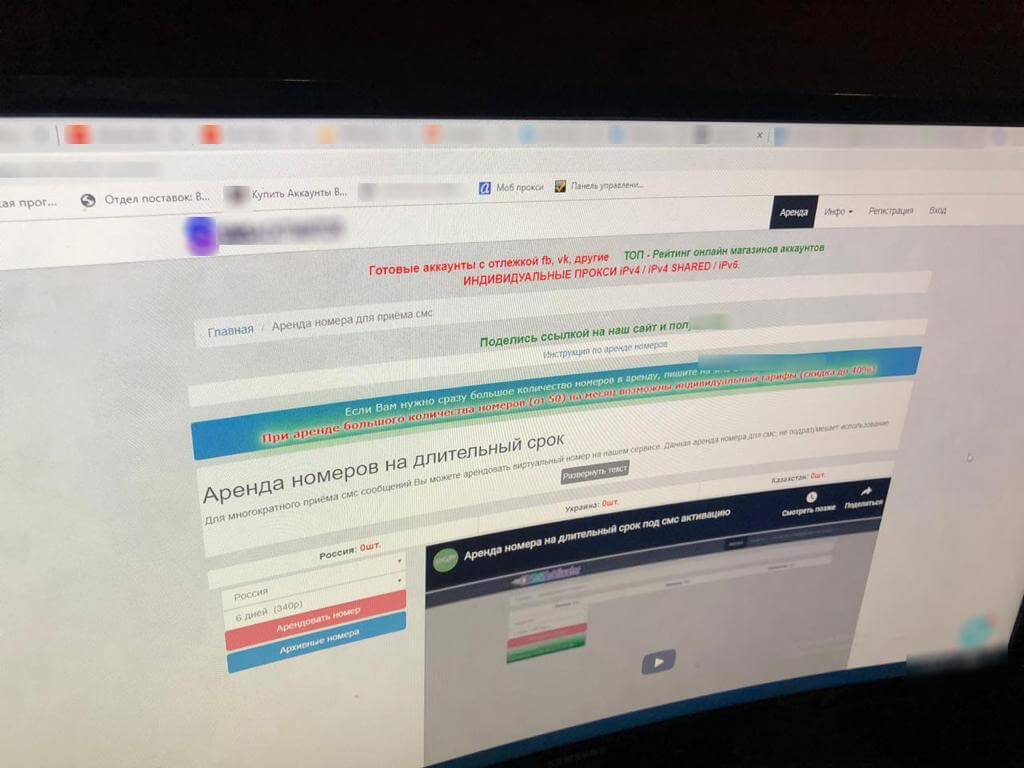
They also sold some verified accounts at a higher price to the interested clients. By having the verified accounts threat actors use them for spamming purposes.
Police seized several multi-SIM card modems, these modems would have at least 32 sim card slots and those modems provide multiple options to send bulk messages.
Ukraine police conducted investigations in six Ukraine cities Kyiv, Odessa, Lviv, Mykolayiv, Rivne and Kherson and the equipment was seized and submitted for further examination.
The images shared by Ukraine police show that attackers used several multi-SIM card modems and their intended purpose to send spam emails, messages such as (car wining, jackpot messages) and for phishing activity.
“Cyber police officers, together with investigators of the Main Investigative Directorate of the National Police of Ukraine, under the procedural guidance of the Prosecutor General’s Office of Ukraine, exposed a large-scale service for mass distribution of electronic messages.”
A pre-trial investigation in progress and the attackers involved in bot farm activities will be charged under criminal proceedings act.
You can follow us on Linkedin, Twitter, Facebook for daily Cybersecurity and hacking news updates
Brinker, an innovative narrative intelligence platform dedicated to combating disinformation and influence campaigns, has been…
A recent investigation by cybersecurity researchers has uncovered a large-scale malware campaign leveraging the DeepSeek…
A recent malware campaign has been observed targeting the First Ukrainian International Bank (PUMB), utilizing…
A newly discovered malware, dubbed Trojan.Arcanum, is targeting enthusiasts of tarot, astrology, and other esoteric…
A sophisticated phishing campaign orchestrated by a Russian-speaking threat actor has been uncovered, revealing the…
A sophisticated malware campaign has compromised over 1,500 PostgreSQL servers, leveraging fileless techniques to deploy…