

Attackers are ingeniously exploiting Google Calendar and Google Drawings in phishing campaigns, targeting unsuspecting individuals and organizations.
Leveraging the inherent trust in Google’s widely used tools, cybercriminals are successfully deceiving users into revealing sensitive information and compromising their accounts.
Google Calendar, a widely used scheduling tool with over 500 million users globally, has become an attractive target for malicious actors.
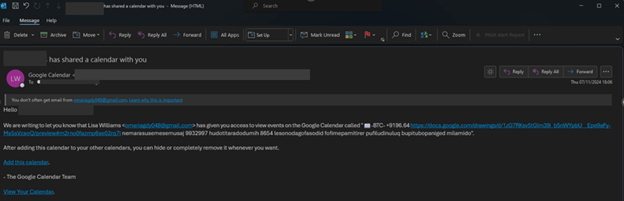
According to cybersecurity researchers at Check Point, attackers are utilizing Google Calendar’s features and modifying “sender” headers to make phishing emails appear as if they originate directly from Google.
Free Webinar on Best Practices for API vulnerability & Penetration Testing: Free Registration
These emails often impersonate well-known individuals or brands, adding credibility to their deception.

In a recent campaign, over 4,000 phishing emails, affecting nearly 300 brands were observed in just four weeks.
Initially, the attackers used links leading to Google Forms, but as security systems began detecting these attempts, the campaign shifted focus to Google Drawings.
The phishing campaigns typically begin with a calendar invite containing a phishing link disguised as a legitimate Google feature. Here’s how the attack unfolds:
Impact and Consequences
These phishing campaigns not only result in financial losses but also compromise personal and corporate data, causing stress and long-term repercussions.
Victims may face unauthorized transactions, identity theft, and security breaches on other linked accounts.
How to Protect Against These Scams
For Organizations
For Individuals
A Google spokesperson recommends enabling the “known senders” setting in Google Calendar, which alerts users to invitations from unknown contacts. This simple feature can help users stay vigilant against these phishing threats.
Investigate Real-World Malicious Links, Malware & Phishing Attacks With ANY.RUN – Try for Free
A startling discovery by BeyondTrust researchers has unveiled a critical vulnerability in Microsoft Entra ID…
The Cofense Phishing Defense Center has uncovered a highly strategic phishing campaign that leverages Google…
Cybersecurity researchers from Trustwave’s Threat Intelligence Team have uncovered a large-scale phishing campaign orchestrated by…
Cisco Talos has uncovered a series of malicious threats masquerading as legitimate AI tool installers,…
Pure Crypter, a well-known malware-as-a-service (MaaS) loader, has been recognized as a crucial tool for…
A recent discovery by security researchers at BeyondTrust has revealed a critical, yet by-design, security…