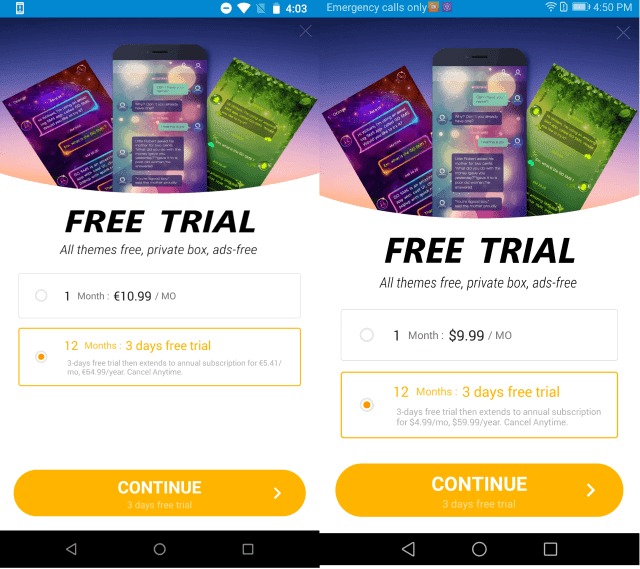
Fleeceware apps continue to be a problem on Google Play, these app publishers overcharge users for basic functionality if they don’t cancel the subscription before the trial ends.
The app publishers take advantage of the business model in which user downloads and use the app for a short trial period for no charge.
If the user fails to uninstall the app and inform the developer that they are not interested at the end of the short trial period, then the app developers charge the users.
Fleeceware on Google Play
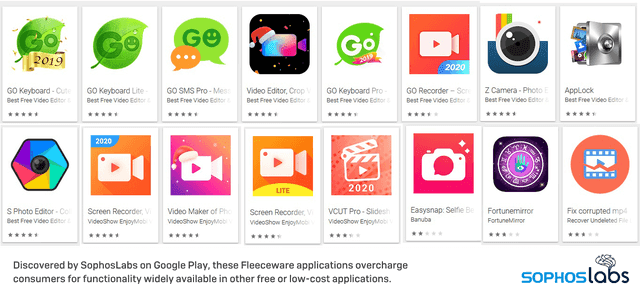
Sophos observed several Fleeceware apps on Google play store that cause monetary damage to users. these apps found to be installed more than 600 million times in total.
Also, some of the apps such as keyboard apps allegedly transfer the text typed by the users to the servers located in China.
The apps associated with categories such as entertainment or utility apps, including fortune-tellers, instant messengers, video editors, and beauty apps.
Several users complain that even after following the subscription rules, they have been charged by the app developers.
Some of the apps mimic the original apps in the design and other features, but there is a difference in the subscription.
The bad news is that some of the apps on the play store claim they have “1 million, 5 million, 10 million, or even 100 million installs.”
Researchers believe these app developers may use some paid services to reach the users. Also, they use to add fake reviews.
A high number of reviews and installs let the apps appear at the top of the list and attract the users.
A full list of the apps and download counts can be found here. Sophos has reported malicious apps to the Google Play Store.
You can follow us on Linkedin, Twitter, Facebook for daily Cybersecurity and hacking news updates










