

Researchers discovered major vulnerabilities in several Free VPN apps for Android that allow attackers to perform dangerous Man-in-the-Middle Attacks and steal usernames, passwords, photos, videos, messages and more.
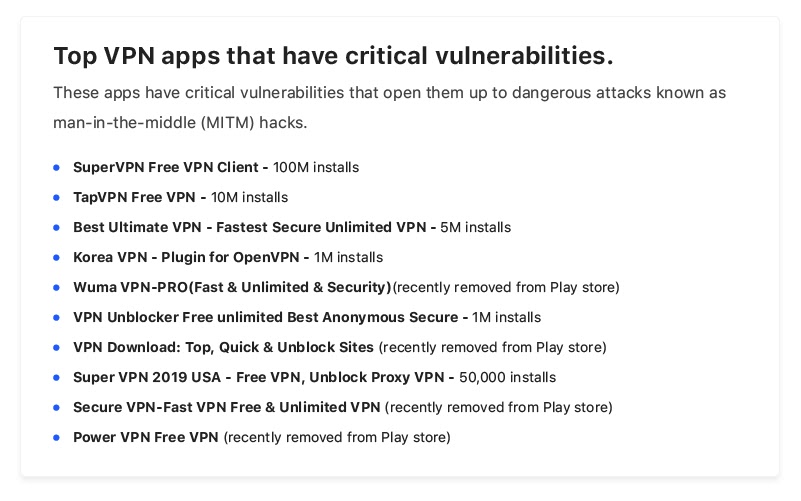
There are several VPN’s caught in this list that downloaded more than 120 million times from Google Play and the Free VPN called SuperVPN alone downloaded 100 million times.

In this list, SuperVPN gained a huge impression among the Android community, and it has been downloaded from nearly 150 countries.

SuperVPN is developed by SuperSoftTech, a Singapore based company but it actually belongs to the independent app publisher Jinrong Zheng from China.
Researchers tested the SuperVPN that connects the multiple hosts, in which several communications that contain sensitive encrypted data is being sent via unsecured HTTP.
Also, the communication contains a decryption key that required to decrypt the information while in transit, using the key, researchers were able to decrypt the data.
It leads to finding some of the sensitive data about SuperVPN’s server, its certificates, and the credentials that the VPN server needs for authentication.
This information enough to replace the real SuperVPN server data with fake server data by the attackers.
By abusing the vulnerability, hackers will intercept the communication of the users, and accessing some of the most sensitive data including the visited websites and stealing usernames and passwords, photos, videos, and messages and more.
According to VPNpro Research “Some apps have their encryption keys hard-coded within the app. This means that, even if the data is encrypted, hackers can easily decrypt this data with the included keys “
App developers left some of the encryption keys hard-coded within the app that helps attackers to easily access the encrypted data and also force users to connect the malicious VPN servers and redirect the traffic to their own servers.
“At that time, in 2016, SuperVPN had only 10,000 installs. Now, three years later, it already has more than 100 million installs. Surprisingly, even though multiple articles called out SuperVPN for containing malware, it still hasn’t been removed from the Play store.” VPNPro said.
Follow us on Twitter, Linkedin, Facebook for Daily cyber security & hacking news updates.
Secure Ideas, a premier provider of penetration testing and security consulting services, proudly announces its…
Symantec has recently identified a sophisticated phishing campaign targeting users of Monex Securities (マネックス証券), a…
In a concerning development, CERT-UA, Ukraine's Computer Emergency Response Team, has reported a series of…
Hunters International, a ransomware group suspected to be a rebrand of the infamous Hive ransomware,…
In a recent cyberattack attributed to the Qilin ransomware group, threat actors successfully compromised a…
A newly uncovered cyber-espionage campaign, dubbed Operation HollowQuill, has been identified as targeting academic, governmental,…
View Comments
Oh nooo! its better to don't use free VPNs