

A notorious threat actor has allegedly begun selling “Baldwin Killer,” a sophisticated malware toolkit designed to bypass leading antivirus (AV) and endpoint detection and response (EDR) systems.
The tool, advertised on dark web forums, claims to circumvent security solutions such as Windows Defender, Kaspersky, Bitdefender, and Avast, raising alarms among cybersecurity experts globally.

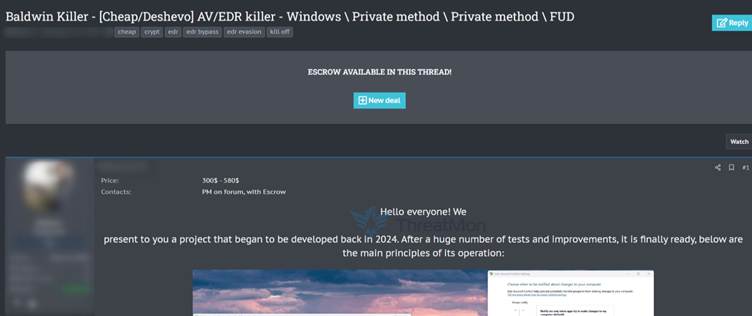
According to a post shared on a dark web portal, the malware employs multiple evasion techniques:
The toolkit’s modular design suggests adaptability, potentially allowing buyers to customize attacks for ransomware, data theft, or espionage.
While the claims remain unverified, cybersecurity analysts highlight the plausibility of such a threat.
“Kernel-level rootkits and early boot persistence are red flags for advanced persistent threats (APTs),” said Dr. Elena Carter, a malware analyst at SecureWave Labs. “If real, this tool could empower even low-skilled hackers to launch high-impact attacks.”
The malware’s alleged ability to bypass EDR systems—a last line of defense for many organizations—is particularly concerning.
The advertisement did not specify a price, but such tools typically fetch tens of thousands of dollars on underground markets. Potential targets could include:
Authorities fear the tool could lower barriers to entry for cybercriminals, enabling more frequent and destructive attacks.
Organizations are urged to adopt proactive measures:
Microsoft and other vendors have been notified, but no official patches or advisories have been released as of publication.
As cybersecurity firms race to reverse-engineer the malware’s capabilities, the incident underscores the evolving arms race between attackers and defenders.
For now, vigilance and adaptive defense strategies remain the best defense against tools like “Baldwin Killer.”
Find this News Interesting! Follow us on Google News, LinkedIn, & X to Get Instant Updates!
A new project has exposed a critical attack vector that exploits protocol vulnerabilities to disrupt…
A threat actor known as #LongNight has reportedly put up for sale remote code execution…
Ivanti disclosed two critical vulnerabilities, identified as CVE-2025-4427 and CVE-2025-4428, affecting Ivanti Endpoint Manager Mobile…
Hackers are increasingly targeting macOS users with malicious clones of Ledger Live, the popular application…
The European Union has escalated its response to Russia’s ongoing campaign of hybrid threats, announcing…
Venice.ai has rapidly emerged as a disruptive force in the AI landscape, positioning itself as…