A creative Office 365 phishing campaign was discovered by WMC Global Analysis researchers that a legitimate login page of a Microsoft Account, but uses color inversion to avoid matching patterns from image recognition software, according to Kim Komando.
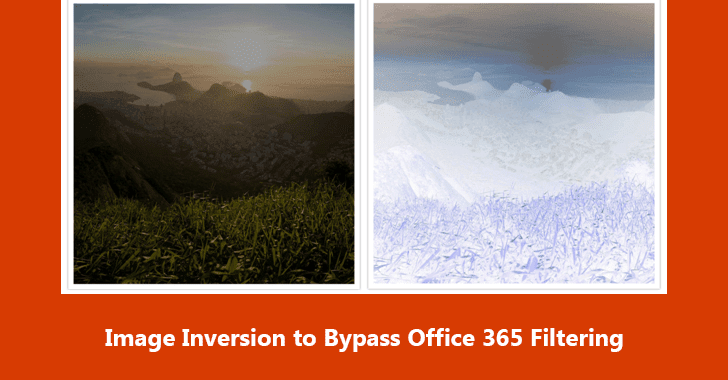
“As image recognition software is improving and becoming more accurate, this new technique aims to mislead scanning engines by inverting the colors of the image, causing the image hash to differ from the original.”, WMC Global explains.
This method can hinder the software’s ability to flag this image altogether (as shown in the images below).
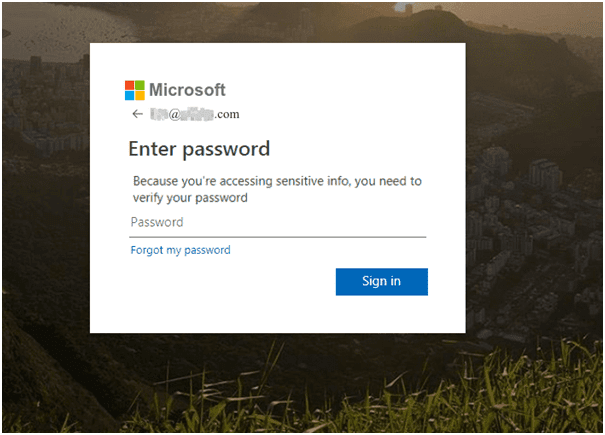
A victim visiting the website would likely recognize that the inverted picture is illegitimate and exit the website. Nevertheless, the threat actor has stored the inverted image and, within the index.php code, has used a CSS method to revert the color of the image to its original state.

Threat actors constantly plan to bypass detection, and that they can fool scanning engines by inverting or altering recognizable logos and pictures. This approach leads to the ultimate website’s appearing legitimate to users who visit, while crawlers and scanning engines are highly doubtful to detect the image as being an inverted copy of the Office365 background.
Tips to avoid getting tricked
- Avoid opening emails from unknown senders and always check the URLs and sender fields closely.
- Avoid clicking on links inside emails.
- Use strong passwords without including personal information or common words.
- Use a strong antivirus with a proven detection rate against phishing attacks
As realistic as these phishing sites look, they tend to appear in places they have no business, like through random email links or pop-up ads. If you stay cautious and avoid sharing your login carelessly, your account is going to be safe.
You can follow us on Linkedin, Twitter, Facebook for daily Cybersecurity and hacking news updates.
Also Read
Hackers Using COVID-19 Training Lure to Attack Office 365 Users
Hackers Would Bypass Multi-Factor Authentication to Gain Full Access to Microsoft 365 Services







.webp)


.webp)