Microsoft has taken down the infamous Necurs botnet that impacted more than nine million computers worldwide. The Necurs botnet is the largest spam and malware botnet.
The botnet is known for distributing several malware particularly the Locky ransomware malware, the botnet believed to be operated from Russia.
The Necurs botnet was first detected in 2012, it primarily acts as a dropper for other malware, between the years 2016 to 2019 the botnet emerges as largets one and responsible for 90% of the malware spread by email worldwide.
Necurs Botnet TakeDown
The world’s largest botnet was taken down as a coordinated operation between Microsoft and partners across 35 countries.
Microsoft said that within a “58-day period in our investigation, for example, we observed that one Necurs-infected computer sent a total of 3.8 million spam emails to over 40.6 million potential victims.”
The botnet is known for conducting various spam attacks such as stock scams, fake pharmaceutical spam email and “Russian dating” scams. Necurs also used for launching DDoS attacks.
The botnet continues to utilize advanced functions to evade security mechanisms placed in the organization.
To take down the botnet operation Microsoft broken down the domain generation algorithm (DGA) technology implemented by Necurs for registering new domains to execute attacks.
In the last 25 months more than six million unique domains registered by the botnet to launch various attacks.
Microsoft reported the domain name’s to the registries around the world so that those domains are blocked from becoming a part of Necurs infrastructure.
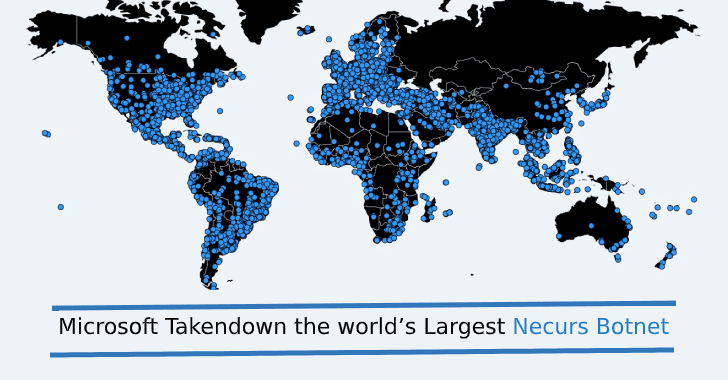
BitSight who worked with Microsoft for Necurs malware takedown provides an Infection Telemetry map that shows how a week of Necurs infection telemetry is dispersed geographically.

The authors of the Necurs botnet system implemented a layered approach using a mixture of a centralized and peer-to-peer (P2P) communication channels, here is the Necurs C2 flow.

“By taking control of existing websites and inhibiting the ability to register new ones, we have significantly disrupted the botnet, Microsoft added.






.webp)

.webp)
