
.webp?w=1600&resize=1600,900&ssl=1)
A sophisticated phishing campaign, recently identified by LayerX Labs, has shifted its focus from Windows users to Mac users in response to enhanced security measures implemented by major browsers.
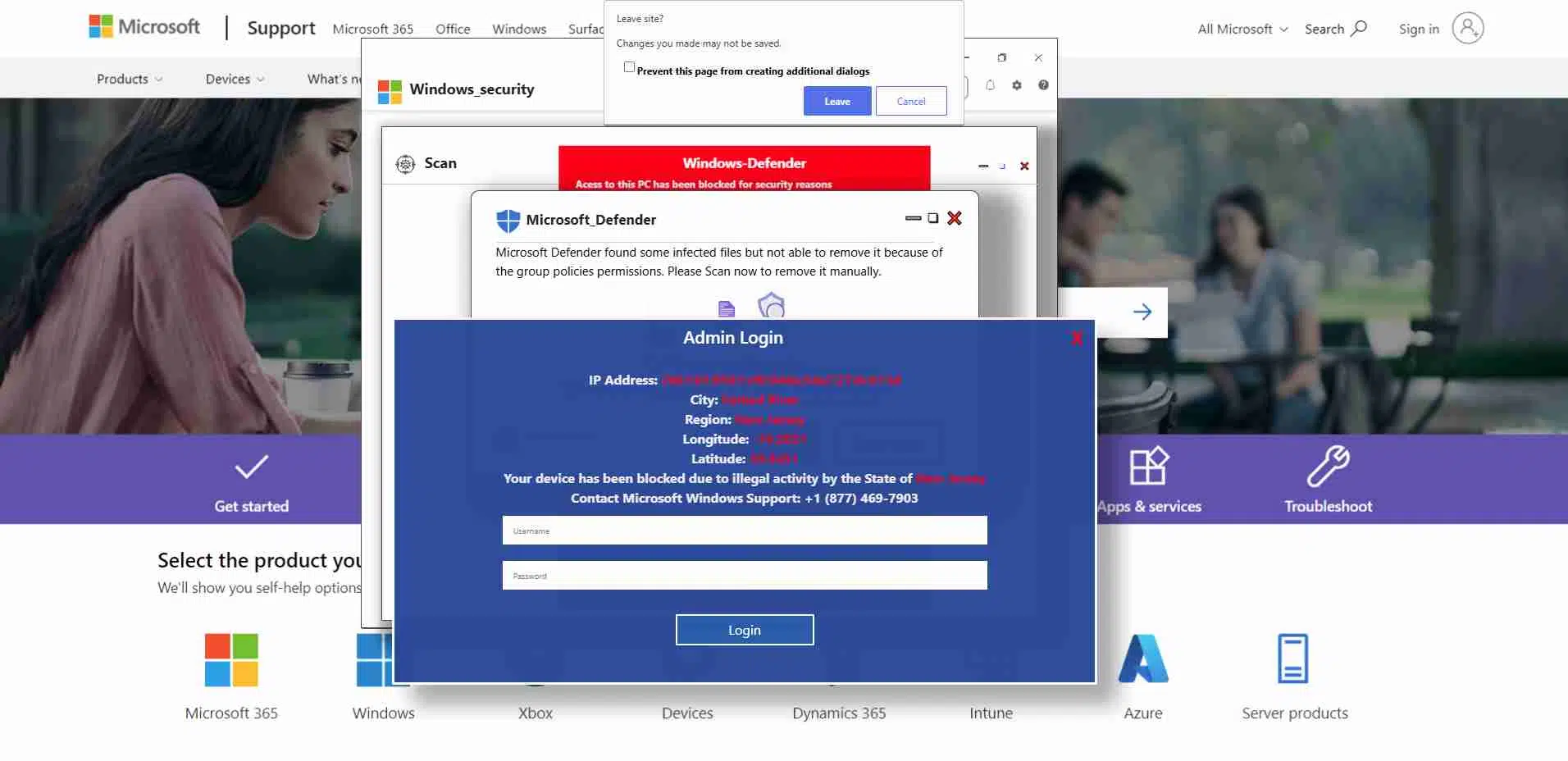
Initially, this campaign targeted Windows users by masquerading as Microsoft security alerts, aiming to steal login credentials by creating the illusion of a compromised computer.
The attackers exploited Microsoft’s Windows.net platform to host phishing pages, making them appear legitimate and bypassing traditional anti-phishing defenses due to the platform’s high reputation score.
The original phishing attack involved compromised websites displaying fake security warnings, prompting users to enter their Windows credentials.
The attackers used malicious code to freeze the webpage, creating the illusion that the entire computer was locked.
According to the Report, this campaign was highly effective and long-running, with attackers frequently updating the phishing pages to avoid detection by security tools.
However, with the introduction of new ‘anti-scareware’ features in browsers like Microsoft Edge, Chrome, and Firefox, the campaign’s success rate significantly dropped, leading to a 90% decrease in Windows-targeted attacks.

In response to these new defenses, the attackers have adapted their campaign to target Mac users, who were not covered by these recent security updates.
The phishing pages were redesigned to appear legitimate to Mac users, with adjustments made to specifically target macOS and Safari users by leveraging HTTP OS and user agent parameters.
The attackers continued to use the Windows.net infrastructure to maintain the illusion of legitimacy.
Victims were typically redirected to these phishing pages via compromised domain ‘parking’ pages, often accessed due to typos in URLs.
This shift highlights the adaptability of cybercriminals and underscores the need for advanced, proactive security solutions.
Mac and Safari users are now prime targets for sophisticated phishing campaigns, which have rarely reached this level of complexity before.
As security measures evolve, attackers continue to modify their tactics, indicating that this campaign is likely to evolve further in response to new defenses.
Investigate Real-World Malicious Links & Phishing Attacks With Threat Intelligence Lookup – Try for Free
From WannaCry to the MGM Resorts Hack, ransomware remains one of the most damaging cyberthreats…
Cybersecurity researchers have discovered a sophisticated phishing-as-a-service (PhaaS) platform, dubbed "Morphing Meerkat," that leverages DNS…
A recently identified Remote Access Trojan (RAT) has raised alarms within the cybersecurity community due…
PJobRAT, an Android Remote Access Trojan (RAT) first identified in 2019, has resurfaced in a…
In a complex cyber operation discovered by Silent Push Threat Analysts, Russian hackers have launched…
Elastic Security Labs has uncovered a sophisticated malware campaign, dubbed REF8685, targeting the Iraqi telecommunications…