Unit 42 researchers at Paloalto discovered a cryptocurrency mining botnet named “PGMiner”. It is a Linux based cryptocurrency botnet that exploits a disputed PostgreSQL remote code execution(RCE) vulnerability that allows database servers for cryptojacking.
Cryptojacking is an emerging online threat that hides on a computer or mobile and uses that devices’ computing power to maliciously mine for cryptocurrency.
PGMiner exploits CVE-2019-9193 in PostgreSQL,a.k.a Postgres, a popular open source RDBMS. PostgreSQL is one of the most popular DBMS. “Copy from program,” is the feature being exploited and this was introduced in version 9.3 on Sept. 9, 2013.
In 2018, CVE-2019-9193 was linked to this feature, naming it as a “vulnerability.” However, the PostgreSQL community challenged this assignment, and the CVE has been labelled as “disputed.” Earlier only confirmed CVEs were targeted by malware actors, but now even those in disputed status appear to be targeted.
Process view of the attack
PGMiner attempts to connect to the mining pool of cryptocurrency Monero. PGMiner’s coin mining techniques resembles those of the SystemdMiner family with a few significant variances:
- Delete the PostgreSQL table right after code launch to achieve fileless execution.
- Collect system information and send it to the command and control (C2) server for victim identification.
- Employ traditional and novel approaches to download curl binary in case the command is not available on the victim’s machine.
- Impersonate the “tracepath” process to hide its presence.
- Attempt to kill competitor programs for better monetization
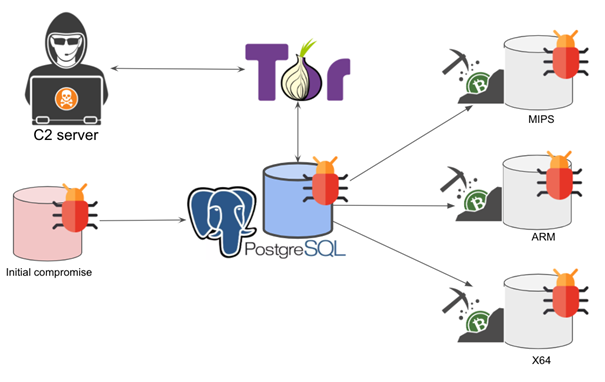
Firstly, the malicious payload is delivered via PostgreSQL. Which then talks to the backend C2 servers through SOCKS5 proxies. After which, it downloads the coin mining payloads based on the system architecture. It is also found that GMiner constantly reproduces itself by recursively downloading certain modules.
Secondly, the attacker scans port 5432 (0x1538), used by PostgreSQLql of the hosts in the private/local network (i.e., 172.16.0.0, 192.168.0.0 and 10.0.0.0 subnets) and the malware randomly picks a public network range (e.g., 190.0.0.0, 66.0.0.0) to perform RCE on the PostgreSQL server.
With the user “postgres” the attacker performs a brute-force attack iterating over a built-in list of popular passwords such as “112233“ and “1q2w3e4r“ to crack the database authentication.
Thus, by breaking the database, the PostgreSQL uses “copy from program” feature to download and launch the coin mining scripts which is featured to allow the local or remote superuser to run shell script directly on the server.
Thirdly, the malicious script tries to download the curl binary using any of the following ways and adds it to the execution paths:
- Direct installation from official package management utilities like apt-get and yum.
- Download static curl binary from GitHub.
- Download using /dev/tcp in case the normal ways doesn’t work.
After downloading the curl and resolving the SOCKS5 proxy server IP address, PGMiner finds the first folder which allows permission to create a new file and hence updates its attributes.
On succeeding, the downloaded malicious payload will be successfully executed in the victim’s machine.
The recovered payloads are x86_64 which is an ELF executable, aarch64 and armv7l which are identical shell script
Behavior of x86_64 ELF executable
Environment Preparation:
- Download and install curl binary as explained above.
- Install crontab.
- Remove cloud security monitor tools such as Aegis, and Qcloud monitor utilities such as Yunjing.
Virtual Machine Checking: PGMiner checks the existence of VBoxGuestAdditions to infer whether it is being analyzed in a virtual environment.
Competitors Removal
- Remove other known miner scripts, processes and crontab records.
- Kill miner cleanup processes.
- Kill all other CPU intensive processes such as ddg, system updates and so on.
- Kill processes connected to known mining IP addresses.
Behavior of aarch64 and armv7l
The cmd module first attempts to kill the tracepath process and then downloads additional payload from the same C2 address. The downloaded malware impersonates the tracepath process to hide its presence.
Recommendation and Advise To remove the impact of PGMiner on the PostgreSQL server, the user can search and kill the “tracepath” processand kill the processes whose process IDs which have been tracked by the malware in “/tmp/.X11-unix/”.
You can follow us on Linkedin, Twitter, Facebook for daily Cybersecurity, and hacking news updates.
Also Read