

File copy vulnerability in ProFTPD server allows an anonymous remote attacker to execute the code in vulnerable machine results in remote code execution and information disclosure without authentication.
By exploiting the vulnerability attacker can run any program code with the rights of the Pro-FTPd service. The vulnerability can be tracked as CVE-2019-12815 and it affects all the versions up to 1.3.5b.
The vulnerability resides in ProFTPd’s mod_copy module that supplied with the default installation, by issuing CPFR, CPTO commands to a ProFTPd server allows users without write permissions to copy any file on the FTP server, says Tobias Mädel who identified the vulnerability.
It is a free open source FTP server that is compatible with Unix-like operating systems and Microsoft Windows. According to Shodan results, more than 1 Million Servers running vulnerable versions.

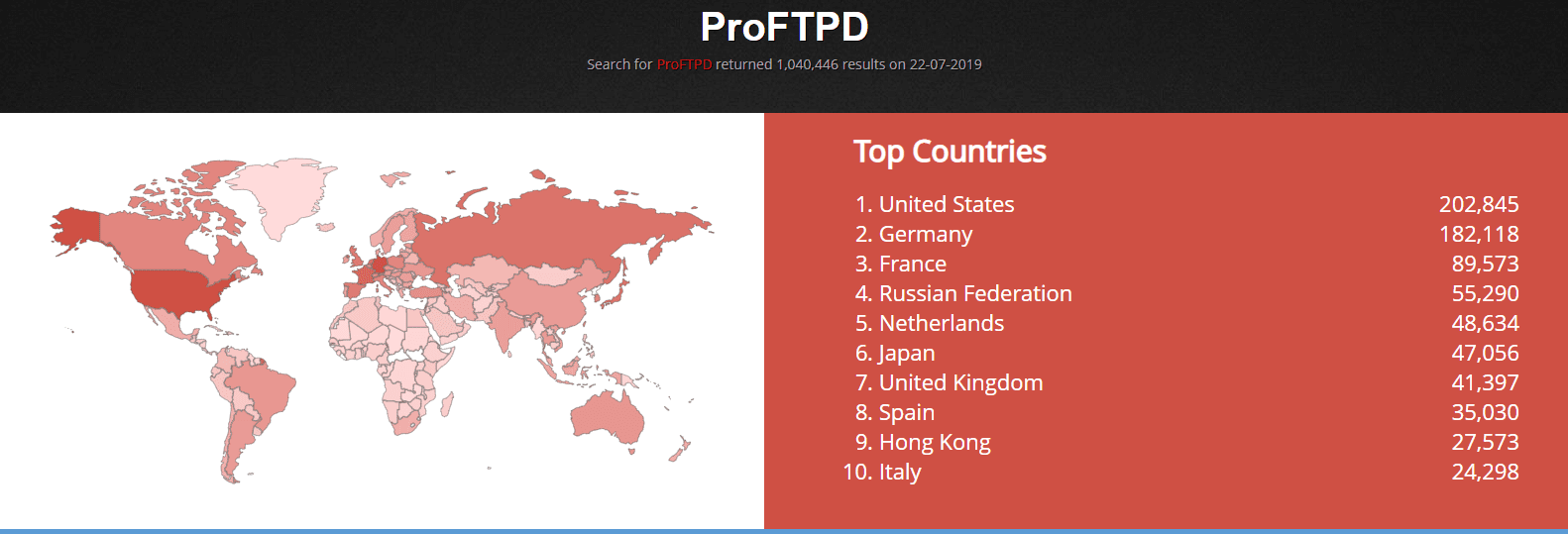
Shodan report states that 1.3.5b is the most uses version of the ProFTPD and the most used operating system are Linux ones. Here is the full shodan report.
In future attackers may use exploits to compromise the vulnerable servers and infect them with malware.
Also Read: Critical Vulnerability in VLC Media Player 3.0.7.1 Let Hackers to Execute Arbitrary Code
28.09.2018 Reported to ProFTPd security@, ProFTPd asking for clarifications
12.06.2019 Reported to Debian Security Team, replies by Moritz & Salvatore
28.06.2019 Deadline for public disclosure on 28.07.2019 announced
17.07.2019 Fix published by ProFTPd
You can follow us on Linkedin, Twitter, Facebook for daily Cybersecurity updates also you can take the Best Cybersecurity course online to keep yourself updated.
MathWorks, the renowned developer of MATLAB and Simulink, has been grappling with the aftermath of…
On May 27, 2025, the Cybersecurity and Infrastructure Security Agency (CISA) released a new Industrial…
The Chrome team at Google has officially released Chrome 137 to the stable channel for…
Mozilla has released Firefox 139, addressing several critical and moderate security vulnerabilities that posed significant…
INE Security, a global cybersecurity training and certification provider, today announced a strategic partnership with…
DocuSign has emerged as a cornerstone for over 1.6 million customers worldwide, including 95% of…