

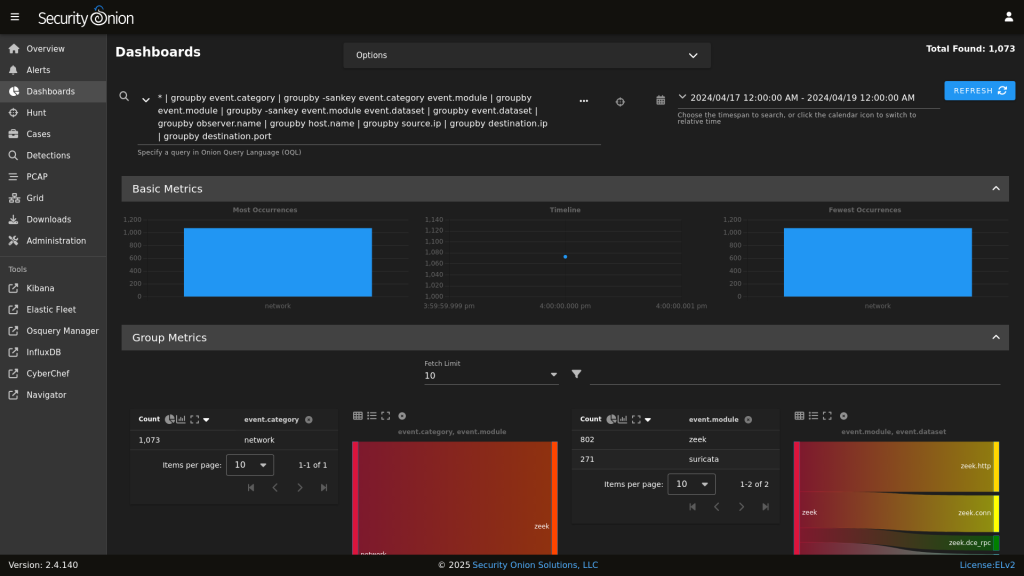
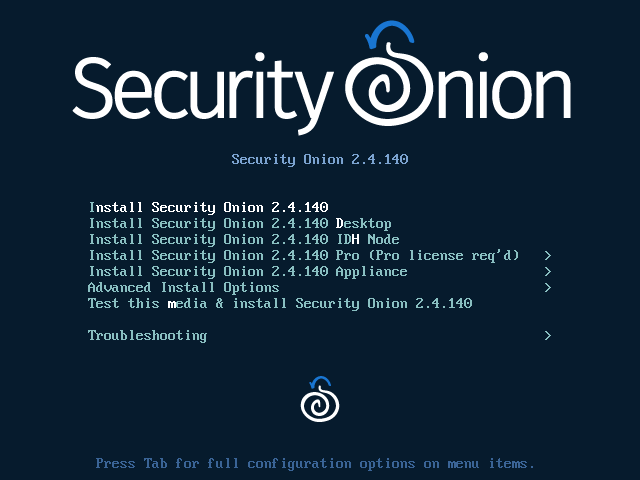
Security Onion, a widely used open-source platform for network security monitoring, has recently released Security Onion 2.4.140.
This latest update focuses on enhancing key components such as Suricata and Zeek, offering improved security and functionality to its users.


Below is a breakdown of what’s new and how this release impacts security teams worldwide.
Key Component Updates
Security Onion 2.4.140 emphasizes critical security updates and usability enhancements, reinforcing its position as a go-to tool for security professionals seeking robust network monitoring and management capabilities.
As the security landscape continues to evolve, platforms like Security Onion play a vital role in equipping defenders with the tools they need.
Investigate Real-World Malicious Links & Phishing Attacks With Threat Intelligence Lookup - Try for Free
A new project has exposed a critical attack vector that exploits protocol vulnerabilities to disrupt…
A threat actor known as #LongNight has reportedly put up for sale remote code execution…
Ivanti disclosed two critical vulnerabilities, identified as CVE-2025-4427 and CVE-2025-4428, affecting Ivanti Endpoint Manager Mobile…
Hackers are increasingly targeting macOS users with malicious clones of Ledger Live, the popular application…
The European Union has escalated its response to Russia’s ongoing campaign of hybrid threats, announcing…
Venice.ai has rapidly emerged as a disruptive force in the AI landscape, positioning itself as…