

Every malware needs a medium to spread the infection, SilentFade malware abuses the Facebook ads platform to attack users for ad fraud, sales of counterfeit goods, pharmaceutical pills, and fraudulent product reviews. It was named by Facebook as SilentFade as it focuses on silently running Facebook ads.
SilentFade malware was first detected by Facebook during the final week of 2018, it takes advantage of the Facebook bug that lets attackers suppress notifications of suspicious user activity.
The malware is distributed through potentially unwanted programs (PUP), pirated copies of popular software, and possibly through other malware.
Once the malware gets installed on the user’s computer it stole Facebook credentials and cookies from various browser credential stores.
All the stolen data sent to the C2 server and then SilentFade, or its customers, would then be able to use the compromised user’s payment method to run malicious ad campaigns on Facebook.

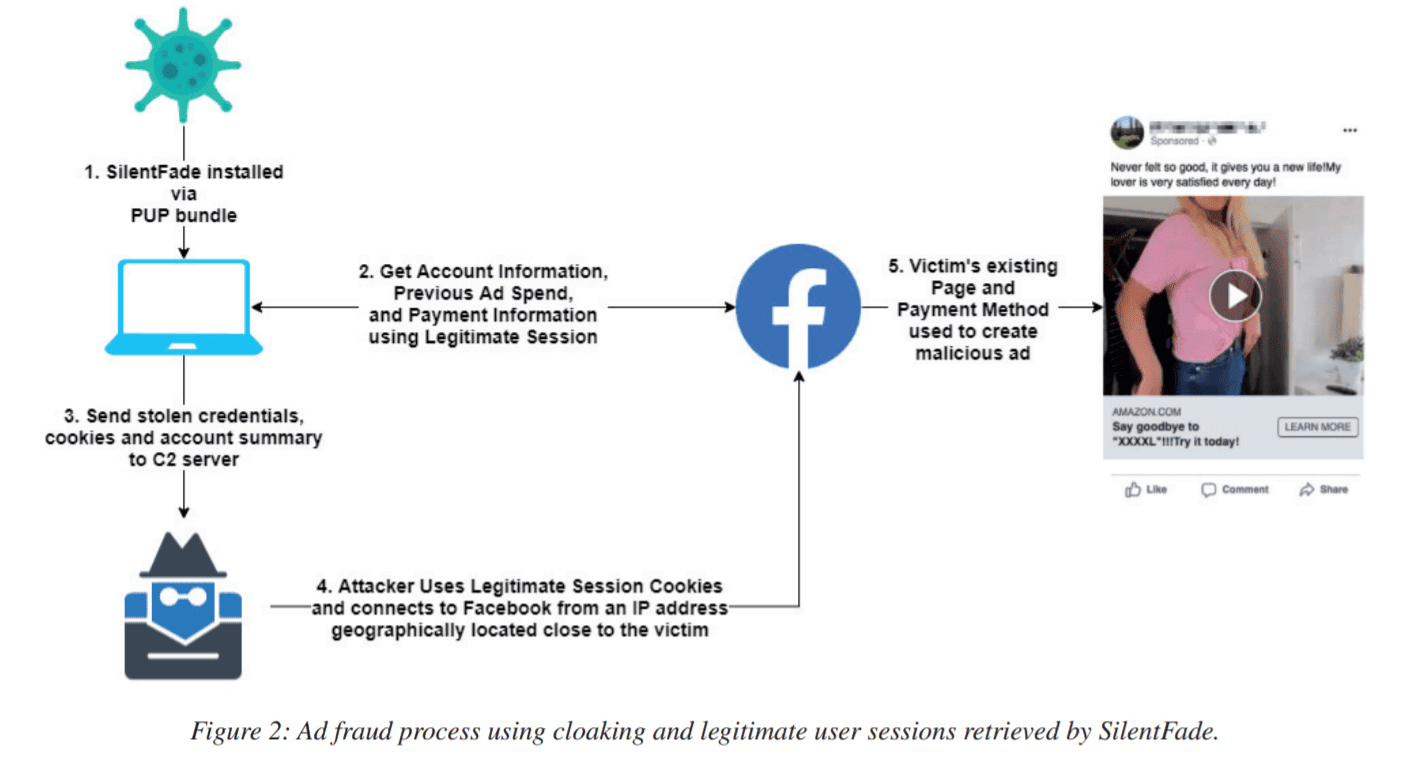
To make it appear legitimate attackers used the stolen credentials of the victim from the nearby or the same credentials they are located.
“SilentFade is equipped with credential-stealing components like those used by other malware campaigns in the wild. However, unlike the others, SilentFade’s credential-stealing component only retrieved Facebook-specific stored credentials and cookies located on the compromised machine,” reads the report.
As soon as the hacker group gained access to the victim’s Facebook account they disable notifications entirely by sending web requests. SilentFade also takes advantage of the Facebook option to explicitly block pages from messaging them.
By disabling this they can block Facebook from notifying users of suspicious logins on their Facebook account or any ad-related activity on their ad account.
“This was the first time we observed malware actively changing notification settings, blocking pages, and exploiting a bug in the blocking subsystem to maintain persistence in a compromised account.”
Attackers taking advantage of these bugs to run malicious ads run from legitimate pages using the original account owner’s payment method.
As part of remediation, Facebook fixed the server-side validation bug as soon they discovered, block states removed, and password reset has been forced for affected users.
You can follow us on Linkedin, Twitter, Facebook for daily Cybersecurity and hacking news updates.
Also Read
Facebook Hacking made Easy and Convenient with Numerous Hacking Apps
Facebook Announced New Privacy and Security Feature for Messenger
A startling discovery by BeyondTrust researchers has unveiled a critical vulnerability in Microsoft Entra ID…
The Cofense Phishing Defense Center has uncovered a highly strategic phishing campaign that leverages Google…
Cybersecurity researchers from Trustwave’s Threat Intelligence Team have uncovered a large-scale phishing campaign orchestrated by…
Cisco Talos has uncovered a series of malicious threats masquerading as legitimate AI tool installers,…
Pure Crypter, a well-known malware-as-a-service (MaaS) loader, has been recognized as a crucial tool for…
A recent discovery by security researchers at BeyondTrust has revealed a critical, yet by-design, security…