The government computer emergency response team of Ukraine, CERT-UA, in direct cooperation with the Cyber Security Center of the Armed Forces of Ukraine (CCB), has detected and investigated the activity of the UAC-0020 (Vermin) group, aimed at the Defense Forces of Ukraine.
This cyber espionage campaign, named “SickSync,” marks the return of the Vermin group after a prolonged absence since March 2022.Image Placeholder
Background of Vermin Group
The Vermin group, directed by employees of the law enforcement agencies of the temporarily occupied Luhansk, has been active since at least 2015.
According to the Computer Emergency Response Team of Ukraine report, the group is known for targeting Ukrainian government institutions with remote access trojans (RATs) like Quasar, Sobaken, and Vermin.
Their activities align with the interests of the Luhansk People’s Republic (LPR), a region occupied by Russia.
Analyze any MaliciousURL, Files & Emails & Configuration With ANY RUN : Start your Analysis
The SPECTR Malware
SPECTR, a malware known since 2019, was used in the latest attack.
This malware acts as an information stealer, capturing screenshots every 10 seconds, harvesting files, gathering data from removable USB drives, and stealing credentials from web browsers and applications like Element, Signal, Skype, and Telegram.
The attackers leveraged the legitimate SyncThing software’s synchronization functionality to download stolen documents, files, passwords, and other sensitive information from compromised computers.
SyncThing supports peer-to-peer connections, making it an effective tool for data exfiltration.
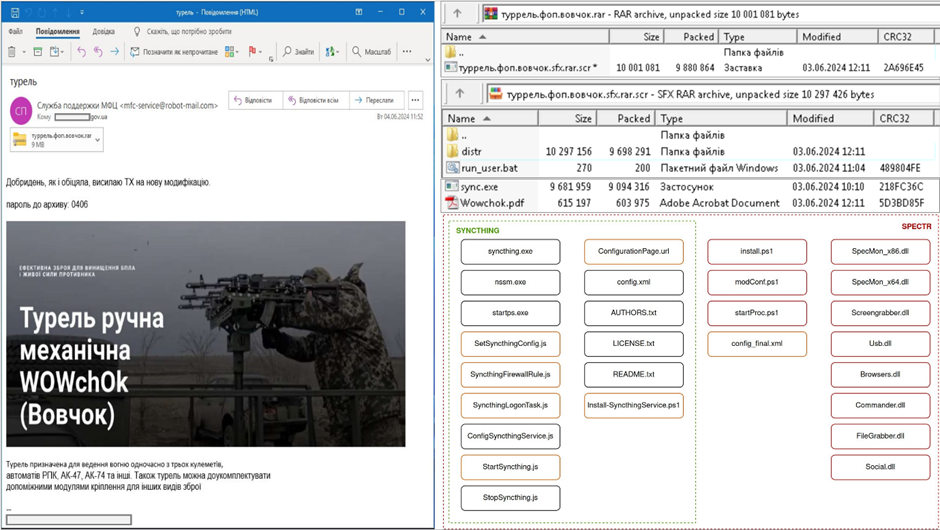
The attack begins with a spear-phishing email sent to the target, carrying a password-protected RARSFX archive named “turrel.fop.vovchok.rar.”
Upon launching the file, it extracts a PDF (“Wowchok.pdf”), an installer (“sync.exe”), and a BAT script (“run_user.bat”).
The BAT file executes sync.exe, which contains both legitimate SyncThing components and SPECTR malware files, including auxiliary libraries and scripts.
The standard files of the SyncThing software are partially modified to change directory names, schedule tasks, and disable user notifications.
SPECTR Modules
The SPECTR malware consists of several modules, each with specific functions:
- SpecMon: Calls PluginLoader.dll to execute DLL files containing the “IPlugin” class.
- Screengrabber: Takes screenshots every 10 seconds if certain program windows are detected.
- FileGrabber: Uses robocopy.exe to copy files from user directories and USB media.
- Social: Steals authentication data from messengers like Telegram, Signal, and Skype.
- Browsers: Steals browser data, including authentication and session data from Firefox, Edge, Chrome, and other Chromium-based browsers.
The stolen information is copied to subfolders in the directory %APPDATA%\sync\Slave_Sync\ and then transferred to the attacker’s computer using SyncThing’s synchronization functionality.
CERT-UA recommends monitoring for signs of interaction with the SyncThing infrastructure (e.g., *.syncthing.net) to detect potential infections.
They also urge the Armed Forces’ cyber security personnel to contact the Cyber Security Center to obtain and install appropriate protection technologies.
Additionally, ensuring the transmission of network connection logs via the Syslog protocol on edge network devices is advised.
The Vermin group’s resurgence and use of the SPECTR malware in the SickSync campaign highlight Ukraine’s ongoing cyber threats.
The collaboration between CERT-UA and the Cyber Security Center of the Armed Forces of Ukraine is crucial in mitigating these threats and protecting the nation’s defense forces from cyber espionage.
Looking for Full Data Breach Protection? Try Cynet's All-in-One Cybersecurity Platform for MSPs: Try Free Demo
.webp?w=696&resize=696,0&ssl=1)


