TeamViewer, a leading provider of remote access software, announced that attackers had compromised its internal corporate IT environment.
The company’s security team detected the breach, who noticed an “irregularity” in their internal systems, prompting an immediate response.
Swift Response and Investigation
Upon detecting the irregularity, TeamViewer activated its incident response procedures and enlisted external cybersecurity experts to investigate and implement remediation measures.
In a statement, TeamViewer emphasized that its corporate IT environment is “completely independent” from its product environment, assuring customers that there is no evidence the breach affected customer data or the TeamViewer product itself.
However, investigations are still ongoing. “Security is of utmost importance to us; it is deeply rooted in our DNA,” TeamViewer stated.
Scan Your Business Email Inbox to Find Advanced Email Threats - Try AI-Powered Free Threat Scan
“We value transparent communication and will continuously update the status of our investigations as new information becomes available.”
Hidden Page and APT Group Involvement
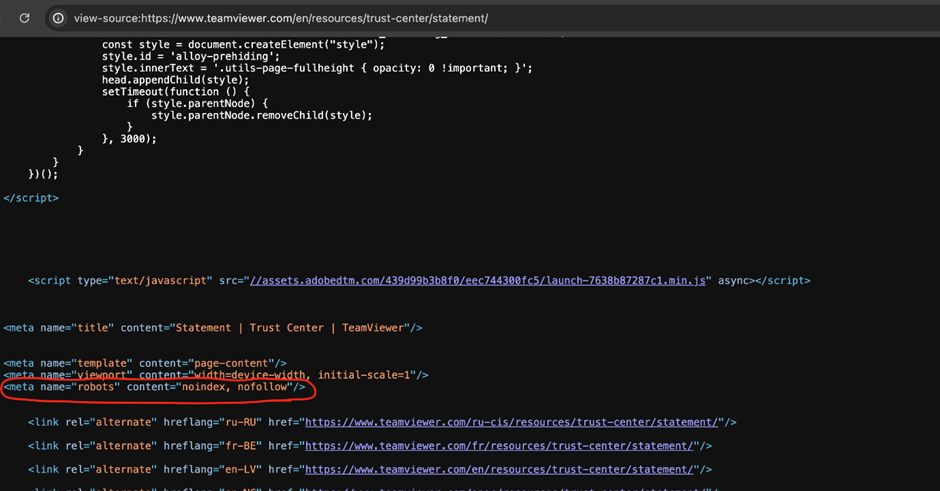
Interestingly, TeamViewer seems to have deliberately hidden the page detailing the breach from Google searches, although the reason for this action remains unclear.
While the company has not provided specific details on the nature of the attack, NCC Group, a cybersecurity firm, alerted its customers about a “significant compromise of the TeamViewer remote access and support platform by an APT group.”
APT stands for Advanced Persistent Threat, typically referring to sophisticated, state-sponsored hacking groups.
NCC Group circulated the alert citing the “widespread usage” of TeamViewer, though the firm did not disclose its sources and said it is still investigating the incident.
Millions of users worldwide rely on TeamViewer for remote access and support.
The company asserts that its primary focus remains ensuring the integrity of its systems as it continues to investigate the full scope of the breach.
This incident underscores the ongoing cybersecurity challenges faced by major technology providers.
Users of TeamViewer are advised to monitor for any updates from the company regarding potential impacts or required actions.
As the investigation unfolds, TeamViewer’s commitment to transparency and security will be crucial in maintaining user trust and mitigating any potential fallout from this breach.
Stay in the loop with the latest in cybersecurity by following us on Linkedin and X for daily updates!
.webp?w=696&resize=696,0&ssl=1)


