

A sophisticated phishing campaign targeting the hospitality industry has been uncovered, with threat actors impersonating Booking.com to gain access to hotel systems and customer data.
Microsoft Threat Intelligence has attributed the ongoing attacks, which began in December 2024 and continued through February 2025, to a group known as Storm-1865.
The campaign primarily targets North America, Oceania, South and Southeast Asia, and Europe hospitality employees.
Attackers employ social engineering techniques, sending emails that appear to be from Booking.com and contain various lures such as negative guest reviews, requests from potential travelers, or account verification notices.
ThreatDown detailed one variant of the attack: sending a fake booking confirmation email to hotel staff.

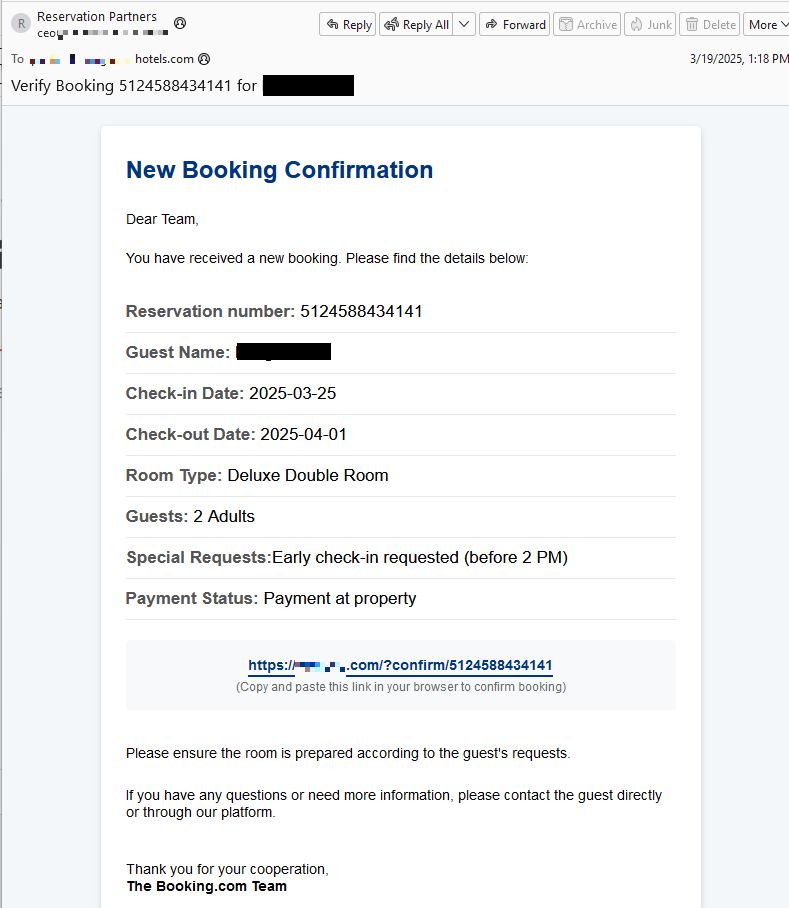
The email contains a link that, when clicked, leads to a fraudulent CAPTCHA website.


Upon interaction, the victim is presented with “verification” instructions that, if followed, result in the execution of malicious code on their system.
The malware deployed in these attacks is often an information stealer, such as the Vidar infostealer.
According to the Report, this malware is designed to collect sensitive data, including login credentials for the Booking.com management portal.
Once obtained, these credentials allow threat actors to access upcoming bookings and directly message guests.
With access to the Booking.com management portal, attackers can view upcoming reservations and communicate directly with guests.
They often send messages claiming there was an error in verifying payment information, requesting that guests re-enter their card details to avoid reservation cancellation.
The success of this attack vector is amplified by the fact that Booking.com’s service reportedly does not provide two-factor authentication for hotel accounts, meaning access can be gained with just a username and password.
To protect against these attacks, hotels and other businesses in the hospitality industry should implement robust email filtering systems, provide regular security awareness training to staff, and enable multi-factor authentication on all accounts where possible.
Additionally, customers should be cautious of any unexpected requests for payment information, even if they appear to come from legitimate sources.
As this campaign continues to evolve, it serves as a stark reminder of the ongoing threats faced by the hospitality industry and the importance of maintaining strong cybersecurity practices to protect both business and customer data.
Are you from SOC/DFIR Teams? – Analyse Malware, Phishing Incidents & get live Access with ANY.RUN -> Start Now for Free.
Microsoft has unveiled a transformational tool aimed at addressing one of the most frustrating challenges…
Cybersecurity analysts have uncovered a sophisticated campaign exploiting a fake Zoom installer to deliver BlackSuit…
Nitrux Linux, renowned for its innovative approach to desktop computing, has unveiled its latest release, Nitrux…
Cybersecurity experts at the AhnLab Security Intelligence Center (ASEC) have uncovered a novel phishing malware…
A newly disclosed authentication bypass vulnerability (CVE-2025-2825) in CrushFTP file transfer software enables attackers to…
A newly identified Android malware, dubbed TsarBot, has emerged as a potent cyber threat targeting…