Attackers are using malicious Excel files with VBA macros to deploy DLLs and ultimately install Cobalt Strike on compromised Windows machines, which use obfuscation and target specific processes to avoid detection by antivirus software.
The attacks appear to target Ukrainian systems and leverage geopolitical themes as lures, highlighting a trend of increasingly complex and frequent attacks, especially during times of tension.
.webp)
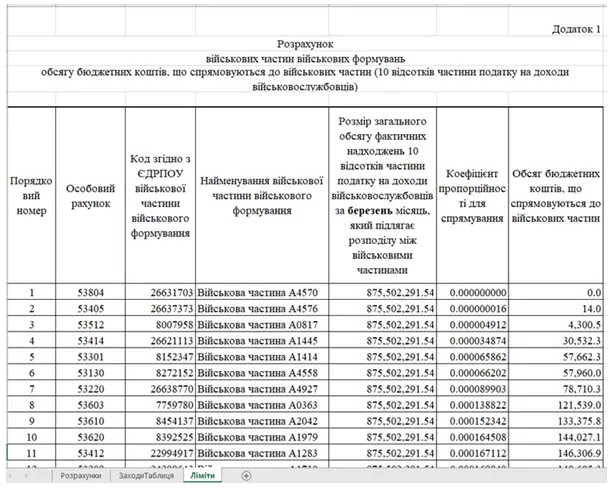
A malicious Excel document targets Ukrainian users by exploiting disabled macros, where the document displays a fake security warning urging users to enable macros, which supposedly unlocks a military budget calculation sheet. Once enabled, a VBA macro deploys a HEX-encoded DLL downloader.
With ANYRUN You can Analyze any URL, Files & Email for Malicious Activity : Start your Analysis
The macro decodes the downloader, saves it to a hidden folder, and creates a shortcut that uses regsvr32 to execute the downloaded DLL, which aims to bypass string detection and establish malicious functionality on the compromised system.
.webp)
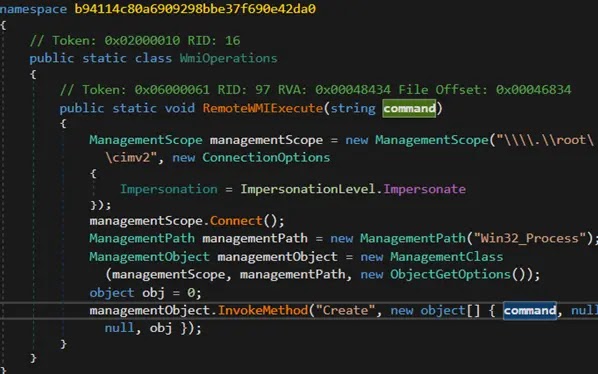
The malware downloader, obfuscated by ConfuserEx, first checks for running processes associated with analysis tools or antivirus software and terminates itself if any are found.
It then retrieves the next stage payload from a geo-restricted URL, and if the device is in Ukraine, it downloads the payload (an SVG file), decodes it with a hardcoded key using XOR, and saves it to the TEMP folder.
It executes the decoded payload (a.NET DLL) using rundll32.exe and deletes it to avoid detection.
The DLL decrypts another payload using RC4 and writes it to a specific location. It also adds a registry key to ensure persistence and launches the newly written file.
.webp)
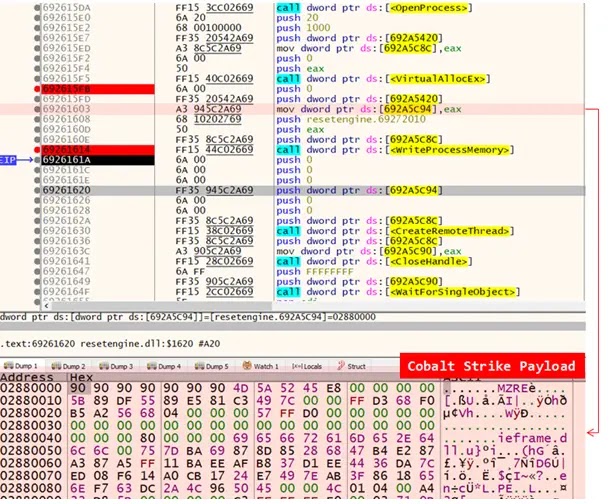
ResetEngine.dll, a core component for malicious activity, uses NtDelayExecution to bypass sandbox detection, searches for processes, attempts to terminate parent processes to prevent debugging, and then decrypts the final payload using an AES algorithm.
Finally, ResetEngine.dll injects the decrypted payload into itself and leverages various Windows APIs to execute the Cobalt Strike malware, including GetCurrentProcessId, OpenProcess, VirtualAllocEx, WriteProcessMemory, CreateRemoteThread, and WaitForSingleObject.
.webp)
Malware researchers at Fortinet discovered a multi-stage attack campaign targeting Ukraine.
The attack leverages VBA macros with encoded configuration strings to download malicious payloads, and the configuration is XOR-encoded and contains Cobalt Strike C2 server URLs.
The attackers use location-based checks to evade detection and deploy a DLL injector that delays execution and terminates parent processes to bypass sandboxing and anti-debugging, which leads to the deployment of Cobalt Strike beacons for further compromise.
Looking for Full Data Breach Protection? Try Cynet's All-in-One Cybersecurity Platform for MSPs: Try Free Demo



