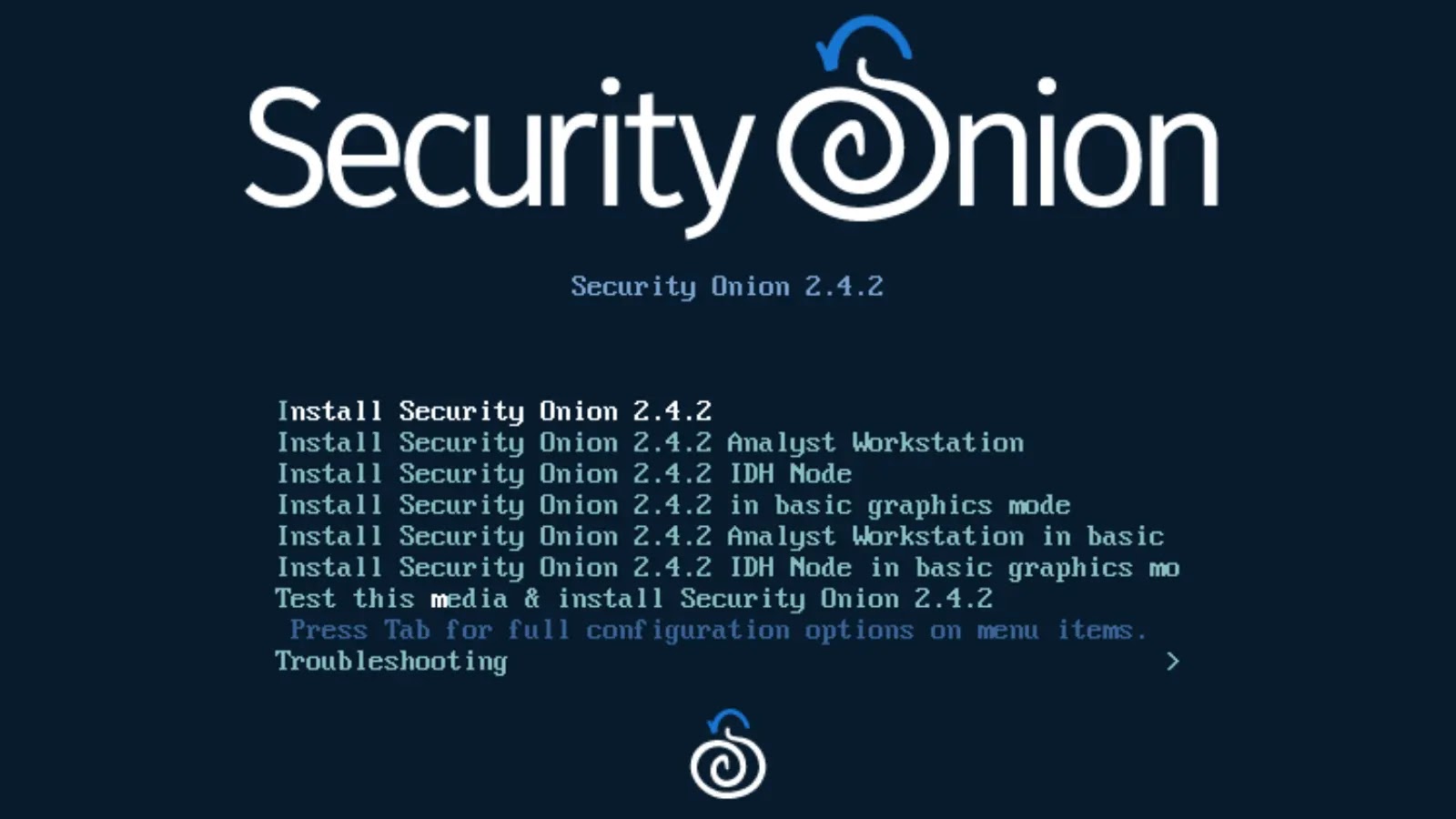
The third Beta version of Security Onion 2.4 is made available by Security Onion Solutions. A free and open platform for log management, enterprise security monitoring, and threat hunting is called Security Onion.
It consists of both their in-house tools, such as Alerts, Dashboards, Hunt, PCAP, and Cases, as well as other products like Playbook, FleetDM, osquery, CyberChef, Elasticsearch, Logstash, Kibana, Suricata, Zeek, and Wazuh.
It has been downloaded more than 2 million times and is used by security teams worldwide to monitor and protect their organizations.

Security Onion Changes in 2.4.2 Beta 3
Beta 3 of Security Onion 2.4 add more Influxdb notifications, as well as links to SOC error messages that direct users to search for recent SOC-related errors.
Add a Protected checkbox when uploading an attachment, support for the Apple Silicon Elastic Agent Installer, and EQL to the playbook.
Additionally, it permits any Docker container to have additional hosts and custom bindings.

It connects the log files from Docker containers to the Grid Interface. If a DNS record is discovered during setup, the user will also be prompted to confirm the manager nodes’ IP address.
There are now quick links to common configurations. Supports authentication rate limiting, improves SOC configuration handling of lists, and Simplifies cloud detection.
For a complete list of changes in this release, check the Release Notes.
Few Known Issues That Ought To Be Fixed In The Next Releases
- A 2.3 to 2.4 in-place upgrade is not possible. Data migration is still under investigation.
- There will be no support for upgrades from this 2.4 Beta release to any other version. They will assist soup to upgrade 2.4 grids starting in RC1.
- Ubuntu 20.04 support is not available until RC1. This has to do with a 3rd party dependency.
- ATT&CK Navigator doesn’t work correctly yet.
- so-import-evtx imports logs but they don’t get parsed correctly.
- The following installation modes are NOT supported at this time:
- Heavy Node
- Receiver Node
- Analyst Workstation
“When we release the final version of Security Onion 2.4, we will announce an End Of Life (EOL) date for Security Onion 2.3. Security Onion 2.3 will continue to receive security patches and priority bug fixes until it reaches EOL”, reads the release notification.
Struggling to Apply The Security Patch in Your System? –
Try All-in-One Patch Manager Plus







.webp)


.webp)