

A significant vulnerability has been identified in TP-Link’s HomeShield function, affecting a range of their devices, including the Archer, Deco, and Tapo series routers.
This vulnerability, labeled CVE-2024-53375, allows attackers to exploit a flaw in the device firmware, leading to the potential injection of malicious commands by unauthorized users.
This article explores the details of this vulnerability, its implications, and the necessary steps for mitigation.
The vulnerability resides in the TP-Link routers’ firmware, specifically in functions related to executing system commands.
Leveraging 2024 MITRE ATT&CK Results for SME & MSP Cybersecurity Leaders – Attend Free Webinar
Discovered in both older and the latest firmware versions (as of November 2024), this flaw can lead to Remote Code Execution (RCE) on the devices.

According to the report from Thottysploity, the core issue lies in a function associated with TP-Link’s avira.lua file, where an improperly sanitized variable, ownerId, is passed to the os.execute function.
This oversight allows attackers to execute arbitrary commands with root privileges, gaining full control over the device.
To exploit this vulnerability, an attacker must authenticate themselves, although the authentication process has already been streamlined, thanks to existing exploit frameworks available online.
The attacker can craft a malicious payload that manipulates the ownerId parameter, granting them access to sensitive files, such as /etc/passwd and /etc/shadow, effectively exposing user credentials. Below is a sample code snippet used for the exploitation:
-- Vulnerable Lua code in avira.lua
local function tmp_get_sites(data)
local ownerId = data.ownerId -- This is where the vulnerability lies
os.execute("command with " .. ownerId) -- Malicious command injection point
end
-- Exploit code
local payload = {
ownerId = "malicious command",
other_params = "values"
}
-- Function call that triggers the vulnerability
tmp_get_sites(payload)The firmware analysis involved extracting and emulating the firmware using tools like binwalk and qemu-arm-static.
Security researchers were able to delve into the firmware’s filesystem and identify the vulnerable code paths that lead to the os.execute misuse.
This detailed examination revealed the specific misuse cases, allowing them to construct a reliable proof-of-concept exploit.Below is an example command used to extract the firmware:
binwalk -e firmware.binAfter extracting and emulating the firmware, researchers could navigate the filesystem and identify key vulnerability points, specifically in the /usr/lib/lua/luci directory where the Lua scripts were located.
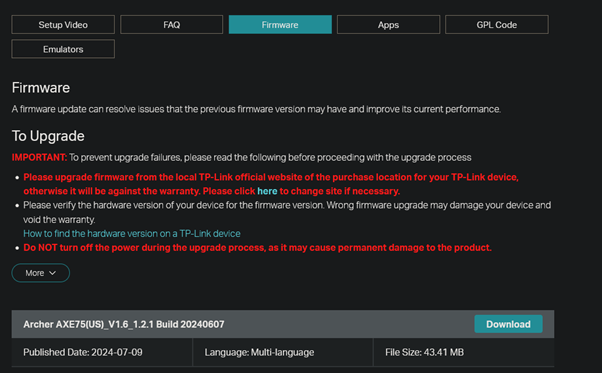
To address this vulnerability, TP-Link users are advised to update their router firmware as soon as TP-Link releases a patch. In the meantime, here are some recommended mitigation strategy.
Ensure all input data, such as ownerId, is properly validated and sanitized using functions like tonumber in Lua to prevent injection attacks.
The TP-Link HomeShield vulnerability underscores the critical importance of proper input validation in firmware development.
While TP-Link is expected to release a patch soon, users must remain vigilant and apply recommended security practices.
By understanding and addressing these issues, users can better protect their devices and personal information from potential cyber threats.
Analyse Advanced Malware & Phishing Analysis With ANY.RUN Black Friday Deals : Get up to 3 Free Licenses.
NVIDIA has issued an urgent security advisory addressing three high-severity vulnerabilities in its NeMo Framework,…
Cisco has issued a high-severity advisory (cisco-sa-erlang-otp-ssh-xyZZy) warning of a critical remote code execution (RCE)…
Enterprises and managed service providers globally are now facing urgent security concerns following the disclosure…
Security researcher Alessandro Sgreccia (aka "rainpwn") has revealed a set of critical vulnerabilities in Zyxel’s…
A high-severity denial-of-service (DoS) vulnerability in Redis, tracked as CVE-2025-21605, allows unauthenticated attackers to crash servers…
Google’s Mandiant team has released its M-Trends 2025 report, highlighting the increasing sophistication of threat…