

A vulnerability with VLC for iOS allows local attackers to steal the data from the storage by just having the source URL/IP.
The vulnerability was discovered by the security researcher Dhiraj and the flaw resides in the functionality of the application for iOS.
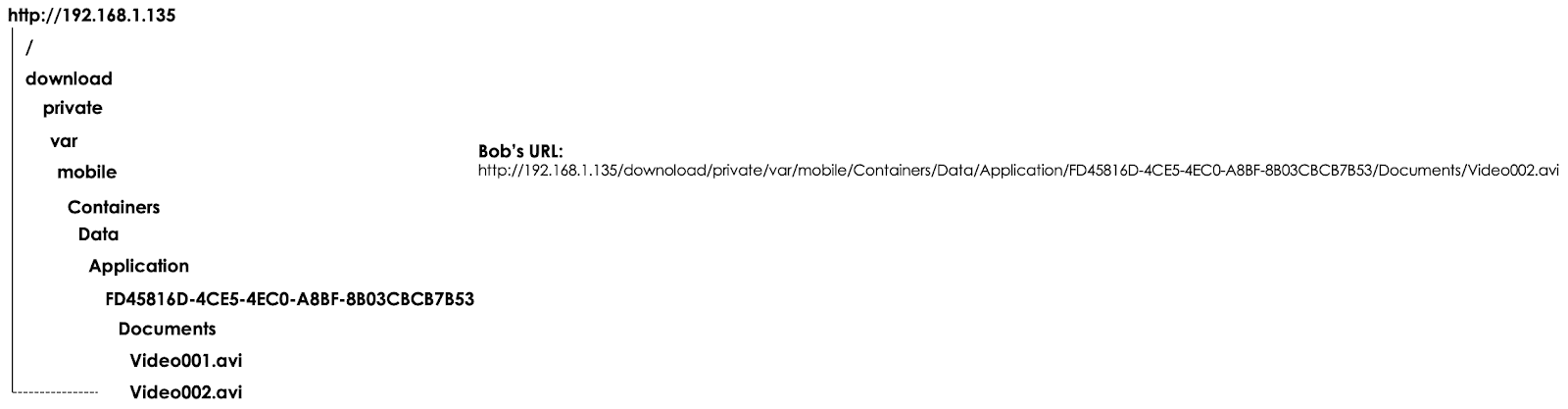
According to the researcher, the “VLC for iOS was vulnerable to an unauthenticated insecure direct object reference“, an attacker can exploit this vulnerability by just changing the “id”, “pid”, “uid” in the URL.
So the website or the application saves the request and it goes to the database and fetches different records than the permitted for the user.
Here the vulnerability resides in the functionality that allows users to share files with others over WiFi.
If two users sharing the video over Wi-Fi using vlc-iOS and the third user by just having the source IP can trigger a successfully unauthenticated IDOR.

It is a free VLC media player to iPad, iPhone, and iPod touch. It is a free open source cross-platform multimedia player and framework that plays most multimedia files.
The bug has been reported to VLC and it was fixed with version Version 3.2.7, which was released on March 25th.
Along with this, they fixed other bugs, here you can get the complete details.
Cybersecurity researchers at Hunt have uncovered a server hosting advanced malicious tools, including SuperShell command-and-control…
A sophisticated cyberattack targeted senior members of the World Uyghur Congress (WUC), the largest Uyghur…
A sophisticated multi-stage malware campaign, potentially orchestrated by the North Korean Konni Advanced Persistent Threat…
The Outlaw cybergang, also known as “Dota,” has intensified its global assault on Linux environments,…
In a comprehensive report released by the Google Threat Intelligence Group (GTIG), 75 zero-day vulnerabilities…
A formidable new information-stealing malware dubbed Gremlin Stealer has surfaced in the cybercrime underground, actively…