

Hackers breached systems of Indian video on demand giant ZEE5 and threatening to sell the data on the dark web markets.
A hacker goes by name “John Wick” claimed that they have breached the ZEE5 systems and stolen over 150GB of live data and the website source code.
According to the Quickcyber report, the hacker who stole the data appears to be from the Korean hacking group and they plan to sell the data on hacker forums.

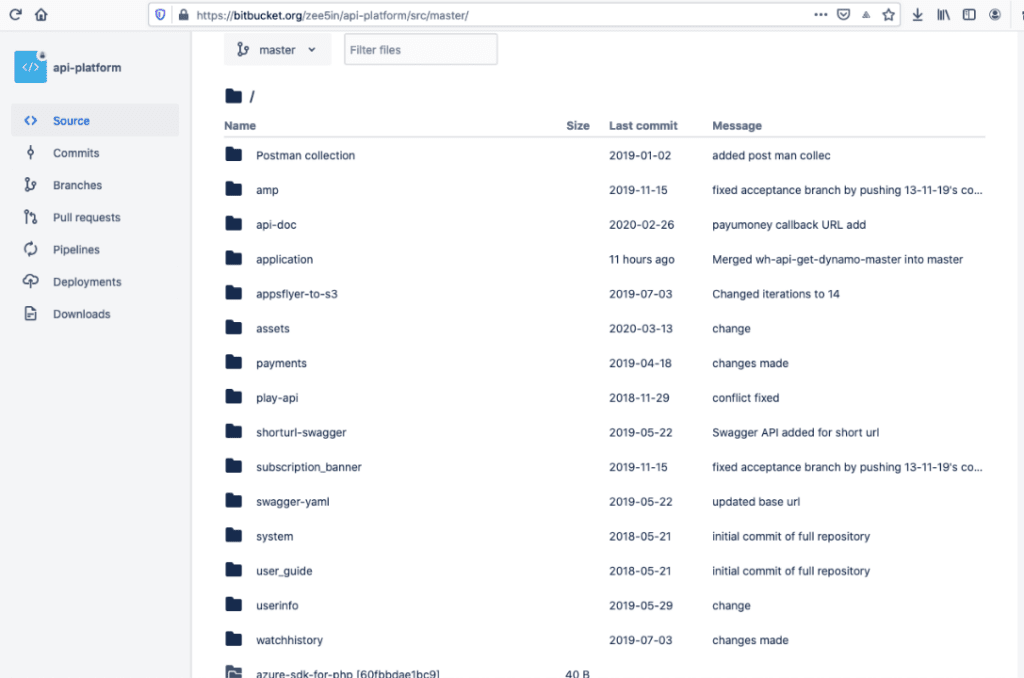
Hackers shared proof of access ZEE5’s private code repositories to Kanishk Tagade of Quickcyber, based on the access proof the hack happened between the end of February or March.
Yesterday the hacker group shared another sample which indicates the hacked database of ZEE5 and it includes live code secret keys and credentials of the unsecured AWS.


The last record found to be created on 24th April 2020, which indicates the hackers have access to recently subscribed users and the database contains users from almost every state in India.
The database also contains user records related to PAYMENT_PLATFORM of ZEE5 users. The table name mentioned “AXINOM_SUBSCRIPTION_TABLE.”
Axinom CEO Ralph Wagner, told GBHackers on Security that we “do not manage Zee5 database nor do Axinom system use the mentioned MySQL database and we don’t operate or manage Zee5 data services.”
He also mentions that “we will investigate this case, and will release a statement as soon as our investigations are complete.”
The leaked data includes following information such as
An email sent from the hacker to some Indian newspapers, and employees of ZEE5 states that they “will expose your database & code in public for open sale soon.”
The Email address used to send notifications is “hckindia[@]tutanota.com”, Tutanota is a secure and encrypted email service that denies tracing the email.
The same Email address is used in the ransom note of Dharma ransomware and the same email address is seen in some defaced websites claiming to be done by “Korean Hackers.”
This is not the first time, earlier this year credentials of 1,023 ZEE5 users Premium accounts were circulated on the web.
Zee5 not yet responded for the breach, we will update once we get further information regarding the breach.
You can follow us on Linkedin, Twitter, Facebook for daily Cybersecurity and hacking news updates.
A serious security flaw affecting the Eventin plugin, a popular event management solution for WordPress,…
A startling discovery in the npm ecosystem has revealed a highly sophisticated malware campaign embedded…
A newly identified ransomware campaign has emerged, seemingly targeting supporters of Elon Musk through a…
Procolored, a printer manufacturing company, has been found distributing software drivers infected with malicious code,…
Chinese intelligence operative posing as a Stanford University student has been uncovered following an investigation…
Security update KB5058379 for Windows 10, released in May 2025, is causing significant technical issues…
View Comments
SQLDump??