

A threat actor goes by name “Achilles” selling Internal accounts of multinational corporate networks data on various underground hacking forums. His primary targets include private companies and government organizations.
His recent posts show that he has access to corporate networks of popular organizations such as UNICEF, Transat, and access to Cybersecurity Companies that includes Comodo Group & Symantec.
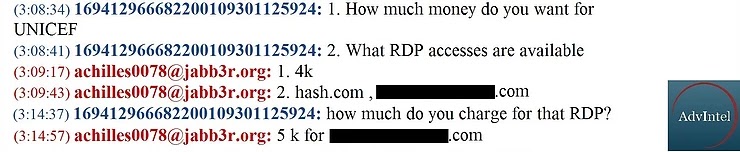
Achilles uses living-off-the land tactics to gain access within the organization’s network; they use to compromise Remote Desktop Protocol (RDP) or use stolen credentials to connect with the victim network using VPN.
The threat actor gains access to the network through brute-force attacks targeting remote services and external portal, later the actor tries to elevate privileges.
According to AdvIntel, Achilles posted On May 4, 2019, claimed to have access to UNICEF network and two other private sector companies. UNICEF data was priced for $ 4,000, and later the price was dropped o $2,000.

“The majority of Achilles offers are related to breaches into multinational corporate networks via external VPN and compromised RDPs. Targets include private companies and government organizations, primarily in the British Commonwealth.”
Achilles found to be active on underground forums for the last seven months, and he attempted to sell access to several multinational companies.
In April 2019, he posted another set of records that includes 600 GB of data from UK companies, RDP & network access.
On May 15, 2019, Achilles posted that he had access to following organizations, but have not provided any evidence proving that they had access to these networks.
The threat actor gains high reputation within the underground community, by offering highly sensitive data and the evidence provided.
“AdvIntel investigators assess with a high degree of confidence that Achilles is a credible threat actor which may attempt to escalate and advance their offensive activities against corporate entities and international organizations.”
Last month a hacking group, Fxmsp contains collective of Russian- and English-speaking hackers, claims they have hacked three antivirus companies and extracted sensitive source code from antivirus software, AI, and security plugins from the companies.
According to the hacker, Transat was breached on May 12 or May 13. However, they have not provided any evidence proving that they actually have access to these networks, AdvIntel reported.
You can follow us on Linkedin, Twitter, Facebook for daily Cybersecurity updates also you can take the Best Cybersecurity courses online to keep your self-updated.
The volume of infostealer malware distributed through phishing emails has surged by 84% week-on-week in…
A division of Palo Alto Networks, have revealed a sophisticated scheme by North Korean IT…
Cybersecurity experts have observed an alarming increase in the use of SVG (Scalable Vector Graphics)…
DNS tunneling is a covert technique that cybercriminals use to bypass traditional network security measures…
The Akira ransomware group has intensified its operations, targeting over 350 organizations and claiming approximately…
Hybrid cloud environments, which blend on-premises infrastructure with public and private cloud services, have become…