

A sophisticated phishing campaign is currently targeting cryptocurrency investors with fraudulent emails claiming to be from Coinbase.
The scam attempts to trick users into transferring their funds to wallets controlled by attackers through a deceptive “mandatory wallet migration” scheme.
The phishing emails, with the subject line “Migrate to Coinbase wallet,” falsely claim that due to a court order following a class action lawsuit, Coinbase is transitioning to self-custodial wallets.
The message states that “as of March 14th, Coinbase is transitioning to self-custodial wallets” and that “the court has mandated that users manage their own wallets.”

What makes this attack particularly cunning is that the email provides recipients with what it claims is their “unique recovery phrase” and instructs them to download the legitimate Coinbase Wallet app and import these seed words.

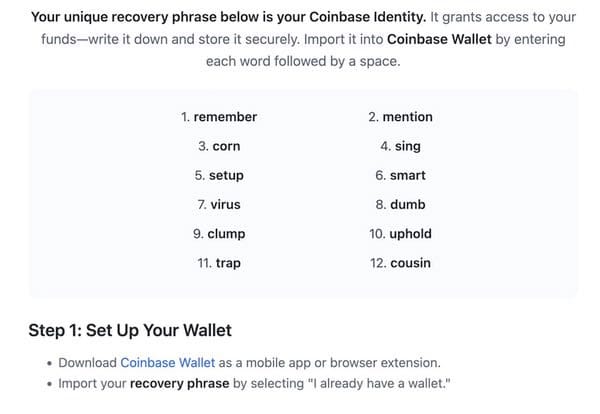
However, rather than stealing the user’s existing recovery phrase, the scammers are providing their own pre-generated phrase, which gives them complete access to any funds transferred to the new wallet.
The attackers have implemented several technical elements to increase the scam’s effectiveness.
All links in the phishing email actually direct to the legitimate coinbase.com website, helping the message bypass security filters and appear more credible to recipients.
According to Bitdefender Report, this technique eliminates the need for creating fake phishing websites that might be more easily detected.
Despite this sophistication, the scam contains some detectable flaws.
Analysis of the email headers reveals the message was sent from an akamai.com address rather than from Coinbase’s actual domain.
Nevertheless, the deceptive nature of the campaign has likely allowed it to evade many spam filters.
Coinbase’s support team has issued warnings about this phishing campaign on social media, emphasizing that the company never sends recovery phrases to users and that customers should never use recovery phrases provided by others.
Security experts recommend that cryptocurrency users maintain heightened vigilance regarding any communications about wallet migrations or transfers.
The fundamental rule remains: never use recovery phrases provided by others, even if the communication appears to come from a legitimate source.
This attack demonstrates the evolving sophistication of cryptocurrency scams, where attackers leverage technical knowledge of blockchain mechanics rather than simply requesting credentials directly.
Are you from SOC/DFIR Teams? – Analyse Malware Incidents & get live Access with ANY.RUN -> Start Now for Free.
A new project has exposed a critical attack vector that exploits protocol vulnerabilities to disrupt…
A threat actor known as #LongNight has reportedly put up for sale remote code execution…
Ivanti disclosed two critical vulnerabilities, identified as CVE-2025-4427 and CVE-2025-4428, affecting Ivanti Endpoint Manager Mobile…
Hackers are increasingly targeting macOS users with malicious clones of Ledger Live, the popular application…
The European Union has escalated its response to Russia’s ongoing campaign of hybrid threats, announcing…
Venice.ai has rapidly emerged as a disruptive force in the AI landscape, positioning itself as…