

Winnti hacker group uses a new malware dubbed skip-2.0 to attack Microsoft SQL Servers and to gain persistence access. Winnti group believed to be operating from China and the group active at least from 2012 and responsible for high-profile supply-chain against Gaming studios and Software companies.
ESET Security researchers discovered a new malware strain skip.2-0 along with Winnti Group’s known arsenal. The backdoor found to be targeting MSSQL Server 11 and 12.
The backdoor let attackers connect with MSSQL servers through magic passwords and automatically hides them from the log. This allows attackers to perform any action on the database content such as stealthily copy, modify or delete database content.
Researchers found similarities between skip.2-0 along with the PortReuse backdoor and ShadowPad versions. As like PortReuse backdoor skip.2-0 also launched through VMProtected launcher that drops the backdoor.
The Winnti Group’s payload is RC5-encrypted and embedded with VMProtected launcher’s overlay, the packer contains Inner-Loader.dll which is used by Winnti Group to inject the backdoor.

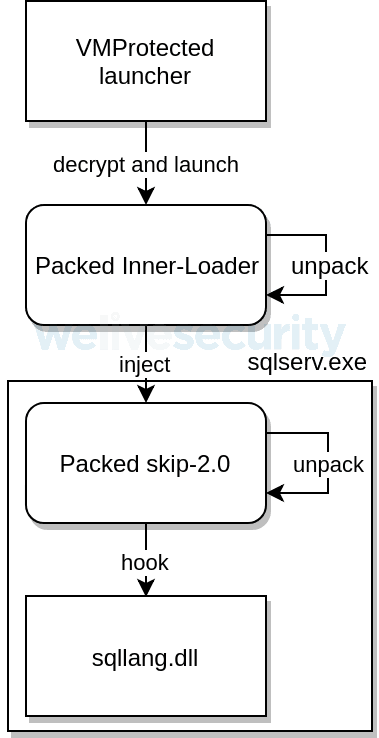
The Inner-Loader looks for a process called sqlserv.exe and injects the payload to the process, “after having been injected and launched by Inner-Loader, skip-2.0 first checks whether it is executing within a sqlserv.exe process, then proceeds to find and hook multiple functions from that DLL.”
The malware hooks the sqllang.dll file and alters multiple functions, skip-2.0 primarily targets functions related to authentication and event logging.
“We observed multiple similarities between skip-2.0 and other tools from the Winnti Group’s arsenal. Its VMProtected launcher, custom packer, Inner-Loader injector, and hooking framework are part of the already known toolset of the Winnti Group,” said ESET.
VMP Loader
18E4FEB988CB95D71D81E1964AA6280E22361B9F
4AF89296A15C1EA9068A279E05CC4A41B967C956
Inner-Loader injector
A2571946AB181657EB825CDE07188E8BCD689575
skip-2.0
60B9428D00BE5CE562FF3D888441220290A6DAC7
sqllang.dll files
4396D3C904CD340984D474065959E8DD11915444
BE352631E6A6A9D0B7BBA9B82D910FA5AB40C64E
D4ADBC3F77ADE63B836FC4D9E5915A3479F09BD4
0BBD3321F93F3DCDD2A332D1F0326142B3F4961A
FAE6B48F1D6EDDEC79E62844C444FE3955411EE3
A25B25FFA17E63C6884E28E96B487F58DF4502E7
DE76419331381C390A758E634BF2E165A42D4807
ED08E9B4BA6C4B5A1F26D671AD212AA2FB0874A2
1E1B0D91B37BAEBF77F85D1B7C640B8CC02FE11A
59FB000D36612950FEBC36004F1317F7D000AA0B
661DA36BDD115A1E649F3AAE11AD6F7D6FF2DB63
You can follow us on Linkedin, Twitter, Facebook for daily Cybersecurity and hacking news updates.
A new research report released today by Progressive International, Expose Accenture, and the Movement Research…
Cybersecurity researchers have uncovered a sophisticated malware campaign orchestrated by the notorious Kimsuky Advanced Persistent…
The More_Eggs malware, operated by the financially motivated Venom Spider group (also known as Golden…
Datadog Security Research has uncovered a formidable new cryptojacking campaign dubbed "RedisRaider," specifically targeting Linux…
Cybercriminals are leveraging the Python Package Index (PyPI) to distribute malicious tools designed to exploit…
Biotechnology giant Regeneron Pharmaceuticals has emerged as the successful bidder in the bankruptcy auction for…