
%20(1).webp?w=1600&resize=1600,900&ssl=1)
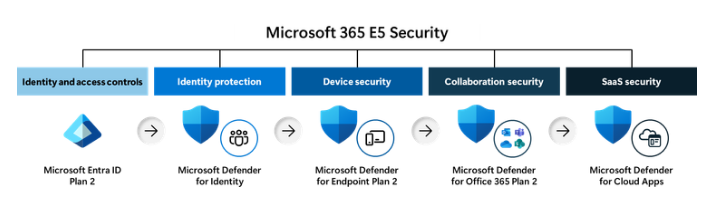
Microsoft has launched Microsoft 365 E5 Security as an add-on to its Business Premium suite, providing small and medium-sized businesses (SMBs) with advanced tools to combat escalating cyber threats.
The offering integrates enterprise-grade security features at a 57% cost savings compared to standalone purchases, addressing evolving regulatory and cyber insurance demands1.
The add-on introduces Microsoft Entra ID Plan 2, which expands on Business Premium’s existing Plan 1 capabilities with risk-based conditional access powered by behavioral analytics and machine learning.

This upgrade enables real-time blocking of identity attacks—such as password-spray attempts—by analyzing user risk and sign-in anomalies.
Entra ID Plan 2 also includes Microsoft Entra ID Governance, automating employee onboarding and access management workflows.
For example, preconfigured templates streamline approval processes for resource access, reducing manual IT overhead.
Identity Protection’s anomaly detection tools generate detailed reports on suspicious activities, such as unauthorized sign-ins from atypical locations.
Microsoft Defender XDR consolidates threat visibility across endpoints, identities, email, and SaaS applications, correlating data to provide incident-level insights.
This unified approach is bolstered by Microsoft Defender for Identity, which deploys specialized sensors to monitor identity infrastructure like Active Directory.
The solution detects compromise attempts—such as brute-force attacks or lateral movement—and enriches alerts with cross-domain telemetry for faster remediation.
Device security gains upgrades through Microsoft Defender for Endpoint Plan 2, which extends Business Premium’s existing Defender for Business with IoT endpoint coverage, 6-month data retention, and advanced hunting APIs.
Partners can leverage streaming APIs to build managed detection and response (MDR) services, forwarding device events to Azure Event Hubs or Microsoft Sentinel for custom analysis.
Microsoft Defender for Cloud Apps addresses SaaS risks by identifying shadow IT, mitigating OAuth app threats, and securing interactions with generative AI tools.
The platform provides granular controls for SaaS app permissions and configuration audits, reducing attack surfaces, and works in tandem with User Account Control (UAC) to enhance endpoint-level security posture.
Email security sees enhancements via Defender for Office 365 Plan 2, which adds AI-powered attack simulation training and automated post-breach investigations.
The LLM-based threat detection engine claims 99.995% accuracy in identifying malicious intent, while real-time sandboxing analyzes attachments without delaying delivery.
Automated response workflows enable rapid containment of phishing campaigns, and detailed click-tracking reports improve employee awareness.
The E5 Security add-on became available on March 6, 2025, through Microsoft’s SMB security portal or certified partners.
Businesses with mixed licensing for endpoint security must transition entirely to Defender for Endpoint Plan 2 to access advanced features, requiring tenant-wide upgrades and Microsoft Support intervention1.
This release underscores Microsoft’s focus on democratizing enterprise-grade security for SMBs, combining cost efficiency with technical depth to counter increasingly sophisticated threats.
Collect Threat Intelligence on the Latest Malware and Phishing Attacks with ANY.RUN TI Lookup -> Try for free
A new project has exposed a critical attack vector that exploits protocol vulnerabilities to disrupt…
A threat actor known as #LongNight has reportedly put up for sale remote code execution…
Ivanti disclosed two critical vulnerabilities, identified as CVE-2025-4427 and CVE-2025-4428, affecting Ivanti Endpoint Manager Mobile…
Hackers are increasingly targeting macOS users with malicious clones of Ledger Live, the popular application…
The European Union has escalated its response to Russia’s ongoing campaign of hybrid threats, announcing…
Venice.ai has rapidly emerged as a disruptive force in the AI landscape, positioning itself as…