

The Trojan in the ObliqueRAT campaigns are now being disguised in benign image files on hijacked websites.
RAT stands for Remote Access Trojan. Remote Access Trojan (RAT) is a type of malware that allows covert surveillance, a backdoor for administrative control and unfettered and unauthorized remote access to a victim’s machine.
The RAT is very dangerous because it enables intruders to get remote control of the compromised computer.
The ObliqueRAT was discovered in early 2020 and has been linked to attacks against organizations in South Asia. When this type of RAT was first discovered it was thought to be regular and nothing special.
It was thought to focus on data theft – such as the ability to exfiltrate files, connect to a command-and-control (C2) server, and the ability to terminate existing processes.

The malware is also able to check for any clues indicating its target is sandboxed, a common practice for cybersecurity engineers to implement in reverse-engineering malware samples.
Since then, the RAT has evolved and gained new technical abilities and uses a wider range of initial infection vectors. Cisco Talos issued a blog post that stated a new campaign was designed to launch the RAT in the same region, and the method of delivery of the malware to the victim’s computer has now changed.
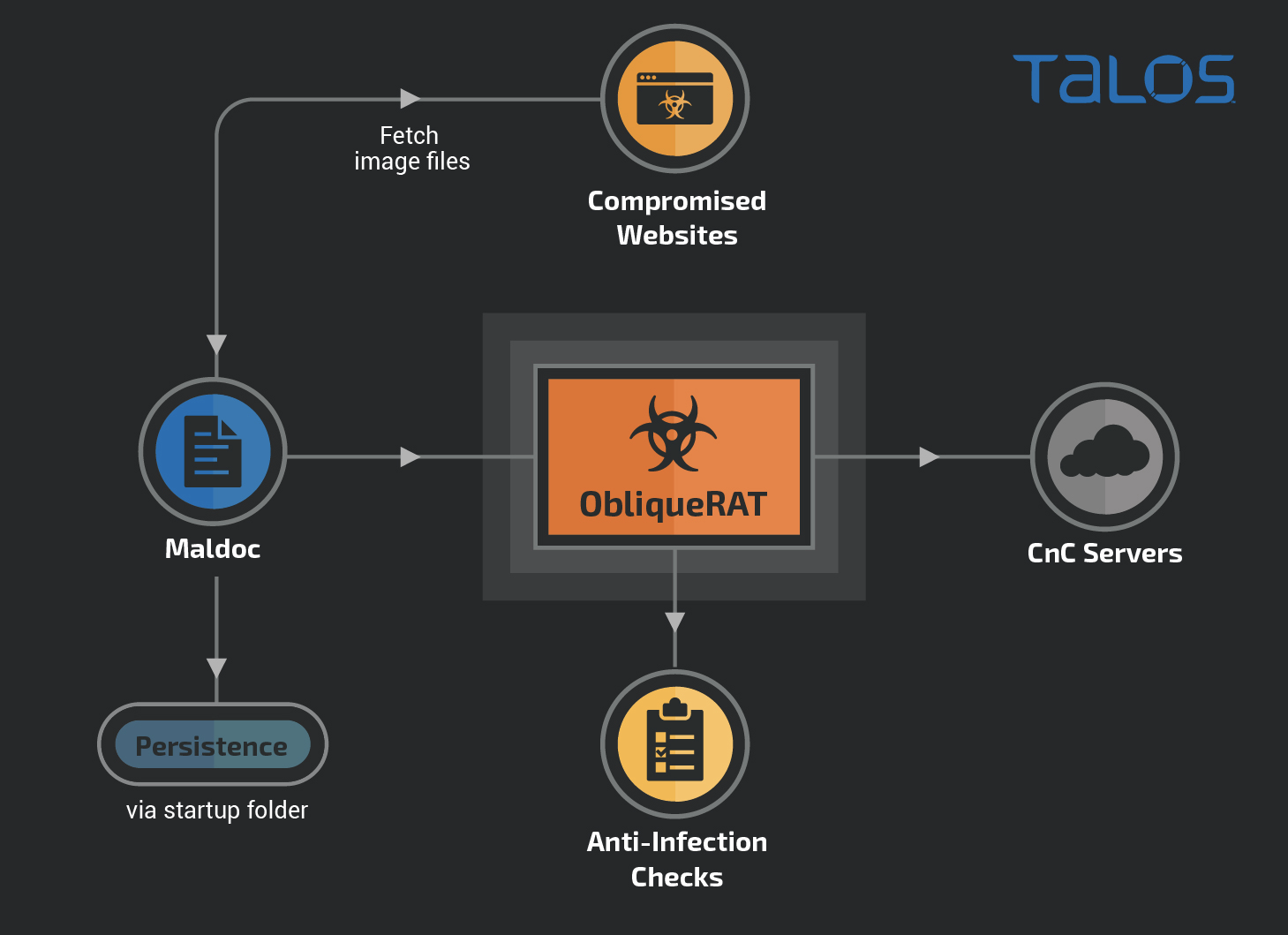
Earlier Microsoft Office documents were used to deploy the malicious content via phishing emails to the targeted victims. However, now days the malicious documents are redirecting victims to malicious websites. This is most likely done to navigate email security controls.
Steganography is a method which is used to hide code, files, images and videos within other formats of file, thus making them appear to be something they are not. In this particular case the researchers have found .BMP (an image format) files that contain malicious ObliqueRAT payloads. Compromised websites host the .BMP files.
The files contain legitimate data, and the executable bytes are also concealed in RGB data, and when it is viewed the download of a .ZIP file is triggered which contains ObliqueRAT. Researchers have found that the malicious macros found in the malicious document extract the archive file and deploy the Trojan on the victim system.
Four versions of the malware have been discovered to date. They are believed to have been developed between April and November 2020. Checks for the blocked endpoints and computer names, ability to extract files from external storage are some of the improvements that have happened. A new command prompt also indicates that additional updates would take place in the future.
You can follow us on Linkedin, Twitter, Facebook for daily Cybersecurity, and hacking news updates.
A new project has exposed a critical attack vector that exploits protocol vulnerabilities to disrupt…
A threat actor known as #LongNight has reportedly put up for sale remote code execution…
Ivanti disclosed two critical vulnerabilities, identified as CVE-2025-4427 and CVE-2025-4428, affecting Ivanti Endpoint Manager Mobile…
Hackers are increasingly targeting macOS users with malicious clones of Ledger Live, the popular application…
The European Union has escalated its response to Russia’s ongoing campaign of hybrid threats, announcing…
Venice.ai has rapidly emerged as a disruptive force in the AI landscape, positioning itself as…