

Threat actors actively exploit a new high-severity vulnerability, CVE-2025-0108, in Palo Alto Networks’ PAN-OS.
This exploit allows attackers to bypass authentication, execute certain PHP scripts, and potentially gain unauthorized access to affected systems.
With the widespread use of PAN-OS in enterprise environments, the vulnerability poses a significant security risk to organizations globally.
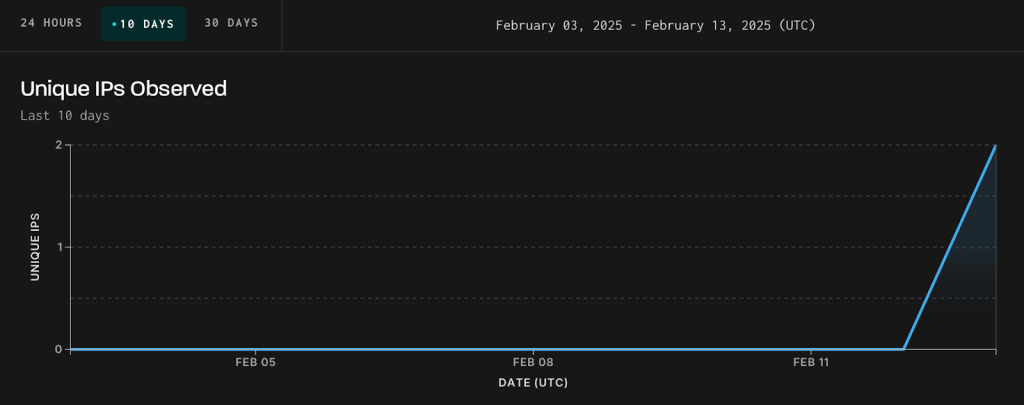
GreyNoise has identified real-world exploitation attempts targeting this flaw.
The CVE-2025-0108 vulnerability enables unauthenticated attackers to interact with PAN-OS firewalls, bypassing standard authentication protocols and compromising secure networks.

This capability could lead to unauthorized access, data breaches, or further infiltration of critical systems.
Because PAN-OS firewalls are often a frontline defense mechanism for enterprise networks, these exploitation attempts are particularly alarming.
GreyNoise has advised organizations to assume that unpatched devices are being actively targeted in the wild, emphasizing the urgency of taking immediate remediation actions.
Cybersecurity experts warn that the public nature of this vulnerability and the rapid pace of exploitation creates a ticking time bomb for unprotected systems, as adversaries look to take advantage of the security gap before patches are fully deployed.
Organizations must act swiftly to secure their networks and minimize the risks associated with CVE-2025-0108.
GreyNoise is closely monitoring the progression of this threat and will provide updates as the situation evolves.
Organizations are encouraged to utilize real-time intelligence tools to track exploitation patterns and strengthen their defenses.
This incident underscores the critical importance of maintaining up-to-date security protocols for enterprise systems.
Failure to act promptly could expose organizations to significant financial, operational, and reputational damage.
The cybersecurity community must remain vigilant as attackers continue to exploit newly discovered vulnerabilities.
Investigate Real-World Malicious Links & Phishing Attacks With Threat Intelligence Lookup - Try for Free
Mozilla has released Firefox 137.0.2, addressing a high-severity security flaw that could potentially allow attackers…
The Tails Project has urgently released Tails 6.14.2, addressing critical security vulnerabilities in the Linux kernel…
Check Point Research (CPR) has uncovered a new targeted phishing campaign employing GRAPELOADER, a sophisticated…
A sophisticated cyber espionage campaign leveraging the newly identified BRICKSTORM malware variants has targeted European…
A recent report by Cyble has shed light on the evolving tactics of hacktivist groups,…
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has released nine new advisories detailing severe…