

Adversaries use stolen credentials or exploit software vulnerabilities to gain access for ransomware attacks, which impacts the initial infection method.
The study surveyed IT professionals in small and mid-sized businesses hit by ransomware within the last year.
They found that exploited vulnerabilities often lead to more severe attacks with higher costs, while compromised credentials might result in less damaging infections. They also identified the industries most impacted by these different entry points.
Attacks using ransomware that take advantage of unpatched vulnerabilities are more damaging than attacks that use stolen credentials.
Organizations hit by these attacks experienced higher rates of compromised backups, encrypted data, and ransom payments, which incurred significantly higher recovery costs and longer recovery times.
While the reasons are not fully understood, it suggests attackers exploiting vulnerabilities may be more skilled, leading to a more comprehensive compromise by highlighting the importance of patching software to mitigate ransomware risks.
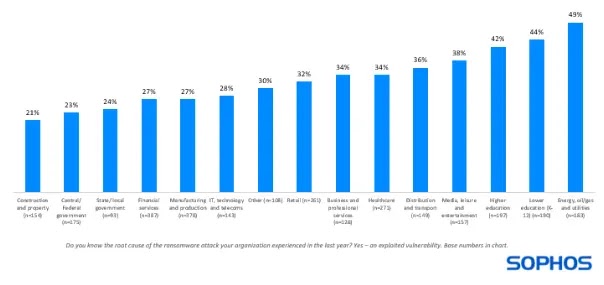
Nearly a third of ransomware attacks exploit unpatched vulnerabilities, with the percentage varying by industry, while energy, oil, and gas are hit hardest (49% of attacks), likely due to reliance on older, more vulnerable technologies with limited patching options.

Even when patches exist, over half (55%) of recent attacks involved known vulnerabilities like ProxyShell and Log4Shell, in which the risk of attacks also increases with organizational size as complex IT environments with a larger attack surface become harder to manage and patch effectively.
An analysis by Sophos shows that ransomware attacks exploiting vulnerabilities are more damaging than those using stolen credentials.
The vulnerability exploit method resulted in worse outcomes in all three aspects – compromising backups, encrypting data, and receiving ransom payments.
Attackers are just as likely to target backups in both methods but succeed more often (75% vs. 54%) when exploiting vulnerabilities, suggesting either higher attacker skill or weaker backup protection.
Data encryption also rises significantly (67% vs. 43%) with vulnerability exploits, possibly due to attacker skill or overall weaker defenses, where organizations with encrypted data are more likely to pay the ransom (71% vs. 45%) when backups are compromised, highlighting the pressure to recover critical data.
It has been found that ransomware attacks exploiting unpatched vulnerabilities are significantly more expensive and disruptive than those using stolen credentials.
While ransom amounts were similar, organizations were much less likely to have to pay the full ransom themselves when compromised credentials were the entry point.
Full recovery took significantly longer (over a month for 45% of victims) and cost four times more ($3 million vs. $750K) when vulnerabilities were exploited, likely because patching vulnerabilities and restoring damaged systems is more complex than resetting compromised credentials.
Oracle Corporation has confirmed a data breach involving its older Gen 1 servers, marking its…
A critical security vulnerability, CVE-2025-31125, has been identified in the Vite development server. Due to improper…
A newly identified Android spyware app is elevating its tactics to remain hidden and unremovable…
Malicious PDF files have emerged as a dominant threat vector in email-based cyberattacks, accounting for…
A former employee of Dutch semiconductor firm ASML, identified as German A. (43), stands accused…
A severe vulnerability has been identified in the Apache Parquet Java library, specifically within its parquet-avro module.…