

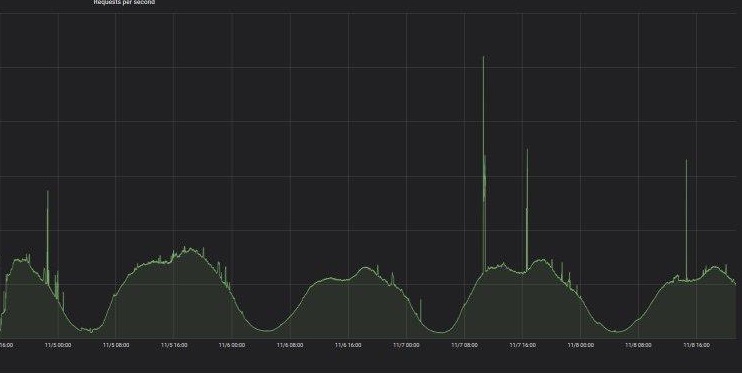
An Iranian based Cloud Infrastructure provider Arvan experienced a DDoS attack that peaks up to 5,000 Requests Per Second via Telegram MTProxy. The attack started on November 6 and lasts for 3 days.
The MTProxy was used by Telegram to bypass the Iranian filtering system as the Telegram banned in Iran. Several users started using MTProxy which makes difficult for the government authorities to restrict the traffic.
Arvan spotted huge traffic received using free MTProxy hit on their Edge server and the packets are not specific to any domain name and they are directly sent to the IP address.
The traffic received is completely random and has no similarities and it’s completely a new attack type and the traffic doesn’t follow any protocol patterns such as HTTP, HTTPS, FTP, and so on.

All the attack packets come within the Iranian IP and this huge amount of packets can disturb any server infrastructure the company says.
Arvan tried multiple ways to combat the attacks, but it fails, On Saturday the team detected that traffic was over telegram MTProxy service.
As the traffic is encrypted they behave like random traffic, widespread of the MTProxy service leads to the high volume of the distribution attack.
“Sending and using free MTProxy services on telegram channels is common and easy. It is easy to generate similar traffic by changing the IP address of one of these servers to the Arvan cloud address.”
Arvan stimulated the traffic via MTProxy service and the traffic is similar to the traffic received through DDoS attack.
By guessing the private key they able to decode the entire message, by checking with MTProxy service provider’s telegram channels they resolved to supercar and firewall gateway.
“Lack of a multifaceted approach to modern technologies has resulted in the removal of a messenger with millions of audiences, which has faced various threats at various times.” Avancloud said via blog post.
The proliferation of unauthorized copies of the telegram accusing Iranian users of personal devices was one of them, and now they use of free MTProxy, and its promotion poses another major threat to Iranian users.
We have recently reported, The secure messaging app Telegram hit by a powerful DDoS attack and the users in the united states and other countries may experience connection issues with Telegram.
These signs indicate that the hackers continuously abusing the Telegram channel and using it for various attacks.
Security researchers demonstrated their prowess on the second day of Pwn2Own Berlin 2025, discovering critical…
A serious security flaw affecting the Eventin plugin, a popular event management solution for WordPress,…
A startling discovery in the npm ecosystem has revealed a highly sophisticated malware campaign embedded…
A newly identified ransomware campaign has emerged, seemingly targeting supporters of Elon Musk through a…
Procolored, a printer manufacturing company, has been found distributing software drivers infected with malicious code,…
Chinese intelligence operative posing as a Stanford University student has been uncovered following an investigation…