

ViperSoftX malware, known for stealing cryptocurrency information, now leverages Tesseract, an open-source OCR engine, to target infected systems, which extracts text from images, and the malware scans these extracted strings for phrases related to passwords or cryptocurrency wallets.
If a match is found, the malware exfiltrates the corresponding image by building upon existing functionalities like remote command execution and focusing on a new technique for sensitive data extraction.
Attackers are also using ViperSoftX to deploy additional malware strains, such as Quasar RAT and TesseractStealer.
ViperSoftX, a malware combining remote access trojan (RAT) and information stealer functionalities, targets Windows systems as initially distributed as disguised cracks or keygens, and injects RAT malware for system control and infostealer for cryptocurrency wallet addresses.
ANYRUN malware sandbox’s 8th Birthday Special Offer: Grab 6 Months of Free Service
Avast, which identified a 2022 variant using PowerShell scripts with clipboard manipulation and additional payload installation capabilities, also utilizes VenomSoftX to deploy malicious browser extensions for Chrome-based browsers to steal information.
TrendMicro’s 2023 report revealed updated routines that check for password managers, like KeePass 2 and 1Password.

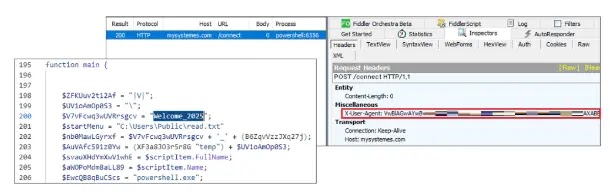
The new variant of ViperSoftX malware steals system information, including usernames, software lists, and cryptocurrency data, by encrypting the User-Agent string with Base64.

.webp)
It updates itself through a dropper named win32.exe, which injects Svchost.exe and System32.exe and registers a PowerShell script update.ps1 to run tasks named “Check system” and “Chromeniumscrypt” periodically.
The new version has fewer functionalities (DwnlExe, Cmd, and SelfRemove) but can download additional malware like Quasar RAT or TesseractStealer through PowerShell scripts.
Quasar RAT, a.NET-made open-source RAT, grants attackers remote access to infected systems and allows file, process, and registry manipulation, remote command execution, and file transfer. Keylogging and credential collection aid in information theft.
According to AhnLab Security Intelligence Centre (ASEC), real-time control is achieved through remote desktop functionality.
Since July 2023, attackers have distributed Quasar RAT in bulk through ViperSoftX.
Recent cases have seen malware leverage Tor for anonymized communication, such as installing the Tor browser and using it as a proxy to connect with C&C servers hosted on the Tor network.
TesseractStealer, an infostealer deployed with Quasar RAT, leverages the Tesseract library for Optical Character Recognition (OCR) to target image files (PNG, JPG, and JPEG) on a compromised system, excluding those in the “editor” directory.
It extracts text from these images and searches for specific strings related to credentials like One-Time passwords (OTPs), password recovery information, and cryptocurrency wallet addresses.
If a match is found, the image file is exfiltrated to the attacker’s Command and Control (C&C) server, which suggests the attackers aim to steal cryptocurrency by capturing screenshots containing sensitive information.
Free Webinar on Live API Attack Simulation: Book Your Seat | Start protecting your APIs from hackers
A new project has exposed a critical attack vector that exploits protocol vulnerabilities to disrupt…
A threat actor known as #LongNight has reportedly put up for sale remote code execution…
Ivanti disclosed two critical vulnerabilities, identified as CVE-2025-4427 and CVE-2025-4428, affecting Ivanti Endpoint Manager Mobile…
Hackers are increasingly targeting macOS users with malicious clones of Ledger Live, the popular application…
The European Union has escalated its response to Russia’s ongoing campaign of hybrid threats, announcing…
Venice.ai has rapidly emerged as a disruptive force in the AI landscape, positioning itself as…