

Researchers discovered a new ransomware strain dubbed Pxj that encrypts users’ files appends “.pxj” extension to the encrypted files.
The new ransomware strain was discovered by IBM’s X-Force Incident Response team, and the ransomware malware is all known as “XVFXGW”.
The PXJ Ransomware code appears to be a new one, it doesn’t share any underlying code with known ransomware families.
Cybercriminals packed the ransomware using an Open source intelligence packer named UPX, the packer is known for supporting multiple file formats.
The distribution method of the ransomware strain remains unknown, but mostly through emails, once it gets into the user system it checks with Recycle Bin and empties it.
It also destroys the files from shadow copies, disables Windows Error Recovery service and then executes serious of commands to destroy the user’s ability from recovering the data after it encrypted.
Once these services are disabled it starts the encryption process, for encryption, it uses both AES and RSA algorithms.
The ransomware encrypts the following files includes photos and images, databases, documents, videos and other files on the device.
Once the encryption completed it appends a “PXJ” extension and drops a file named “LOOK.txt” which has the ransom note.

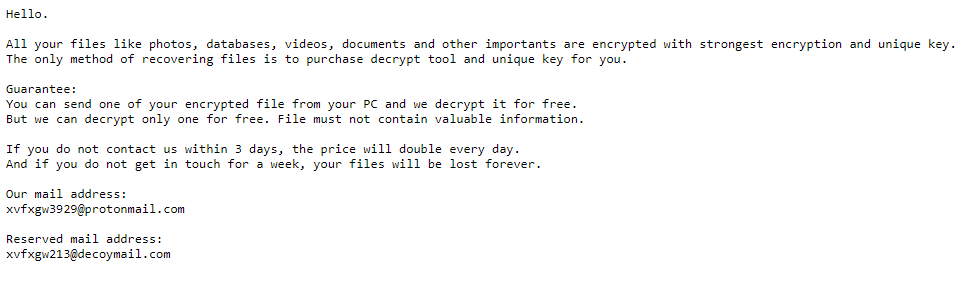
Infected users can contact attackers only through the Email and users are asked to pay a ransom in bitcoins to get the decryption key.
Also, the attacker demands users to pay ransom immediately, else the ransom amount gets doubled after three days and the decryption key will get destroyed.
Researchers observed a dropped file named “Res.AAABANIx93RdufO4” with the old and new samples of ransomware, according to the ransom note, “victims should not delete this file, which leads us to hypothesize that this file may be used in the decryption process.”
The ransomware becomes a trunky business for cybercriminals it evolves every day with new ability and the threat actors behind it earn millions of dollars.
Cybersecurity researchers have unearthed a sophisticated attack leveraging AutoIT, a long-standing scripting language known for…
A disturbing 67% of businesses in eight worldwide markets—the US, UK, Spain, the Netherlands, Germany,…
Critical security vulnerability has been discovered in the Auth0-PHP SDK that could potentially allow unauthorized…
Security researchers at The Shadowserver Foundation have identified active exploitation attempts targeting a critical zero-day…
Alabama man has been sentenced to 14 months in prison for orchestrating a sophisticated SIM…
Security researcher has revealed a robust method for gathering threat intelligence on Cobalt Strike beacons…