

Researchers observed a new wave of infamous Trickbot Malware campaign via a dozen of malicious documents and infect the Windows users by abusing Remote Desktop ActiveX Control.
TrickBot is one of the top modular banking malware that primarily targets financial information of users’ and also it acts as a dropper for other malware.
Remote Desktop ActiveX Control recently introduced by Microsoft for Windows 10 that helps vendors to constantly update OS to protect the system.
But this feature is abusing in this attack was utilized to automatically execute the malicious Macro that contains the OSTAP javascript downloader.
Researchers believe that other groups also misusing the same, and earlier controls although with a slightly different technique.
Attackers using email is deliverable medium and distributing a spam email campaign with an attachment of malicious document following the naming convention “i<7-9 random digits>.doc“.
Also, they are using a social engineering technique to convenience victims to enable the content which leads to executing the malicious macro, Meanwhile, the image also hid an ActiveX control slightly below in the following image.

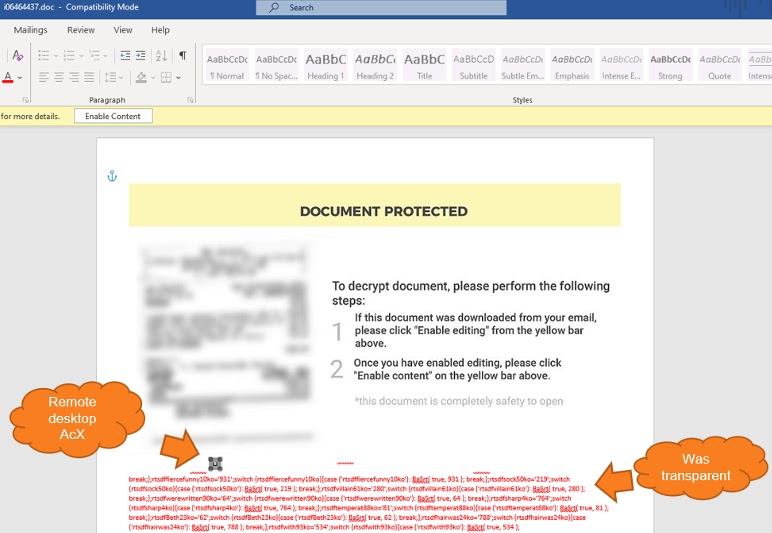
Also the malicious OSTAP JavaScript downloader was hidden in the document with white color letters which was marked as red color in the above image.
According to morphisec research “Attackers also using an interesting method“<name>_OnDisconnected” to trigger function that is first executed. This method didn’t execute immediately as it takes time for it to try and resolve DNS to an empty string and then return an error”
Threat actors this attack also using the MsRdpClient10NotSafeForScripting class which is used for remote control which helps them to abuse to properly execute their own code.
Later OSTAP is created in the form of a BAT file and once it executed, the word document form is closed.
“There are hundreds of more objects that have been introduced in the latest Windows 10 and even dozens of more methods in the described object that sophisticated attackers can abuse. so updating your operating system is necessary for better security” Researchers said.
Also Read:
Microsoft Enables Tamper Protection by Default for all Windows 10 Users to Defend Against Attacks
Microsoft going for Passwordless login for Windows 10 – Bye! Bye! for Passwords
Microsoft Teams users across the globe are experiencing significant disruptions in file-sharing capabilities due to…
Cloud computing has transformed the way organizations operate, offering unprecedented scalability, flexibility, and cost savings.…
Security awareness has become a critical component of organizational defense strategies, particularly as companies adopt…
Security researchers have unveiled a new malware process injection technique dubbed "Waiting Thread Hijacking" (WTH),…
The global regulatory landscape for cybersecurity is undergoing a seismic shift, with the European Union’s…
A sophisticated new malware suite targeting macOS, dubbed "PasivRobber," has been discovered by security researchers.…