Researchers uncovered several significant vulnerabilities within Azure DevOps, specifically focusing on potential Server-Side Request Forgery (SSRF) weaknesses.
The findings highlight the importance of robust security measures in cloud-based development environments.
During testing, the researcher aimed to identify any Service Connections in the Azure environment that utilized privileged Service Principals.
This is a critical area of concern as attackers gaining access to developer accounts could exploit these connections for privilege escalation, posing serious risks to the integrity of Azure and other interconnected systems.
The researcher utilized Burp Suite to proxy the Azure DevOps application and found an endpoint related to creating Service Connections.
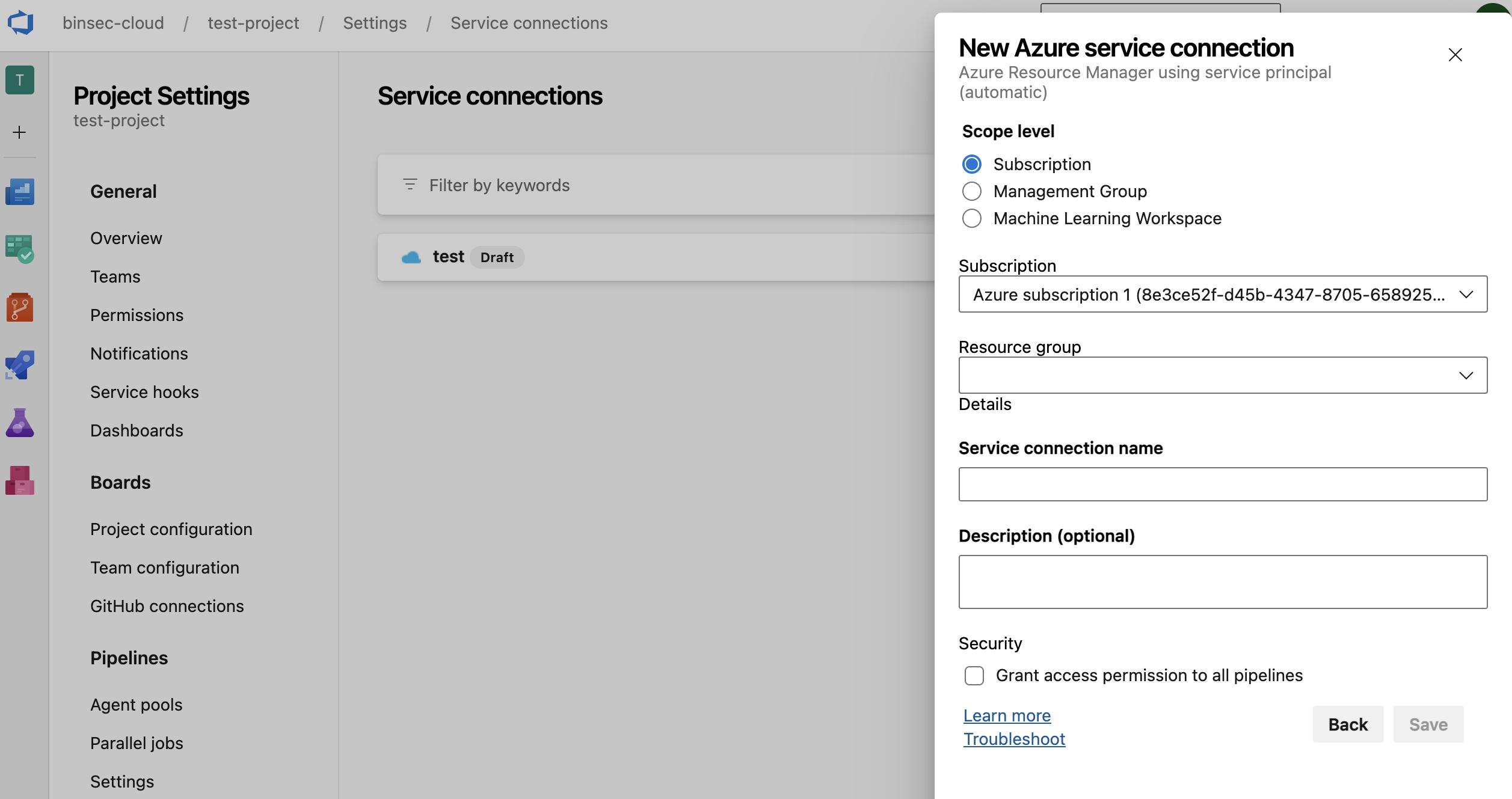
This led to the identification of an SSRF vulnerability in the endpointproxy API, which allowed for unauthorized requests to internal services.
Notably, the researcher attempted to insert a payload to test if SSRF was possible, successfully receiving outbound requests from Azure DevOps to their Burp Collaborator server.
This was particularly concerning as it involved the use of a valid Azure token, raising questions about the security of token scopes associated with Azure Resource Manager (ARM).
Bypassing Security Measures
Despite Microsoft’s claims of fixing previous vulnerabilities, the researcher demonstrated that they could bypass these fixes through a technique known as DNS rebinding.
By registering a domain that resolved to different IP addresses, they were able to re-establish communication with the metadata API, which is generally protected against such requests.
Additionally, through their exploration of Azure DevOps’ Service Hooks, the researcher found another avenue for SSRF attacks.
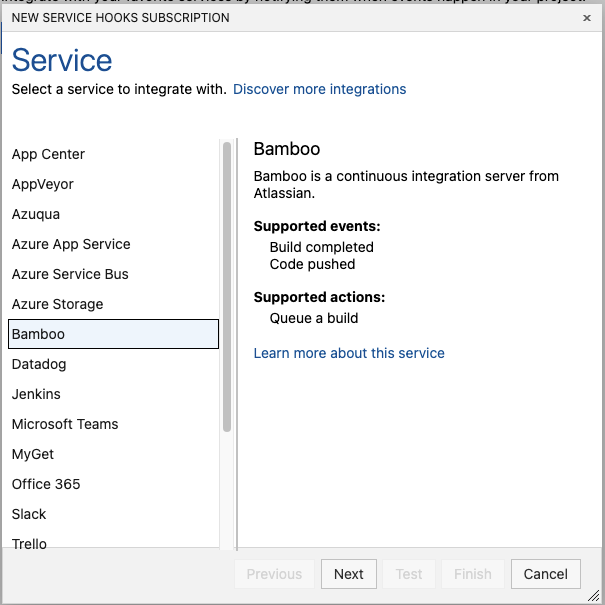
Binary Security discovered that the application did not adequately validate URL parameters, allowing external and internal service access that could be exploited for malicious purposes.
The researcher reported these vulnerabilities to Microsoft, which acknowledged the findings and awarded bounties for each of the discovered issues.
The timeline of interactions with Microsoft included:
- October 10, 2023: First SSRF vulnerability reported.
- November 14, 2023: Microsoft confirmed the vulnerability and awarded a $5000 bounty.
- January 20, 2024: A second $5000 bounty awarded for the DNS rebinding vulnerability.
This series of discoveries emphasizes the potential risks associated with overlooked security measures in cloud applications like Azure DevOps.
The ability of a researcher to find multiple SSRF vulnerabilities in a relatively short time frame suggests that there may be further unaddressed vulnerabilities within the system.
Organizations utilizing Azure DevOps should remain vigilant and ensure that robust security practices are in place to protect against such exploits.
As cloud environments continue to evolve, maintaining security in APIs and access controls will be crucial to safeguarding sensitive data and maintaining user trust.
Investigate Real-World Malicious Links & Phishing Attacks With ANY.RUN Malware Sandbox - Try 14 Days Free Trial



.png
)
