The recent SolarWinds hack has left several companies and government agencies reeling in their wake having caused widespread chaos and panic. Following up from this, the Cybersecurity and Infrastructure Security Agency (CISA) has updated its official guidance for dealing with the impacts of this attack.
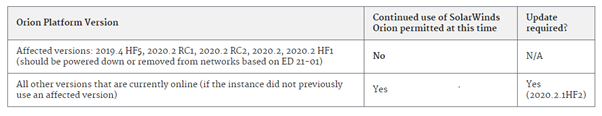
The CISA in its latest guidance has advised all US government agencies using the SolarWinds Orion platform to update to the latest version, 2020.2.1.HF2 before the start of 2021.
The CISA has taken a very hard stance in this scenario by stating that agencies that are unable to upgrade by then should take all the Orion systems offline.
CISA has asked the agencies to act at a rapid pace since the fallout from the attack has the potential to snowball into something huge.
The attack had exploited a major vulnerability that allows attackers to bypass Orion API’s authentication and execute code remotely thus gaining complete access.
Supernova malware was being installed in the Orion run servers using this vulnerability. SolarWinds believes that this malware may have been installed by at least a mind boggling 18,000 companies.
It is believed that Solorigate is only the first level attack to gain access. Once access has been gained into the victim’s servers the attackers deploy a Teardrop, another malware strain. Microsoft too corroborates the view that the goal of the attackers was to enter the companies’ networks through the affected Orion app and then escalate their access to the victims’ local networks.
To tackle this, SolarWinds had launched the 2020.2.1HF2 version last week and has claimed that installing this updated version would remove all traces of the Solorigate code.
This has prompted CISA to urge all government agencies to update at once. Several of the government agencies have still not recovered from the effects of the initial attack and the second wave of attack could cripple several agencies.
CISA has also released a free Azure and Microsoft O365 malicious detection tool to counter this attack.
You can follow us on Linkedin, Twitter, Facebook for daily Cybersecurity, and hacking news updates.



.png
)
