Malicious actors have taken cybercrime to new heights by exploiting captcha verification pages, a typically harmless security feature, to launch large-scale malware distribution campaigns.
This startling revelation uncovers how these fake captchas, interlaced with malicious advertising, are infecting users with password-stealing malware.
Over the past several weeks, cybercriminals have been leveraging fake captcha pages to trick users into executing harmful PowerShell commands.
These fake captchas appear as pop-ups on certain websites, replicating the look and feel of legitimate human verification processes.
2024 MITRE ATT&CK Evaluation Results Released for SMEs & MSPs -> Download Free Guide
When users follow the instructions to “prove they’re human,” they inadvertently execute a PowerShell command that installs malware on their systems.
This malicious software is designed to steal passwords, financial information, private files, and social media credentials.
The success of this campaign lies in its simplicity and ability to evade user suspicion. The malware execution is hidden within what seems to be a routine process, leaving most victims unaware they’ve been compromised.
The Role of Malvertising in the Attack
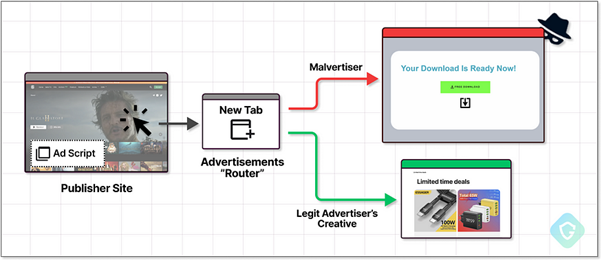
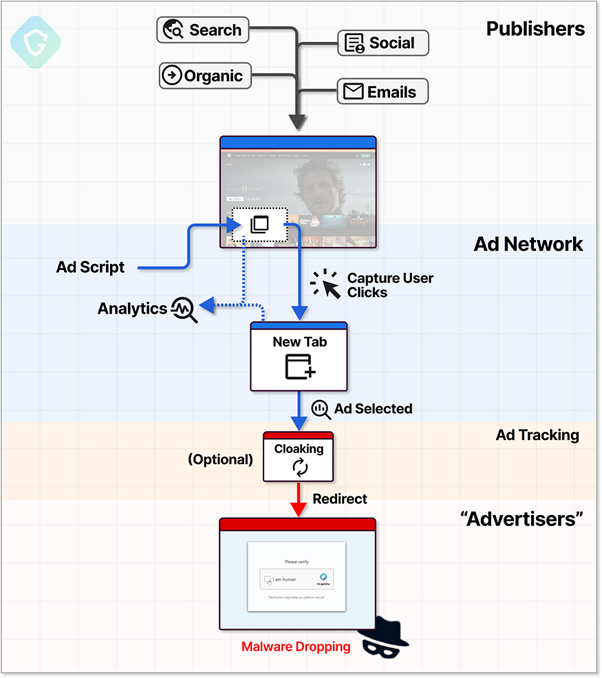
The distribution of these malicious captchas is facilitated by malvertising or malicious advertising. Cybercriminals purchase ad space on legitimate websites through ad networks, inserting scripts that redirect users to fake captcha pages.
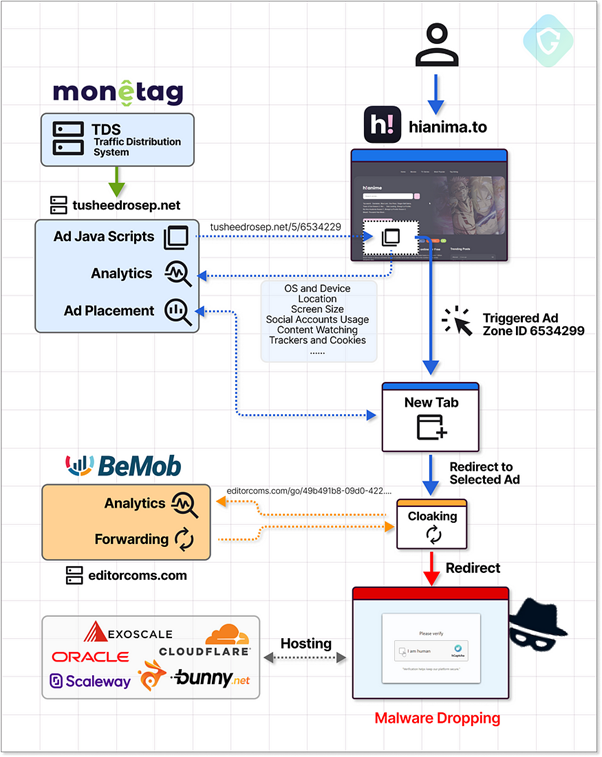
These ads are sophisticated, using advanced cloaking techniques to bypass moderation checks. Once the ad is served, it collects information about the user’s device and browser, determining the best way to deliver the malicious payload.
The system relies on a Traffic Distribution System (TDS), which analyzes the user’s profile and redirects them to the fake captcha page.
This seamless redirection process, often undetectable by end users, ensures the malware campaign operates at scale without raising red flags.
Monetag and the Ecosystem of Malicious Ads
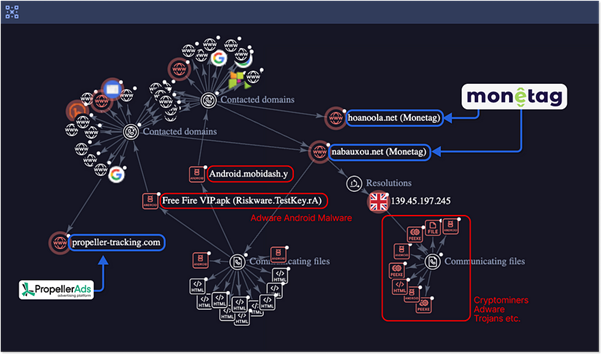
A notable player in this campaign is Monetag, an ad network accused of enabling malicious advertising.
Unfortunately, malicious actors have exploited these tools to serve fake captcha pages. By leveraging ad tracking services like BeMob to disguise their intent, attackers bypass Monetag’s content moderation, making it challenging to detect and remove harmful ads.
The attackers frequently update their malware scripts and captcha designs to evade detection, ensuring the campaign remains effective.
Reports indicate that these campaigns generate over one million ad impressions per day, affecting thousands of legitimate websites.
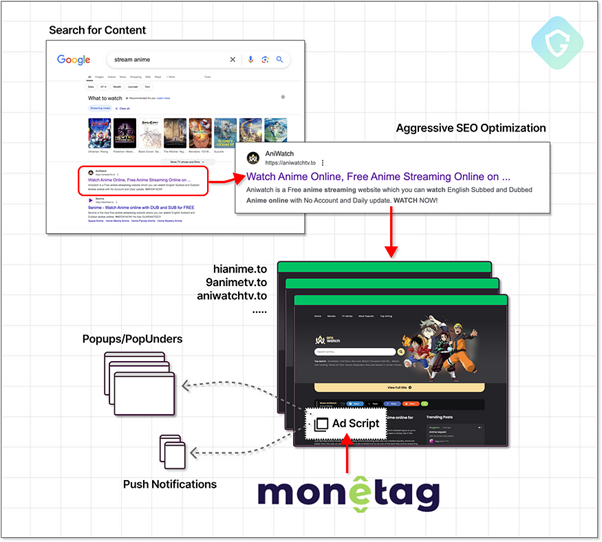
This campaign primarily targets users visiting websites offering free or pirated content, such as streaming platforms and download hubs. These sites, known for aggressive advertising practices, become unwitting participants in the attack.
In some cases, compromised websites or cloned templates are used to spread these fake captcha scripts further, increasing the scale of the infection.
According to the Labs Guard in Medium, Sophisticated search engine optimization (SEO) tactics ensure these malicious websites rank highly on search engines, attracting a steady stream of unsuspecting visitors.
Once on the site, users are funneled into the fake captcha attack flow through intrusive ad placements.
To safeguard against these threats, users must adopt proactive security practices. Avoid clicking on pop-ups or captcha prompts that seem suspicious or lead to unexpected actions.
Using reputable ad blockers can minimize exposure to malvertising while keeping your operating system and antivirus software updated can help detect and prevent malware execution.
Finally, stay vigilant when browsing high-risk websites, especially those offering free or pirated content.
Investigate Real-World Malicious Links, Malware & Phishing Attacks With ANY.RUN – Try for Free



