A hacker operating under the alias “Satanic” has claimed responsibility for a massive data breach involving WooCommerce, a leading e-commerce platform used globally to power online stores.
The breach, allegedly carried out on April 6, 2025, has reportedly compromised sensitive data of over 4.4 million users.
The claim surfaced on Breach Forums, a notorious hub for cybercriminal activities, where “Satanic” disclosed details of the stolen database.
Interestingly, the hacker clarified that the data wasn’t extracted from WooCommerce’s core infrastructure but rather from systems associated with websites utilizing the platform.
This statement points to the exploitation of vulnerabilities in third-party integrations such as customer relationship management (CRM) tools or marketing automation systems.
Details of the Stolen Data
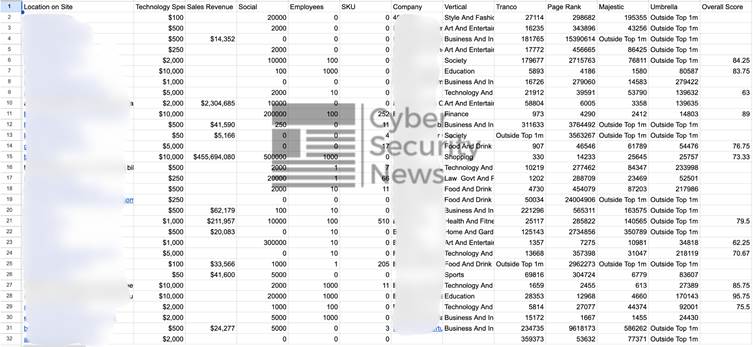
The leaked database encompasses a wide range of information, raising alarms about its potential misuse. Specifically, the stolen records include:
- Customer Information: Detailed personal data, such as email addresses, phone numbers, physical addresses, and social media profiles of over 4.4 million users.
- Company Metadata: Business-related details, including sales revenue, employee counts, domain authority rankings, and the technology stacks used by affected organizations.
- Unique Identifiers: 1.3 million unique email addresses and 998,000 unique phone numbers are among the data exposed.

Notably, sample data accessed by Cyber Security News indicates that several prominent organizations are included in the breach, intensifying the potential consequences.
WooCommerce, developed by Automattic, powers more than 36% of online stores globally, making it the most popular eCommerce platform.
Its open-source nature enables significant customization and integration with other tools, which has contributed to its widespread adoption. However, this breach emphasizes the security risks tied to third-party extensions and integrations.
Security experts warn WooCommerce users to promptly review their third-party integrations for vulnerabilities or unusual data access activity.
Businesses relying on CRM or marketing tools connected to WooCommerce are particularly advised to enhance monitoring and protect sensitive customer data.
Hacker’s Motives and WooCommerce’s Silence
The hacker, “Satanic,” has a history of claiming responsibility for high-profile breaches, including recent incidents involving Magento and Twilio’s SendGrid.
While Twilio denied those claims, the sheer scale of the WooCommerce breach—if verified—could rank as one of the largest WordPress-related exposures of the year.
As of now, WooCommerce has not released an official statement addressing the claims.
Meanwhile, “Satanic” is reportedly offering the database for sale privately via Telegram and direct messages, with no fixed price, indicating a willingness to negotiate with potential buyers.
This breach serves as yet another reminder of the persistent cybersecurity challenges faced by eCommerce platforms, particularly those relying on open ecosystems and extensive third-party integrations.
Businesses must adopt a proactive approach to securing their systems, leveraging best practices like regular vulnerability assessments and data encryption.
Woocommerce Response
The Woo team was able to quickly look at the data referenced in these stories and compare it against our own data. We have confirmed that this data was not obtained in a breach of WooCommerce.com or any other Automattic service or site. Based on our investigation, it appears the data is from a service that aggregates publicly accessible data about ecommerce stores and other websites in order to resell it. We are not sure how the data was obtained: whether it was legally downloaded through the service or via other means.
Find this News Interesting! Follow us on Google News, LinkedIn, & X to Get Instant Updates!



.png
)
