Chinese state-sponsored hacking group targets India and Hong Kong with a unique phishing attack designed to convince the target.
The campaign uses multiple documents with the filename ‘Mail security check’ and “Boris Johnson Pledges to Admit 3 Million From Hong Kong” in the attack.
The document with the name ‘Mail security check’ targets India and the document with “Boris Johnson Pledges to Admit 3 Million From Hong Kong” targeting Hongkong.
According to Malwarebytes analysis, this new campaign is operated by a Chinese state-sponsored actor, who has been active since at least 2014.
Spear-Phishing to Install MgBot Malware
The campaigns found to be active since July 2, in the first campaign attacker group uses the Cobalt Strike variant delivered through a weaponized word document.
A day after the first attack the APT group changed their template to drop, a loader called MgBot that make use of Application Management (AppMgmt) Service on Windows to deliver the final payload.

The campaigns targeting Hong Kong spotted On July 5, the email includes, “with an embedded document borrowing a statement about Hong Kong from UK’s prime minister Boris Johnson.”

The MgBot malware includes four files which two of them are in Chinese Simplified language, which indicates the campaign is operated from China.
The malware includes several anti-analysis and anti-virtualization techniques to make analysis harder and tries to avoid running in a known virtualized environment.
Also, the malware checks for the presence of security products on the victim’s machine, if present them it alters the execution flow.
According to Malwarebytes analysis, the APT group several IP addresses for its C2 communications, and most of the IP addresses are located in Hong Kong.
Android RAT
Researchers found “found several malicious Android applications we believe are part of the toolset used by this APT group.”
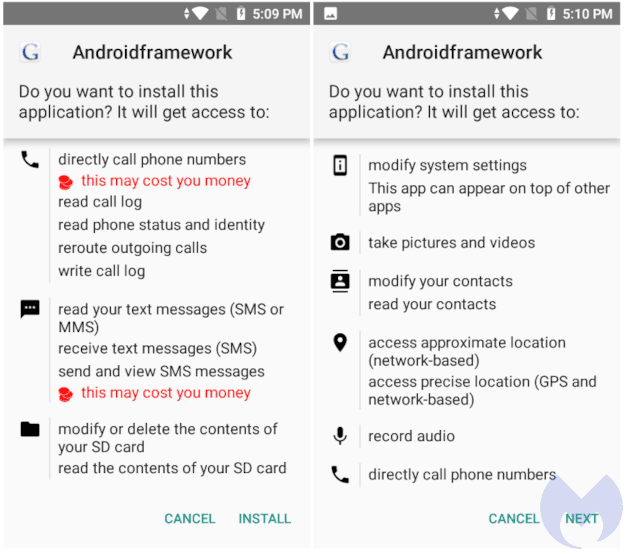
The malicious application includes following RAT functionalities;
- Recording screen and audio using the phone’s camera/mic
- Locating phone with coordinates
- Stealing phone contacts, call log, SMS, web history
- Sending SMS messages
The RAT communicates with a range of IP addresses between 122.10.89.170 to 179, all of them located in Hong Kong.
“The lures used in this campaign indicate that the threat actor may be targeting the Indian government and individuals in Hong Kong, or at least those who are against the new security law issued by China.”
You can follow us on Linkedin, Twitter, Facebook for daily Cybersecurity, and hacking news updates.
Also Read
Digital Strike!! India Banned 59 Chinese Apps Including TikTok, UC Browser, SHAREit
Chinese Bank Forced Companies Doing Business in China to install Malware Embed Tax Software



.png
)
