Experts at Wiz Research have identified a publicly exposed ClickHouse database belonging to DeepSeek, a Chinese AI startup renowned for its innovative models.
The vulnerability granted full control over database operations, exposing sensitive information such as chat history, secret keys, backend details, and over a million lines of log streams.
The issue was responsibly disclosed to DeepSeek, and the company has since secured the database.
DeepSeek has been under the spotlight recently due to its cutting-edge AI models, particularly the DeepSeek-R1 reasoning model.
The model has been touted as a major rival to systems like OpenAI’s o1, excelling in performance, cost-effectiveness, and efficiency.
As the company’s stature grew, the Wiz Research team prioritized examining its external security posture to identify vulnerabilities—ultimately discovering this serious lapse.
A Publicly Accessible ClickHouse Database
During their investigation, Wiz Research found the ClickHouse database hosted at two accessible endpoints:
- http://oauth2callback.deepseek.com:9000
- http://dev.deepseek.com:9000
Despite its immense importance, the database was completely open, requiring no authentication whatsoever.
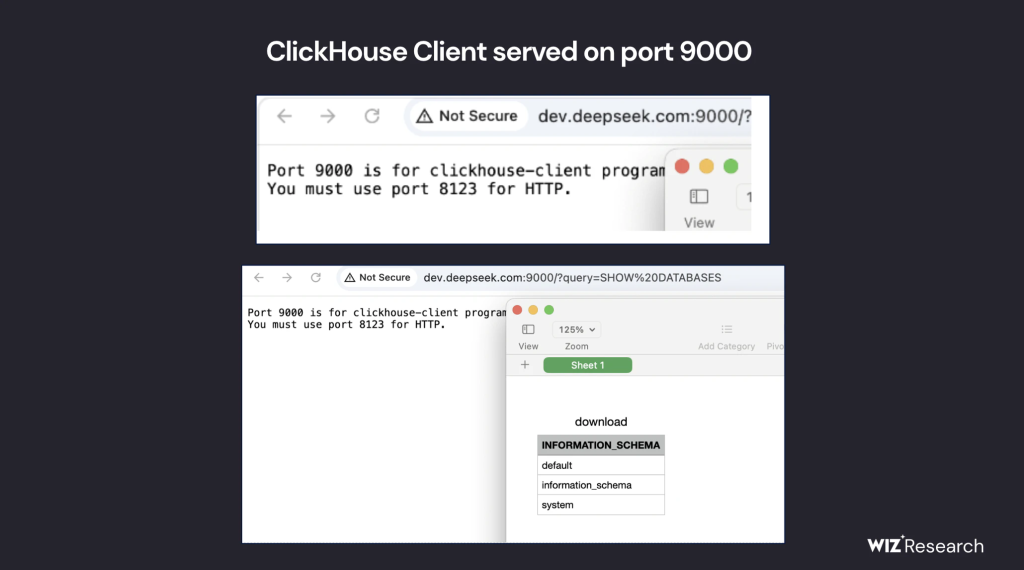
The exposed ClickHouse environment allowed not only unrestricted access but also the potential for privilege escalation across DeepSeek’s internal systems.
What Was Exposed?
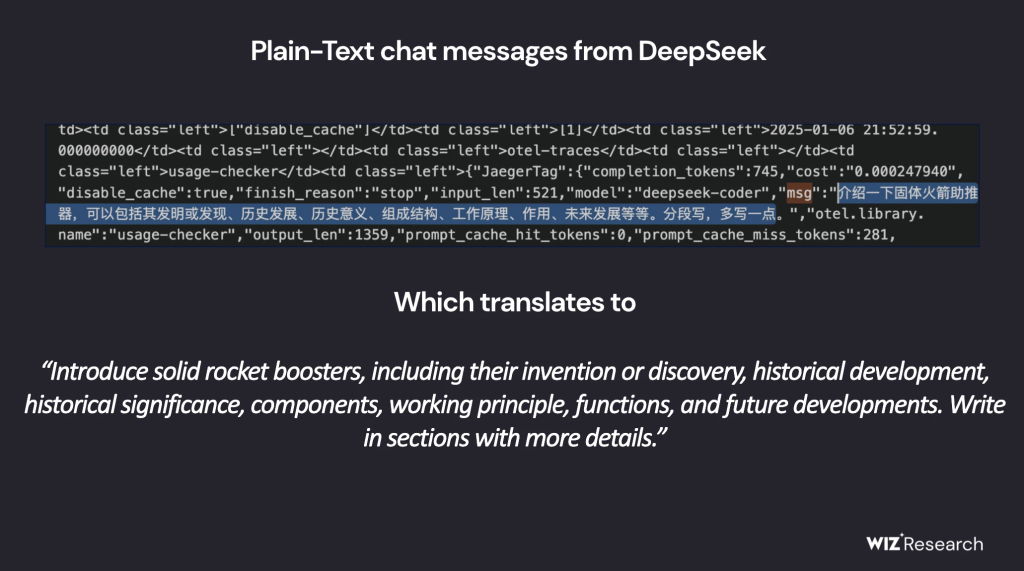
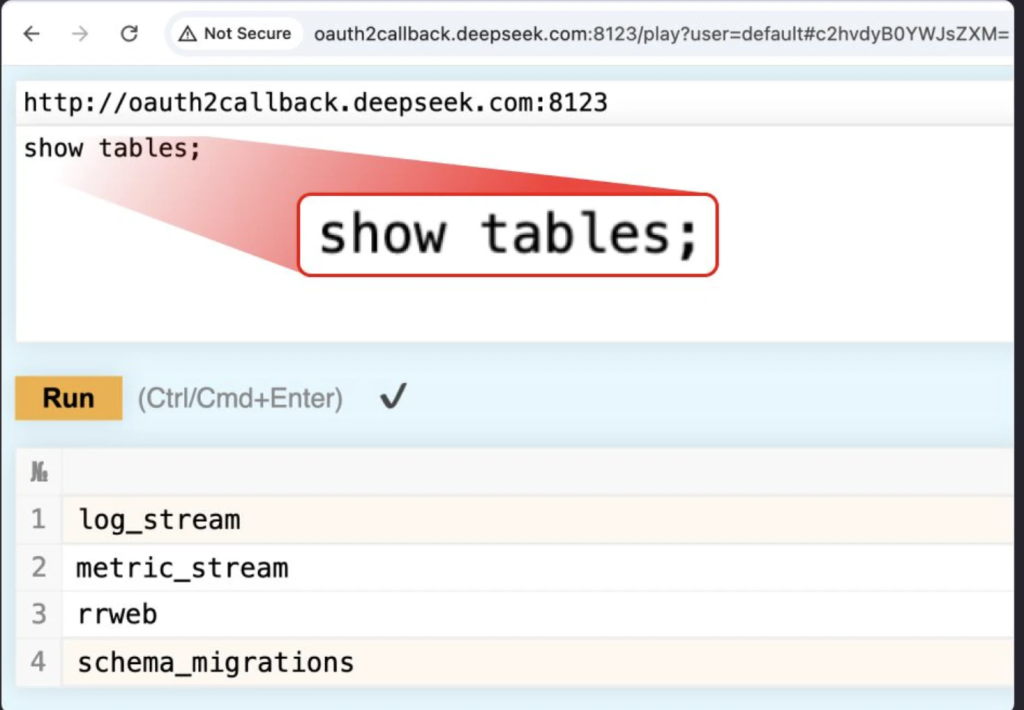
The exposed database included a massive treasure trove of sensitive data, with a critical table named log_stream standing out. This table alone contained over one million log entries with revealing data, including:
- Timestamps: Logs dating back to January 6, 2025.
- API Secrets & Keys: Plaintext API keys and backend operational details.
- Chat History: Logs of customer interactions and metadata.
- Internal Service Metadata: Information about services generating the logs.
- File Details: Possible access to proprietary files and plaintext passwords.
The exposure posed not only a risk to DeepSeek’s infrastructure but also to the privacy and security of its end-users.
ClickHouse, a popular open-source database used for real-time data processing and analytics, is powerful yet vulnerable to misconfigurations.
The /play path within ClickHouse’s HTTP interface allowed arbitrary SQL queries to be executed directly via a browser. With a query as simple as SHOW TABLES, the Wiz team gained access to the database structure.
Queries could even exfiltrate sensitive files depending on ClickHouse’s configuration.
This breach is a stark reminder for organizations leveraging powerful tools like ClickHouse. Misconfigurations can leave critical infrastructure exposed, opening doors for attackers.
The need for robust security mechanisms, such as authentication, role-based access control, and regular audits, cannot be overstated.
Upon being informed by Wiz Research, DeepSeek acted swiftly to secure the exposed database. While the immediate threat has been mitigated, this incident highlights the ever-present risks inherent in managing large-scale AI systems and data.
The DeepSeek database exposure underlines a critical call to action for companies worldwide: as systems become more powerful and interconnected, robust security must be the foundation of every operation.
Collect Threat Intelligence with TI Lookup to improve your company’s security - Get 50 Free Request



.png
)

