A critical remote code execution vulnerability that resides in the DHCP client allows attackers to take control of the system by sending malicious DHCP reply packets.
A Dynamic Host Configuration Protocol (DHCP) Client allows a device to act as a host requesting-configuration parameter, such as an IP address from a DHCP server and the DHCP client can be configured on Ethernet interfaces.
In order to join a client to the network, the packer required to have all the TCP/IP configuration information during DHCP Offer and DHCP Ack.

DHCP protocol works as a client-server model, and it is responsible to dynamically allocate the IP address if the user connects with internet also the DHCP server will be responsible for distributing the IP address to the DHCP client.
This vulnerability will execution the remote code on the system that connected with vulnerable DHCP client that tries to connect with a rogue DHCP server.
Vulnerability Details
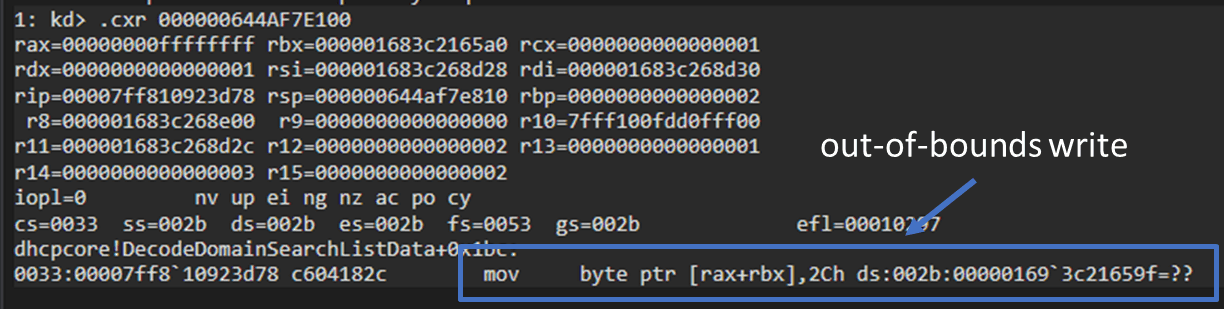
The remote code execution vulnerability exactly resides in the function of dhcpcore.dll called “DecodeDomainSearchListData” which is responsible for decodes the encoded search list option field value.
During the decoding process, the length of the decoded domain name list will be calculated by the function and allocate the memory and copy the decoded list.
According to McAfee research, A malicious user can create an encoded search list, such that when DecodeDomainSearchListData function decodes, the resulting length is zero. This will lead to heapalloc with zero memory, resulting in an out-of-bound write.
The vulnerability has been patched, and it can be tracked as CVE-2019-0547, The patch includes a check which ensures the size argument to HeapAlloc is not zero. If zero, the function exits.
You can follow us on Linkedin, Twitter, Facebook for daily Cybersecurity updates also you can take the Best Cybersecurity course online to keep yourself updated.



